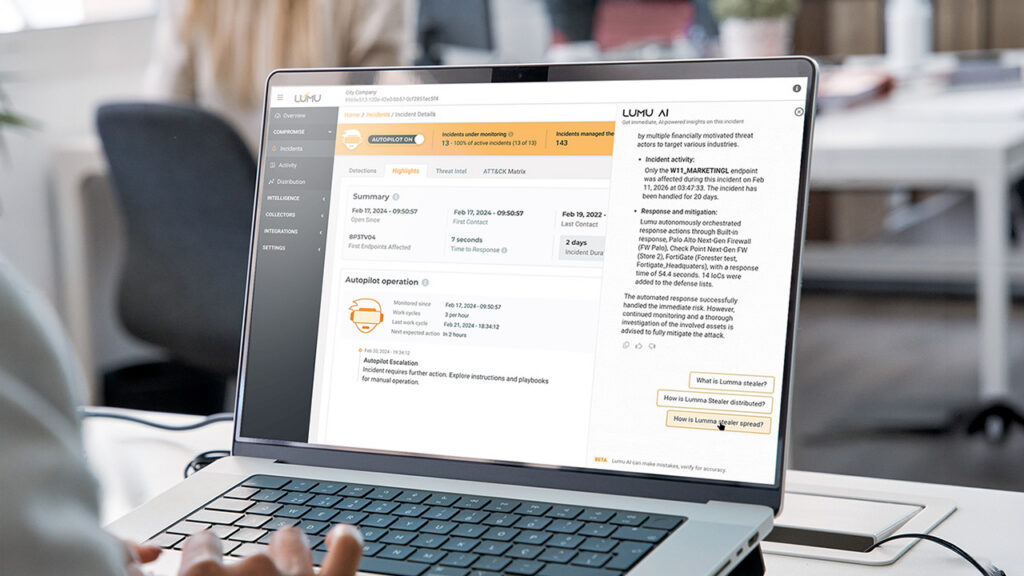
How Lumu AI Delivers Autonomous Defense and Instant Analyst Insights
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Already have an account? Sign in
Sign in
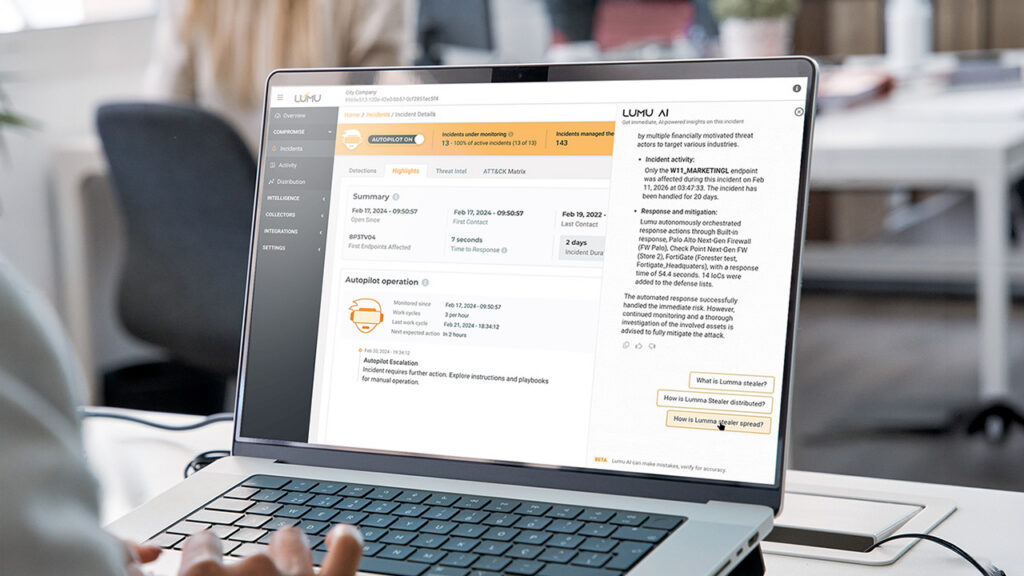
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Reading Time: 7 minsSummer break is a high-risk period in cybersecurity for schools. Discover practical cybersecurity solutions for how to secure school networks over the summer.
Reading Time: 6 minsEmpower your school’s cyber stack by securing 1:1 Chromebooks. Learn how network detection provides the visibility needed to stop threats early.
Reading Time: 7 minsHow does the 2026 Remcos RAT bypass your security to stream live surveillance? Understand the latest campaign and how to protect your enterprise.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 6 minsFresh from DEFCON 33, Lumu’s Mario Lobo identifies a revolutionary shift in AI-driven attacks that is changing the rules for cyber defenders and their tools.

Reading Time: 4 minsTo defend against threats, organizations must use a structured cyber threat intelligence lifecycle. This turns knowledge about attackers into timely, decisive action.

Reading Time: 3 minsAs security professionals, we hear about mitigation and remediation on a daily basis. However, these are terms that are commonly confused with each other.
Reading Time: 6 minsBumbleBee malware facilitates severe attacks like ransomware or data theft. Threat intelligence shows increasing deployment across key industries and locations.

Reading Time: 5 minsAs a new school year begins, cybersecurity for K-12 is more critical than ever. Let’s explore top tips on how to prepare.

Reading Time: 4 minsA supply chain cyberattack on C&M Software has impacted Brazilian financial institutions. Learn about the incident, its implications, and how to protect your organization from similar third-party risks.

Reading Time: 5 minsIn response to global cyber threats, a new White House executive order prioritizes network visibility to strengthen national cybersecurity. Why is network visibility important for your organization?

Reading Time: 8 minsA current ClickFix campaign has compromised over 260,000 websites, turning trusted platforms into malware delivery systems that steal login credentials, cryptocurrency wallets, and personal data. Explore the full attack chain, from initial compromise to final payload, and see why this campaign poses a serious threat to U.S. organizations.

Reading Time: 5 minsLumma Stealer cyber threat resurfaces despite recent takedown. Discover the malware’s resurgence and learn how to protect your systems.

Reading Time: 7 minsDefense against zero day attacks requires constant vigilance and meticulous preparation, and Lumu should be an essential component of your strategy.

Reading Time: 4 minsAs global cybersecurity event, RSAC 2025, wraps for another year, Ricardo Villadiego, CEO of Lumu Technologies, reflects on the pulse of the cybersecurity industry.

Reading Time: 4 minsIntroducing the Lumu SecOps Platform, a fully integrated platform that brings together detection, response, automation, compliance, and threat intelligence. One platform, one experience, full context.

Reading Time: 5 minsA surge in malicious activity is targeting ConnectWise ScreenConnect. Attackers are attackers are misusing clients and exploiting vulnerabilities, posing a significant threat to organizations.

Reading Time: 5 minsCybercrime in the education sector is having a field day while educational institutions are suffering at the hands of cybercriminals. We look at some of the stats and reasons behind this worrying trend.

Reading Time: 3 minsThe recent Akira ransomware attack, which exploited a vulnerable webcam to bypass EDR, underscores the critical need for organizations to adopt a Zero Trust architecture and continuous network monitoring.