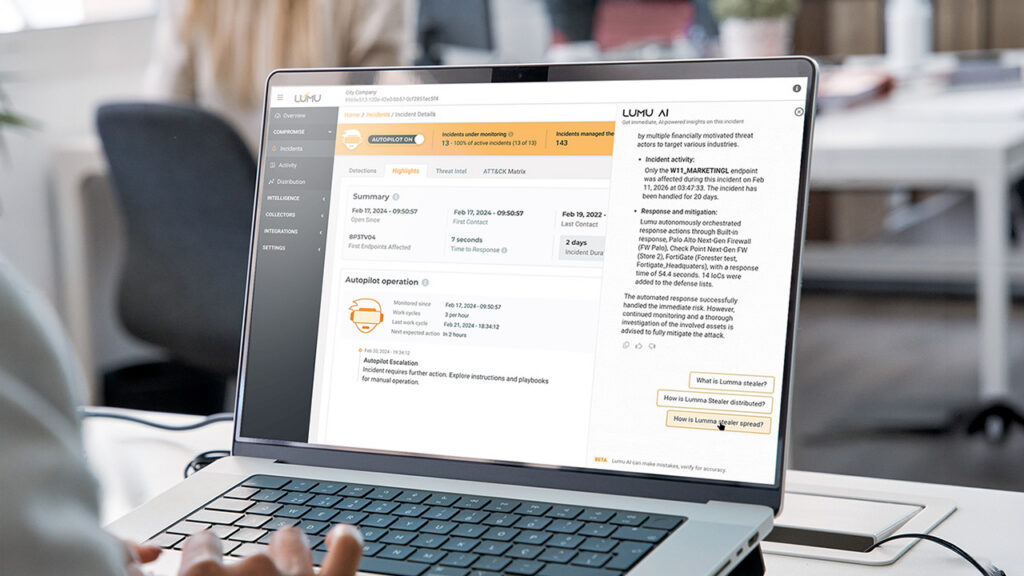
How Lumu AI Delivers Autonomous Defense and Instant Analyst Insights
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Already have an account? Sign in
Sign in
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Reading Time: 7 minsSummer break is a high-risk period in cybersecurity for schools. Discover practical cybersecurity solutions for how to secure school networks over the summer.
Reading Time: 6 minsEmpower your school’s cyber stack by securing 1:1 Chromebooks. Learn how network detection provides the visibility needed to stop threats early.
Reading Time: 7 minsHow does the 2026 Remcos RAT bypass your security to stream live surveillance? Understand the latest campaign and how to protect your enterprise.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 4 minsDr. Chase Cunningham gives some insight into why he decided to head Lumu’s CISO Advisory Board.

Reading Time: 6 minsMSP Burnout is reaching critical levels. Luckily, online communities have some solid advice.

Reading Time: 4 minsManaged Service Providers are feeling the effects of MSP burnout and cybersecurity is a big culprit, but cybersecurity can also provide relief.

Reading Time: 3 minsHere are a few simple steps that startups and small businesses can take to implement a strong cybersecurity practice leveraging existing resources.

Reading Time: 5 minsLumu CTO Jeffrey Wheat takes a look at the factors placing pressure on financial sector cybersecurity teams and how automation can be the key to relieving this pressure.

Reading Time: 4 minsThe new Lumu Incident View is a single screen that places at the cybersecurity operator’s fingertips the tools and information that they need to outwit cybercriminals at every turn.

Reading Time: 4 minsThe Conti Ransomware Group has recently unleashed a series of attacks on nations including Costa Rica, resulting in the declaration of a state of emergency. The key to their success is the network of alliances that they have built with precursor malware operators.

Reading Time: 4 minsAfter numerous conversations with customers Nicole Ibarra, Lumu’s Director of Product Marketing, reports back on her findings.

Reading Time: 3 minsCybersecurity operations can be hard but are needed in all businesses. EMA Research Director Chris Steffen shares how MSPs and MSSPs can help small and medium-sized businesses operate cybersecurity proficiently.
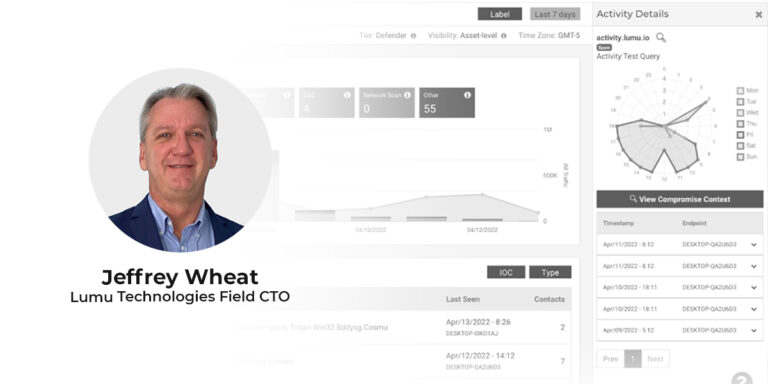
Reading Time: 4 minsLumu’s recently appointed Field CTO Jeffrey Wheat looks at the future of the SOC and how incremental improvement leads to proficient operations. Beginning his cybersecurity career at the department of defense, Jeffrey Wheat is a proven leader and CISSP with 30 years of experience spanning SOC management at international firms as well as cybersecurity architecture design and implementation.
Reading Time: 4 minsIn April of 2022, it seems that cybersecurity is more unsettled than ever. Here are the top questions we’ve been receiving about cybersecurity and emerging cyber threats

Reading Time: 3 minsTrends from 2021 indicate that 2022 will see an increased threat of ransomware on a global level. Here are some insights and background information to accompany the facts and figures provided by our Ransomware Flashcard 2022.

Reading Time: 3 minsLumu Free just got a major upgrade. We’ve included more metadata collectors, giving you greater network visibility and more closely reflecting our vision of how cybersecurity needs to be operated.
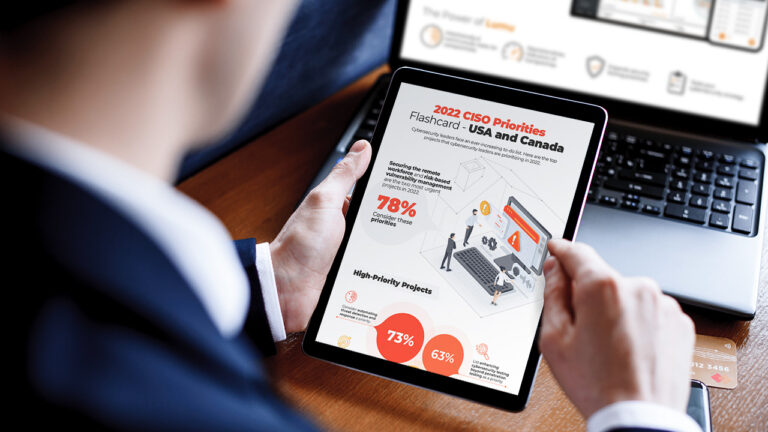
Reading Time: 2 minsWe polled over 300 CISOs from across the Americas on the cybersecurity challenges they’re prioritizing in 2022. Gain insight into the key projects, emerging priorities, and deprioritized secondary initiatives—despite high risks.
Reading Time: 2 minsIn 2021 Lumu grew from strength to strength—in every metric. Here’s our Year in Review with all the unmissable highlights from the year of experience-based growth.