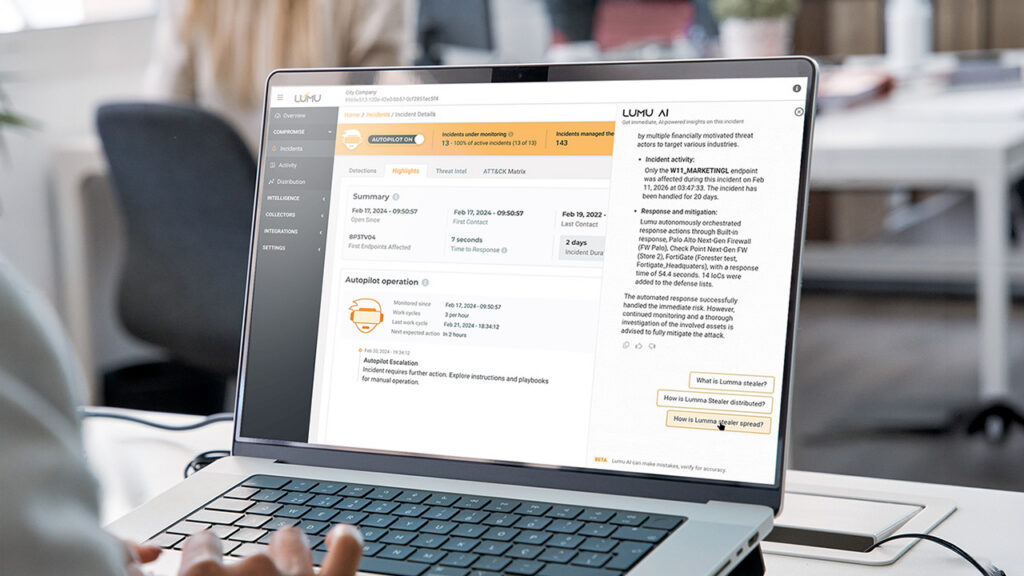
How Lumu AI Delivers Autonomous Defense and Instant Analyst Insights
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Already have an account? Sign in
Sign in
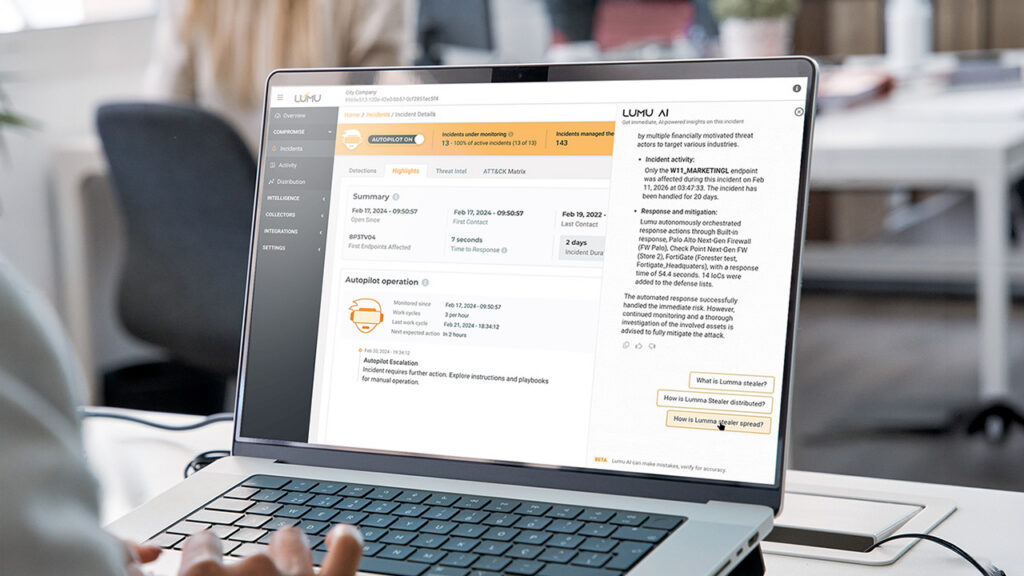
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Reading Time: 7 minsSummer break is a high-risk period in cybersecurity for schools. Discover practical cybersecurity solutions for how to secure school networks over the summer.
Reading Time: 6 minsEmpower your school’s cyber stack by securing 1:1 Chromebooks. Learn how network detection provides the visibility needed to stop threats early.
Reading Time: 7 minsHow does the 2026 Remcos RAT bypass your security to stream live surveillance? Understand the latest campaign and how to protect your enterprise.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 10 minsThis technical deep-dive analyzes a sophisticated Amadey Stealer campaign leveraging Living-off-the-Land tactics and defense evasion, identified through Lumu’s network behavior analysis.

