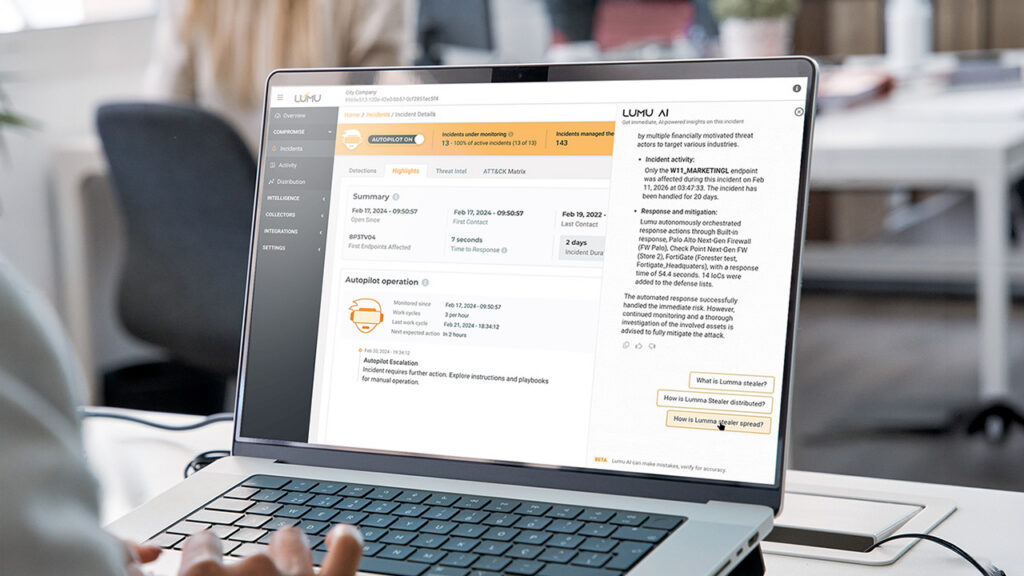
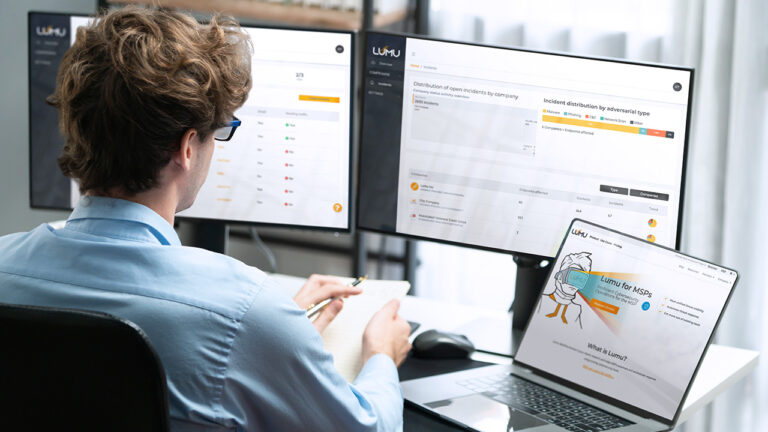
How Lumu AI Delivers Autonomous Defense and Instant Analyst Insights
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Already have an account? Sign in
Sign in
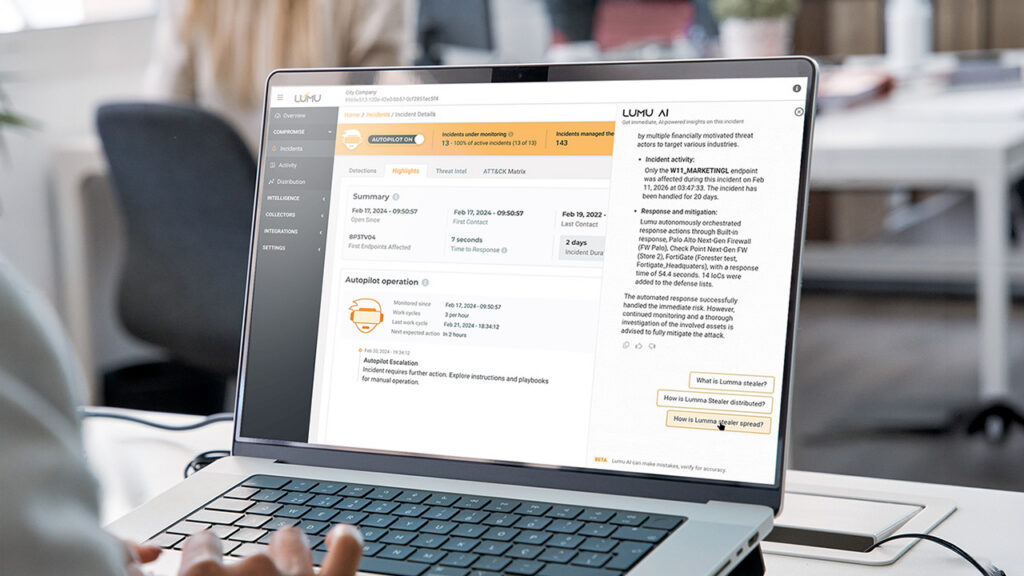
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Reading Time: 7 minsSummer break is a high-risk period in cybersecurity for schools. Discover practical cybersecurity solutions for how to secure school networks over the summer.
Reading Time: 6 minsEmpower your school’s cyber stack by securing 1:1 Chromebooks. Learn how network detection provides the visibility needed to stop threats early.
Reading Time: 7 minsHow does the 2026 Remcos RAT bypass your security to stream live surveillance? Understand the latest campaign and how to protect your enterprise.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 6 minsDiscover how Lumu’s Playback feature improves visibility and efficiency while addressing the limitations of traditional SIEMs in handling vast amounts of network data.
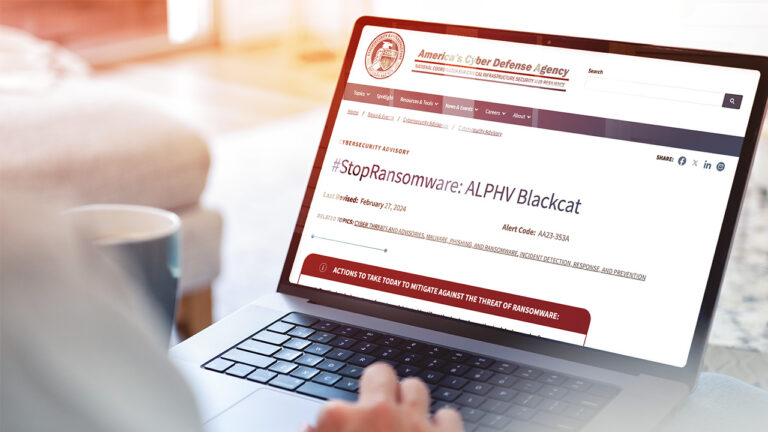
Reading Time: 4 minsRansomHub is a new ransomware group offering Ransomware as a Service that has already encrypted and exfiltrated data from at least 210 victims. How does RansomHub bypass defenses and how can you defend against it?
Reading Time: 7 minsMario Lobo, Cybersecurity Specialist at Lumu Technologies, recently attended DEFCON – a hacker convention held annually in Las Vegas, Nevada – and he highlights his big takeaways.

