
Is Your Supply Chain Exposing Your Organization? 4 Security Case Studies
Reading Time: 7 minsNetwork perimeters are no longer static. They grow and shift with third parties, whose credential leaks are now your biggest supply chain vulnerability
Already have an account? Sign in
Sign in

Reading Time: 7 minsNetwork perimeters are no longer static. They grow and shift with third parties, whose credential leaks are now your biggest supply chain vulnerability

Reading Time: 10 minsThis technical deep-dive analyzes a sophisticated Amadey Stealer campaign leveraging Living-off-the-Land tactics and defense evasion, identified through Lumu’s network behavior analysis.

Reading Time: 4 mins For cybersecurity operators, Large Language Models (LLMs) provide many potential uses. To help you maximize their value, here are 10 suggested cybersecurity prompts for anyone in the space to pose to their favorite AI chatbot.

Reading Time: 5 minsYour security stack is built on trusting domain reputation scores. But attackers now weaponize malicious domain detection methods against you.
Reading Time: 6 minsWhat is Sarcoma ransomware? This new double extortion threat both steals sensitive data and encrypting systems. You need to ensure your organization is prepared.

Reading Time: 6 minsFresh from DEFCON 33, Lumu’s Mario Lobo identifies a revolutionary shift in AI-driven attacks that is changing the rules for cyber defenders and their tools.

Reading Time: 4 minsTo defend against threats, organizations must use a structured cyber threat intelligence lifecycle. This turns knowledge about attackers into timely, decisive action.

Reading Time: 4 minsA supply chain cyberattack on C&M Software has impacted Brazilian financial institutions. Learn about the incident, its implications, and how to protect your organization from similar third-party risks.

Reading Time: 5 minsFollowing the release of data from over 15,000 Fortinet devices, what can we do to protect against further compromise?

Reading Time: 4 minsAnonymization, though designed to protect privacy, is increasingly exploited by cybercriminals to mask their origins and identities, complicating the detection and mitigation of attacks.

Reading Time: 7 minsThis is the story of a serious DNS tunneling attack on a multinational insurance provider — discover the importance of DNS tunneling detection, what we found when we investigated the attack, and how we contained it.

Reading Time: 7 minsEndpoint Detection and Response (EDR) has a critical role in most companies’ security setup, but cybercriminals are mastering EDR bypass tactics. How can we defend against them?
Reading Time: 7 minsMario Lobo, Cybersecurity Specialist at Lumu Technologies, recently attended DEFCON – a hacker convention held annually in Las Vegas, Nevada – and he highlights his big takeaways.

Reading Time: 3 minsLearn about the recent CrowdStrike outage affecting Microsoft devices, its impact, recovery steps, and how Lumu can help ensure continued network security.
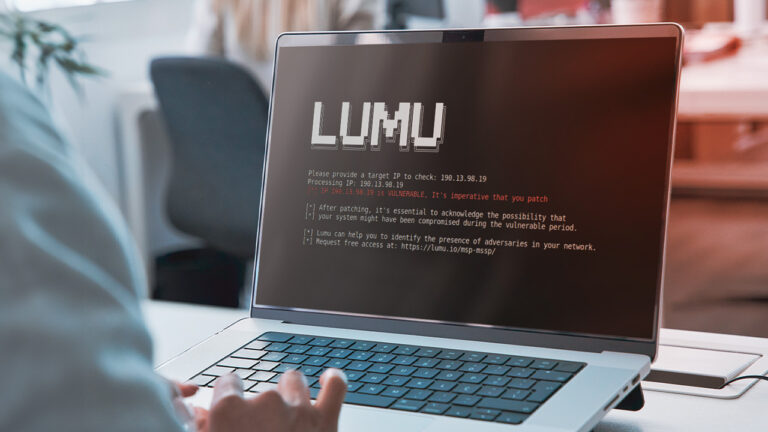
Reading Time: 2 minsThis VPN vulnerability highlights a typical risks associated with perimeter defenses, which can allow attackers to access networks. Stay informed and secure your network promptly.