Reading Time: 6 minsWe have entered a new ‘Age of Adaptation’. The enemy is becoming more difficult to stop at the gate. We need to shift from reliance on perimeter defenses to continuous, real-time assessment.

Reading Time: 4 mins For cybersecurity operators, Large Language Models (LLMs) provide many potential uses. To help you maximize their value, here are 10 suggested cybersecurity prompts for anyone in the space to pose to their favorite AI chatbot.

Reading Time: 5 minsDeathRansom ransomware has evolved, hiding in malicious PDFs to bypass defenses. It does not break down the door. It is invited in.
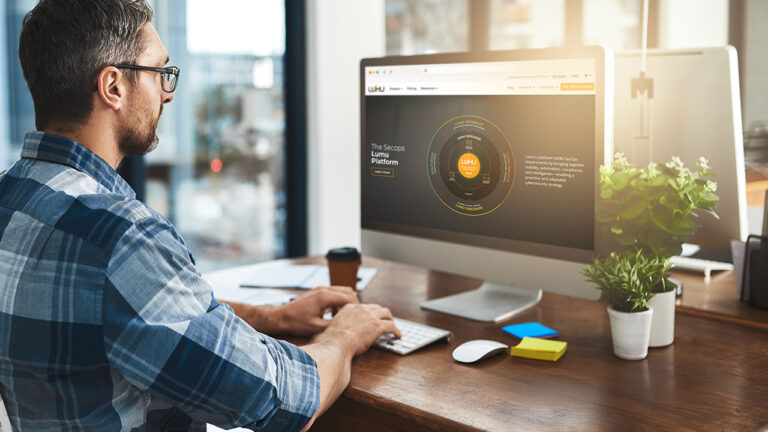
Reading Time: 5 minsThis year’s Lumu 2025 Product Recap highlights our commitment to simplifying SecOps and leading cybersecurity transformation. Key milestones include the launch of the unified Lumu SecOps Platform, the acquisition of Maltiverse to deepen threat intelligence, and significant advancements across our product suite.

Reading Time: 5 minsYour security stack is built on trusting domain reputation scores. But attackers now weaponize malicious domain detection methods against you.

Reading Time: 4 minsHow autonomous attacks, AI supply chain compromise, and geopolitical cybercrime will render traditional SOCs and endpoint security obsolete, requiring the establishment of a new viable “truth layer” capable of inferring intent in an environment.

Reading Time: 3 minsHow autonomous attacks, AI supply chain compromise, and geopolitical cybercrime will render traditional SOCs and endpoint security obsolete, forcing a move to a new truth layer.

Reading Time: 6 minsOur analysis of APT-C-36, Blind Eagle, breaks down how a regional phishing attack becomes a global supply chain threat, providing insights for your proactive defense.
Reading Time: 5 minsEmbracing remote work creates BYOD security challenges. Learn to secure the personal laptops and phones connecting to your network and protect your business.

Reading Time: 4 minsBy integrating generative AI with Lumu Defender’s carefully curated threat data, you can create a powerful virtual analyst. This guide shows how to use this to deliver faster and more effective security.

Reading Time: 4 minsThe MSSP model of fast alert response is no longer enough. Success now requires shifting from simple reaction to strategic resilience.

Reading Time: 7 minsGunra ransomware targets critical industries using a strict five-day payment deadline. Learn about Gunra and ransomware detection techniques to fortify your defenses.

Reading Time: 5 minsLearning how to implement Zero Trust is more than just buying tools, you have to ensure they work. Integrating Zero Trust with Lumu gives you the needed visibility.
Reading Time: 6 minsWhat is Sarcoma ransomware? This new double extortion threat both steals sensitive data and encrypting systems. You need to ensure your organization is prepared.