Reading Time: 4 minsWe are incredibly excited to share that Lumu has been recognized as one of the best Network Detection and Response (NDR) solutions for the second year running in the GigaOm Radar for NDRs.
Reading Time: 3 minsLearn how Lumu helps MSPs meet CIS compliance with real-time malware detection, network defense, and automated incident response.

Reading Time: 3 minsLearn about the recent CrowdStrike outage affecting Microsoft devices, its impact, recovery steps, and how Lumu can help ensure continued network security.

Reading Time: 4 minsEssential cybersecurity tips to safeguard K-12 schools during the back-to-school season.

Reading Time: 3 minsExplore the Snowflake supply chain attack, how infostealer malware impacted hundreds of major companies, and essential measures to protect your organization from similar threats

Reading Time: 4 minsPlatformization can limit flexibility and innovation. Discover why an open SecOps Platform is essential for cybersecurity
Reading Time: 2 minsThis VPN vulnerability highlights a typical risks associated with perimeter defenses, which can allow attackers to access networks. Stay informed and secure your network promptly.

Reading Time: 6 minsLocal Government and Education Institutions are under increasing threat from cyber criminals. Explore how these critical sectors can level up their cybersecurity posture.

Reading Time: 4 minsMissed RSA Conference 2024? Explore Lumu CEO and RSAC veteran Ricardo Villadiego’s perspective on the key takeaways from RSAC 2024

Reading Time: 5 minsIntroducing Lumu Autopilot, the latest innovation that delivers on our promise to help the world operate cybersecurity proficiently.

Reading Time: 4 minsThe Palo Alto Networks PAN-OS firewall vulnerability exemplifies critical flaws in traditional perimeter defenses. Understand how Lumu’s detection capabilities safeguard networks.

Reading Time: 2 minsEfficiently confirm and address ConnectWise ScreenConnect vulnerabilities with our guide and user-friendly tool.