Already have an account? Sign in
Sign in
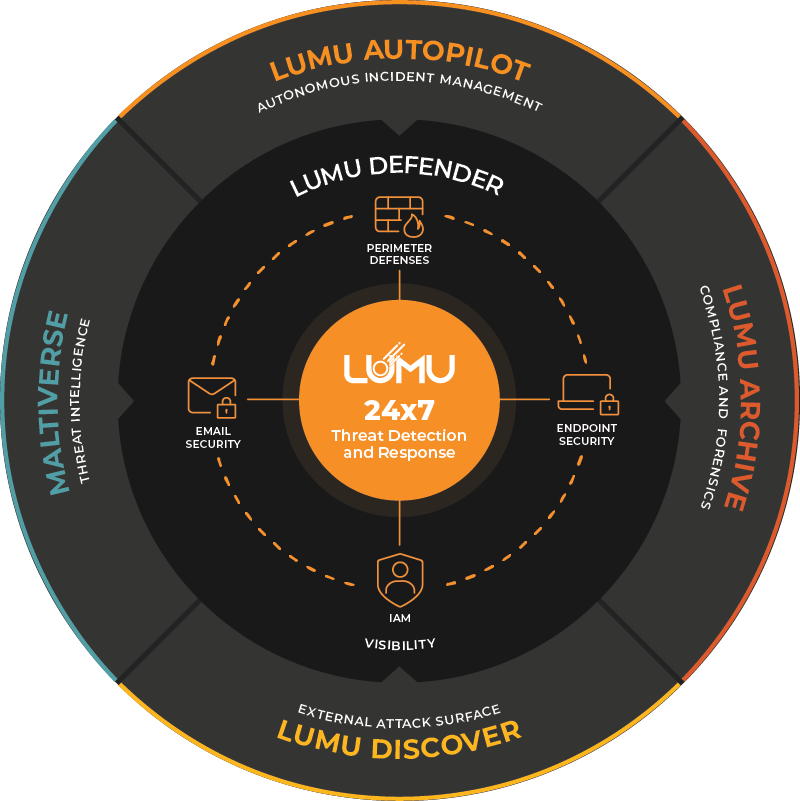
Lumu’s Threat Detection and Response is the core of your security ecosystem. Provides complete visibility across network, endpoint, identity, and cloud while seamlessly integrating with existing cybersecurity defenses to automate threat response.
Schools are now the primary objective for cybercrime in the USA. Attackers are taking advantage of the chaos of student traffic to get into your network.
AsyncRAT is an adaptable open-source Trojan that has evolved into a global threat. We look at how it works and the best way to defend against it.
To defeat the adversary in 2026, you must understand their toolkit. We analyzed the threat horizon and dissected global data to help you make key decisions. This report shows you exactly where to prioritize your defense.
Schools are under growing pressure to defend against modern cyber threats. See how Lumu defends schools 24/7, securing sensitive data and keeping classrooms running without disruption.
This session provides a hands-on look at how Lumu Discover helps security teams stay ahead of targeted threats.
Our team bypasses Microsoft Defender in just minutes, demonstrating the vulnerabilities present in all EDR solutions.

EDUCATION

Director of Technology
“Working with the engineers from Lumu was incredibly helpful and easy. We deployed the app to all of our Chromebooks, through our Google workspace”
Watch Interview
EDUCATION

Information Systems Director
“Think of a security stack as a stack of Swiss cheese pieces: each piece provides defense, but each one of those layers has holes in it. If a threat gets through, Lumu catches that.”
Watch Interview
EDUCATION

IT Director
“Lumu gives us faster detection and less guesswork. We are not cybersecurity experts so we need something like Lumu to partner with us and do the things that we can’t.”
Watch Interview
EDUCATION

Technology and Facilities Director
“It paired really nicely with our Checkpoint firewall and our CrowdStrike. That interoperability oftentimes doesn’t happen. And so Lumu really makes these other tools that we were using better.”
Watch Interview
EDUCATION

