
How to Turn MISP from a Compliance Burden into Active Defense
Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Already have an account? Sign in
Sign in

Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Reading Time: 4 minsThe Education sector is the number one global cyber target. It is clearer than ever that manual defense is failing. We look at how to automate detection and response and win the battle.
Reading Time: 5 minsContact is not compromise. True proactivity means prioritizing rapid response not blindly relying on prevention
Reading Time: 6 minsAsyncRAT is an adaptable open-source Trojan that has evolved into a global threat. We look at how it works and the best way to defend against it.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 4 minsDiscover the top insights from Lumu’s pre-conference workshop at IT Nation Connect, where MSP leaders shared actionable advice on building effective cybersecurity stacks, pricing services, and managing client success

Reading Time: 2 minsAs we move into 2025, AI-driven evasion and autonomous threats will redefine cybersecurity, pushing organizations to adapt to new risks and defense tactics.

Reading Time: 7 minsEndpoint Detection and Response (EDR) has a critical role in most companies’ security setup, but cybercriminals are mastering EDR bypass tactics. How can we defend against them?
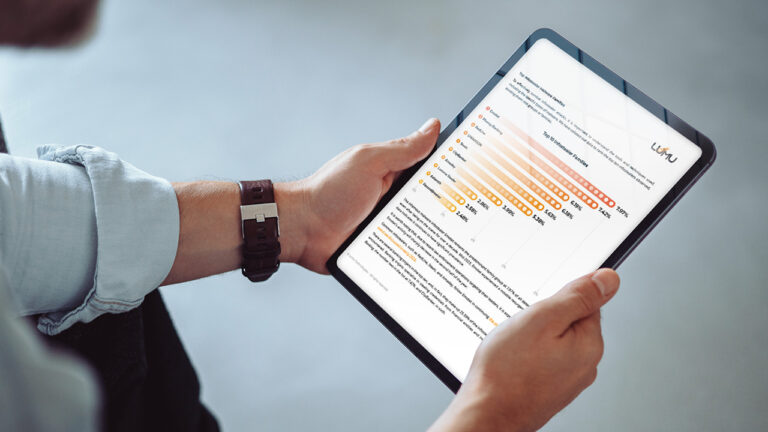
Reading Time: 5 minsLumu’s Compromise Report for 2024 uncovers surprising information about how infostealer malware has increasingly targeted US organizations, local government, and education establishments.

Reading Time: 4 minsFor MSPs to proactively protect their clients they need good intelligence, such as the trends and tendencies in cyber threats revealed in the Lumu Compromise Report 2024.
Reading Time: 6 minsExplore DPI’s limitations in network security and discover how Lumu’s cloud-native, metadata-driven approach provides essential visibility and threat detection.

Reading Time: 3 minsLumu’s new Compromise Report 2024 reveals the greatest current cybersecurity trends and how to defend against them. We look at the top three takeaways to watch out for in the report.

Reading Time: 6 minsDiscover how Lumu’s Playback feature improves visibility and efficiency while addressing the limitations of traditional SIEMs in handling vast amounts of network data.
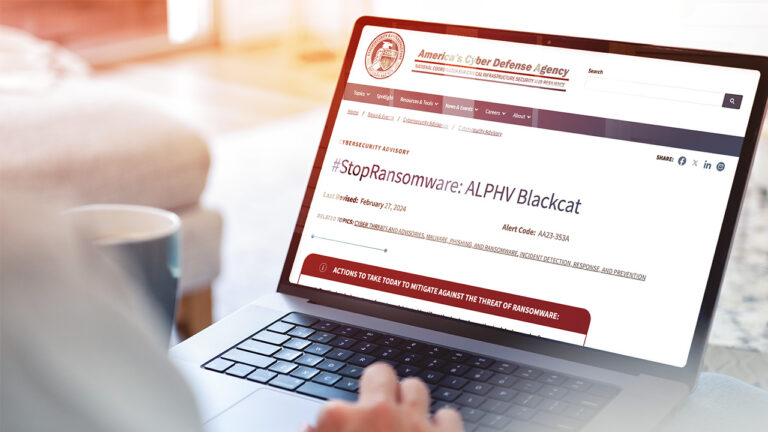
Reading Time: 4 minsRansomHub is a new ransomware group offering Ransomware as a Service that has already encrypted and exfiltrated data from at least 210 victims. How does RansomHub bypass defenses and how can you defend against it?
Reading Time: 7 minsMario Lobo, Cybersecurity Specialist at Lumu Technologies, recently attended DEFCON – a hacker convention held annually in Las Vegas, Nevada – and he highlights his big takeaways.

Reading Time: 4 minsWe are incredibly excited to share that Lumu has been recognized as one of the best Network Detection and Response (NDR) solutions for the second year running in the GigaOm Radar for NDRs.
Reading Time: 3 minsLearn how Lumu helps MSPs meet CIS compliance with real-time malware detection, network defense, and automated incident response.

Reading Time: 3 minsLearn about the recent CrowdStrike outage affecting Microsoft devices, its impact, recovery steps, and how Lumu can help ensure continued network security.

Reading Time: 4 minsEssential cybersecurity tips to safeguard K-12 schools during the back-to-school season.

Reading Time: 3 minsExplore the Snowflake supply chain attack, how infostealer malware impacted hundreds of major companies, and essential measures to protect your organization from similar threats