The Tactics, Techniques, and Procedures (TTPs) used by threat actors are always evolving. Recently, Ransomware attacks are making use of more traditional malware to gain a foothold in an enterprise, and Malware Delivery as a Service is evolving to meet this demand.
The general trend is that adversaries are specializing in relatively small parts of the cyber kill chain. By doing so they can refine their TTPs, make their attacks harder to detect, and open up business opportunities previously hidden, such as selling access to already compromised networks. This is the division of labor, explained by Adam Smith more than 2 centuries ago; now specific criminal groups focus on what they do best.
On top of this, the existence of several commercial and open-source penetration testing tools creates an environment in which setting up an APT (Advanced Persistent Threat) is relatively easy. This has been a further step in the ongoing democratization of malware. Sophisticated TTPs are increasingly available to threat actors without extensive technical knowledge.
Timeline of Events
Starting in April 2019, we can see cooperation between ransomware and malware gradually increasing. This culminated in the latest generation of malware that caters specifically to this symbiotic relationship.
Date | Short description | Reference |
April 2019 | Emotet and trickbot develop the ability to deliver ransomware to an infected system | |
June 2019 | Trojans (qakbot, emotet, rietspoof) are used to move laterally until a domain controller is composed. Megacortex is delivered to the compromised network. | 4. |
Nov 2019 | Dridex trojans can take months to move deeper and compromise domain controllers, before ransomware is delivered. | |
May 2020 | Prolock Ransomware uses qakbot malware as well as remote desktop servers to breach victims. | |
May 2020 | Threat actors shift to using MAZE ransomware post-compromise with IceID, using exfiltrated data to apply greater pressure on targets. | |
June 2020 | Glupteba trojans create backdoors to infected systems, for the purpose of delivering access to other threat actors. | |
July 2020 | Threat group TA505 improves its tools over time, most recently using Get2 to install SDBbot, FlawedGrace, or FlawedAmmyRAT malware to move laterally and deploy CLOP ransomware on the maximum number of systems. Refusal to pay the ransom results in sensitive data being posted on their site “CL0P^_- LEAKS” |
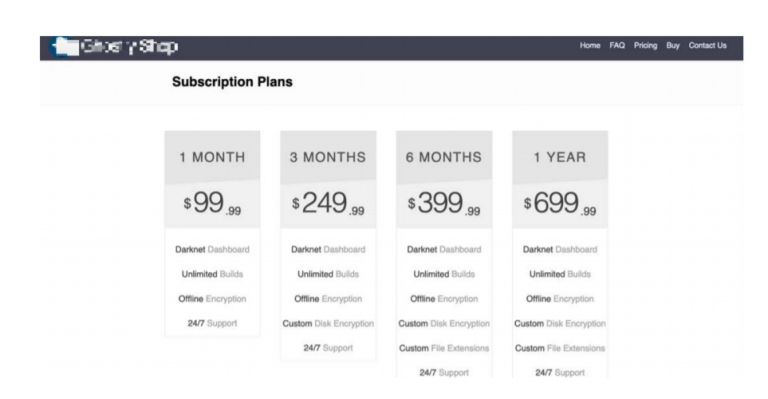
Looking at ransomware attacks from the cybercriminal’s perspective, we can conclude that developing, maintaining, and protecting infrastructure capable of controlling thousands of infected devices around the globe is not an easy task. This is where solutions such as Ransomware-as-a-Service, provides its value. Now even without technical knowledge, anyone can deploy an attack, just by paying a very low price. According to the Trend Micro report Shifts in Underground Markets, the price of Ransomware-as-a-Service starts at US$5 and some popular ones like Crypterlocker around US$100. They also offer subscription plans like those in the image below (and they provide support):
Ransomware-as-a-Service is not new in the security business, and because of that, threats that operate using this methodology are usually detected by most antivirus vendors, making things harder for cybercriminals.
So, how can an attacker bypass security tools and deploy ransomware attacks in corporations these days without any issue? Well, this is what brings Malware Delivery as a Service to life.
Cybercriminals can stop worrying about spam email campaigns or malware packers for hiding attacks from antivirus engines and instead use the infrastructure already compromised by other threat groups with way more experience in avoiding security tools. Using any of the commercial and open-source penetration testing tools available, they can focus on understanding the inner workings of your victim’s infrastructure, identifying the most valuable assets, and deploying attacks directly against them.
Wouldn’t that sound great to an attacker?
This is the new business model gaining more players in the malware scene, allowing new groups to enter this field while optimizing their ROI.
It has never been easier to compromise an organization—even without technical knowledge—hence this is the time to look continuously and intentionally for those compromises.
Malware Compromise Distributions
Lumu has detected increased activity from compromises associated with Malware Delivery as a Service. The below examples from the Lumu portal show compromise context visualizations—including the frequency of adversarial contacts—from these attacks.


If your network infrastructure is communicating with any of these IoCs, be sure to take immediate action. Even the smallest amount of activity could indicate that a ransomware attack is imminent. Above all, it is imperative to continuously and intentionally look for Malware Delivery as a Service compromises, so they can be eliminated before the severity of the breach can be escalated.
To stay up to date on the latest developments, be sure to visit our new Ransomware Resource Center.




