
ConnectWise ScreenConnect 23.9.8 Advisory Alert: Tool for Vulnerability Check
Reading Time: 2 minsEfficiently confirm and address ConnectWise ScreenConnect vulnerabilities with our guide and user-friendly tool.
Already have an account? Sign in
Sign in
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 2 minsEfficiently confirm and address ConnectWise ScreenConnect vulnerabilities with our guide and user-friendly tool.

Reading Time: 7 minsLockBit takedown news and guidance: arrests made, resilience shown, and future cybersecurity steps.
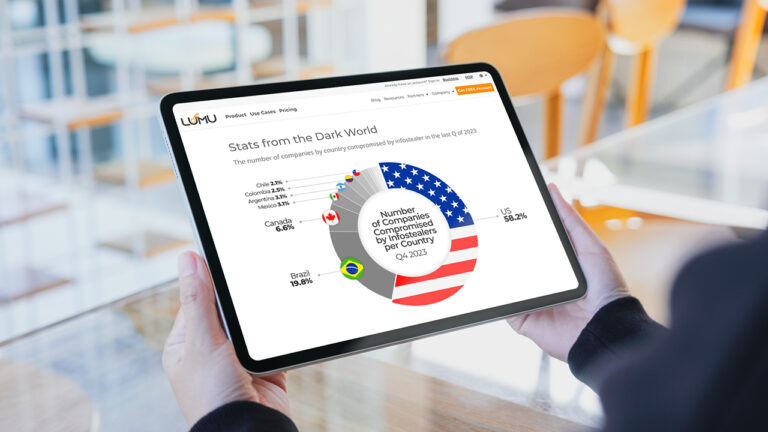
Reading Time: 7 minsExplore how infostealers compromise global security, silently stealing data and offering adversaries Initial Access to networks.

Reading Time: 5 minsLumu’s threat intelligence team has identified a new Advanced Persistent Threat (APT) actor named ‘Copode 1.0’, leveraging the LockBit Black code leaks for cyberattacks. This emerging threat underlines the need for stringent security practices and Lumu’s real-time monitoring offers an efficient response to such evolving challenges.

Reading Time: 3 minsThe recently discovered MOVEit vulnerability is an actively exploited zero-day threat, which is leading to significant breaches in large and critical enterprises. Gain insight into the nature of this vulnerability, its exploitation by the CL0P Ransomware Group, who is at risk, and the necessary remedial measures to be taken.
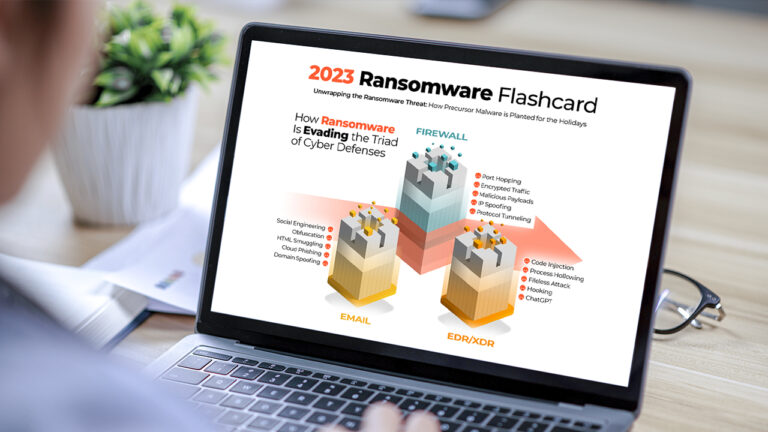
Reading Time: 3 minsExplore the key insights and trends from our 2023 Ransomware Infographic Flashcard. Learn about how hackers are evading defenses, the precursor malware they use, and ransomware’s devastating impact.

Reading Time: 6 minsClop Ransomware is currently being unleashed in a blitz of attacks against organizations across the globe. To help you stay informed and safeguard your organization, Cristian Torres has prepared a detailed analysis examining this emerging threat.

Reading Time: 8 minsThe Manufacturing industry is targeted by ransomware more than any other industry in the USA. Take a look at the motivations and opportunities driving threat actor activity in this critical vertical.

Reading Time: 2 minsThere’s a lot of information available about ransomware, but most of what exists focuses on how to prevent ransomware rather than what to do when ransomware hits. Our latest ransomware incident response playbook details comprehensive defense and response strategies against ransomware.

Reading Time: 5 minsLumu CTO Jeffrey Wheat takes a look at the factors placing pressure on financial sector cybersecurity teams and how automation can be the key to relieving this pressure.

Reading Time: 4 minsThe Conti Ransomware Group has recently unleashed a series of attacks on nations including Costa Rica, resulting in the declaration of a state of emergency. The key to their success is the network of alliances that they have built with precursor malware operators.
Reading Time: 2 minsIn 2021 Lumu grew from strength to strength—in every metric. Here’s our Year in Review with all the unmissable highlights from the year of experience-based growth.
Reading Time: 2 minsThe Log4j vulnerability (designated as CVE-2021-44228 by MITRE) affects 1000’s of software applications. Here are some quick facts and how Lumu helps.

Reading Time: 5 minsRansomware is always preceded by signs that can be identified and stopped. Learn about ransomware chains and their weakest links.

Reading Time: 2 minsThe monetization of cybercrime has diversified while deep web credential market activity has been accelerating. Here’s why that’s serious.