Systems Administration Manager
“The Lumu dashboard provides visibility into all of the different traffic coming from those integrated parts and pieces, so that you don’t have to spend time opening different locations.”
Watch Interview
EDUCATION

Director of information Services
“Even though we had our security stack in place, those solutions had some gaps. [When we installed Lumu we were seeing some command and control and malware on the servers.”
Watch Interview
EDUCATION

Director of Technology
“The ability to see into what our 10,000 Chromebooks are doing is important. The agent provided by Lumu gives us that ability.”
Watch Interview
CONSTRUCTION

Security Engineer
“Lumu is that guy that’s up 24 hours looking at the threats, looking at the data, and if action is necessary, they raise the alert, hook into your integrations, and do it all for you.”
Watch Interview
BANKING

SVP, Senior Technology Officer
“Lumu catches the things that make it past our other defences. It’s kind of scary – if we didn’t have Lumu, what would we not be seeing?”
Watch Interview
FINANCIAL

Head of Cybersecurity
“Lumu identifies what is failing, against whom you are failing, and how to respond to that failure. Nothing else in the market does this.”
Watch Interview
FINANCIAL

CISO
“Lumu can even see things before my endpoint protection. This is spectacular because I don’t need to activate an endpoint response plan, because I’ve dealt with it before it’s happened.”
Watch Interview
FINANCIAL

Cybersecurity Manager
“Lumu gives you all the information you need to precisely act in a timely manner”
Watch Interview
STATE & LOCAL GOVERNMENT

Chief Information Officer
“Lumu is making actionable decisions in real-time based on information it’s ingesting from our network, it integrates with our firewall and response happens within seconds.”
Watch Interview
STATE & LOCAL GOVERNMENT

Information Security Officer
“Lumu’s automated response is next generational, we’re not up all night watching monitors to see what’s going on.”
Watch Interview
HEALTHCARE

IT Coordinator
“It gives me those tools that I need to be able to protect my patient information in a way that HIPAA is is satisfied with and of course if HIPAA is satisfied with it then I’m satisfied with it.”
Watch Interview
MSP

Cloud / Security Specialist
“Lumu has been fantastic in it’s flexibility around deployment for different customers.”
Watch Interview
MSP

CEO
“When Lumu sees compromise it will integrate with your other products to automatically block those threats.”
Watch Interview
MSP

Systems Engineer
“Lumu helped us narrow down response efforts to a malicious incident with a client by showing us what happened, seeing which user it involved, the specific IP and device so we could quickly reach out to our client and let them know what was going on.“
Watch Interview
MSP

IT Consultant
“Lumu helps us understand which tools we need in our cyber-stack and whether or not they are actually working.”
Watch Interview
GOVERNMENT

Network Security Analyst
“We previously used a SIEM that complicated things, Lumu gives us clear information we can decisively act on.“
Watch Interview
HEALTHCARE

Director, Information Technology
“We installed Lumu and within two months we were able to detect a serious threat, the quick turnaround from Lumu to notify us allowed us to close up that threat as quickly as possible and stop a possible bad breach to our Network.”
Watch Interview
HOSPITALITY

IT Director
“Lumu is easy to install. Since we don’t have a full time cybersecurity person on staff, Lumu has become our virtual cybersecurity analyst.”
Watch Interview
EDUCATION

Director of Technology
“Working with the engineers from Lumu was incredibly helpful and easy. We deployed the app to all of our Chromebooks, through our Google workspace”
Watch Interview
EDUCATION

Information Systems Director
“Think of a security stack as a stack of Swiss cheese pieces: each piece provides defense, but each one of those layers has holes in it. If a threat gets through, Lumu catches that.”
Watch Interview
EDUCATION

IT Director
“Lumu gives us faster detection and less guesswork. We are not cybersecurity experts so we need something like Lumu to partner with us and do the things that we can’t.”
Watch Interview
EDUCATION

