Table of Contents
Qakbot, also known as Qbot, is a type of sophisticated banking Trojan and malware that has been active for several years. It primarily targets Windows-based systems and is designed to steal sensitive financial information, login credentials, and other personal data.
Though it’s known to impact the financial industry, we’ve seen the malware strain evolve and target many other industries. Despite claims of a takedown this past summer, it seems they are just as active as ever.
What We Know
Despite claims by the FBI in the summer, Qakbot was never truly taken down.
Lumu’s position was always that Qakbot never truly halted operations. We’ve been seeing Qakbot impact our customer base even after the takedown was announced in August.
- FBI’s QakBot Takedown: ‘Dismantled’ or Just a Temporary Setback? https://nationalcybersecurity.com/fbis-qakbot-takedown-dismantled-or-just-a-temporary-setback-hacking-cybersecurity-infosec-comptia-pentest-ransomware/
- FBI’s QakBot Takedown Raises Questions: ‘Dismantled’ or Just a Temporary Setback? https://www.infosecurity-magazine.com/news-features/fbi-qakbot-takedown-dismantled/
- Industry Reactions to Qakbot Botnet Disruption: Feedback Friday https://www.securityweek.com/industry-reactions-to-qakbot-botnet-disruption-feedback-friday/
- It might be too soon to claim victory against Qakbot https://www.computerweekly.com/opinion/It-might-be-too-soon-to-claim-victory-against-Qakbot
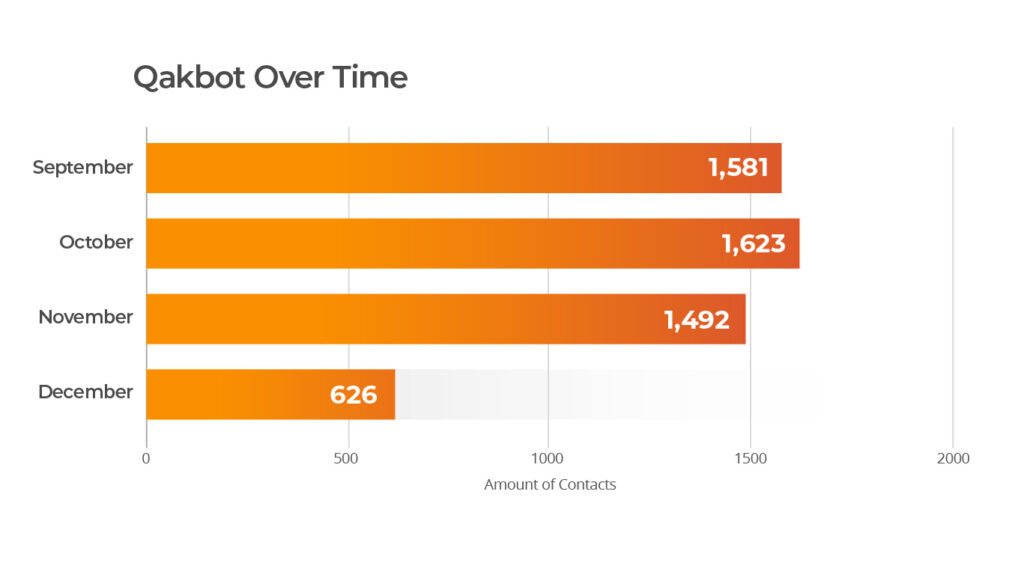
Our customer data suggests that the botnet has been quite active over the last few months, as we’ve detected Qakbot activity impacting various customers at a steady rate. December is not over, but we still see it keeping pace with previous months.
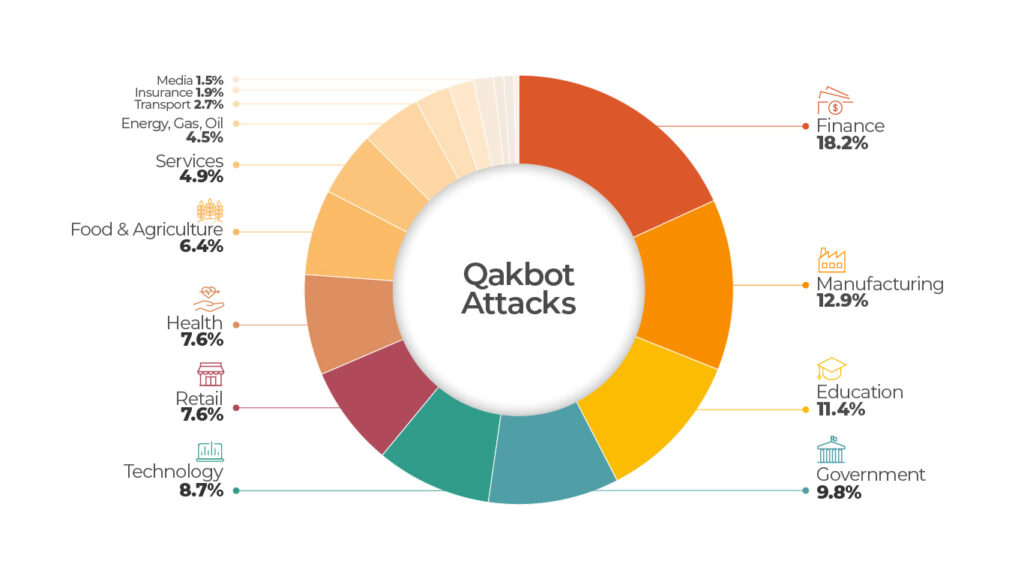
Qakbot seems to be targeting a variety of industries, but Finance, Manufacturing, Education, and Government are the most commonly impacted across our customer base.
Qakbot Returns: Bigger and Better
According to our feeds, the C2 infrastructure was taken down for the most part, however, the people behind the operation are still free. In order to keep the operation they created and deployed a new executable binary, and now apparently they renewed and improved their infrastructure and binaries.
The new Qakbot malware now operates on 64 bit systems, uses AES encryption for its network communications, which enhances its ability to remain undetected and secure its data exfiltration processes. Additionally, it has evolved to send HTTP POST requests to specific paths, a method likely used for its command and control communications or for data exfiltration
Recommendations
- Enhanced Network Monitoring: Deploy Continuous Compromise Assessment to detect any communication with known Qakbot C2 servers. This real-time monitoring can alert you to potential breaches or malware activity.
- Incident Response Planning: Have a robust incident response plan in place. Lumu’s incident management feature can aid in quickly identifying and mitigating threats.
- SecOps Enablement: Leverage SecOps capabilities to actively monitor and respond to threats. Lumu’s platform can provide valuable insights for SecOps teams to act upon.
- Employee Awareness Training: Educate your staff about the risks of phishing emails, which are a common delivery method for Qakbot. Promote vigilance in identifying and reporting suspicious emails.
- Regular Updates and Patching: Ensure that all systems are regularly updated and patched to mitigate vulnerabilities that could be exploited by Qakbot.
- Threat-Informed Defense: Stay informed about the latest developments in Qakbot’s tactics and techniques. Use this information to inform your cybersecurity strategies and defenses.
A critical step in any cybersecurity strategy is establishing visibility into threats that are affecting your network infrastructure. Open a Lumu Free account and start gaining visibility into threats that are evading traditional cybersecurity defenses.