Technology and Facilities Director
“It paired really nicely with our Checkpoint firewall and our CrowdStrike. That interoperability oftentimes doesn’t happen. And so Lumu really makes these other tools that we were using better.”
Watch Interview
EDUCATION

Systems Administration Manager
“The Lumu dashboard provides visibility into all of the different traffic coming from those integrated parts and pieces, so that you don’t have to spend time opening different locations.”
Watch Interview
EDUCATION

Director of information Services
“Even though we had our security stack in place, those solutions had some gaps. [When we installed Lumu we were seeing some command and control and malware on the servers.”
Watch Interview
EDUCATION

Director of Technology
“The ability to see into what our 10,000 Chromebooks are doing is important. The agent provided by Lumu gives us that ability.”
Watch Interview
CONSTRUCTION

Security Engineer
“Lumu is that guy that’s up 24 hours looking at the threats, looking at the data, and if action is necessary, they raise the alert, hook into your integrations, and do it all for you.”
Watch Interview
BANKING

SVP, Senior Technology Officer
“Lumu catches the things that make it past our other defences. It’s kind of scary – if we didn’t have Lumu, what would we not be seeing?”
Watch Interview
FINANCIAL

Head of Cybersecurity
“Lumu identifies what is failing, against whom you are failing, and how to respond to that failure. Nothing else in the market does this.”
Watch Interview
FINANCIAL

CISO
“Lumu can even see things before my endpoint protection. This is spectacular because I don’t need to activate an endpoint response plan, because I’ve dealt with it before it’s happened.”
Watch Interview
FINANCIAL

Cybersecurity Manager
“Lumu gives you all the information you need to precisely act in a timely manner”
Watch Interview
STATE & LOCAL GOVERNMENT

Chief Information Officer
“Lumu is making actionable decisions in real-time based on information it’s ingesting from our network, it integrates with our firewall and response happens within seconds.”
Watch Interview
STATE & LOCAL GOVERNMENT

Information Security Officer
“Lumu’s automated response is next generational, we’re not up all night watching monitors to see what’s going on.”
Watch Interview
HEALTHCARE

IT Coordinator
“It gives me those tools that I need to be able to protect my patient information in a way that HIPAA is is satisfied with and of course if HIPAA is satisfied with it then I’m satisfied with it.”
Watch Interview
MSP

Cloud / Security Specialist
“Lumu has been fantastic in it’s flexibility around deployment for different customers.”
Watch Interview
MSP

CEO
“When Lumu sees compromise it will integrate with your other products to automatically block those threats.”
Watch Interview
MSP

Systems Engineer
“Lumu helped us narrow down response efforts to a malicious incident with a client by showing us what happened, seeing which user it involved, the specific IP and device so we could quickly reach out to our client and let them know what was going on.“
Watch Interview
MSP

IT Consultant
“Lumu helps us understand which tools we need in our cyber-stack and whether or not they are actually working.”
Watch Interview
GOVERNMENT

Network Security Analyst
“We previously used a SIEM that complicated things, Lumu gives us clear information we can decisively act on.“
Watch Interview
HEALTHCARE

Director, Information Technology
“We installed Lumu and within two months we were able to detect a serious threat, the quick turnaround from Lumu to notify us allowed us to close up that threat as quickly as possible and stop a possible bad breach to our Network.”
Watch Interview
HOSPITALITY

IT Director
“Lumu is easy to install. Since we don’t have a full time cybersecurity person on staff, Lumu has become our virtual cybersecurity analyst.”
Watch Interview
EDUCATION

Director of Technology
“Working with the engineers from Lumu was incredibly helpful and easy. We deployed the app to all of our Chromebooks, through our Google workspace”
Watch Interview
EDUCATION

Information Systems Director
“Think of a security stack as a stack of Swiss cheese pieces: each piece provides defense, but each one of those layers has holes in it. If a threat gets through, Lumu catches that.”
Watch Interview