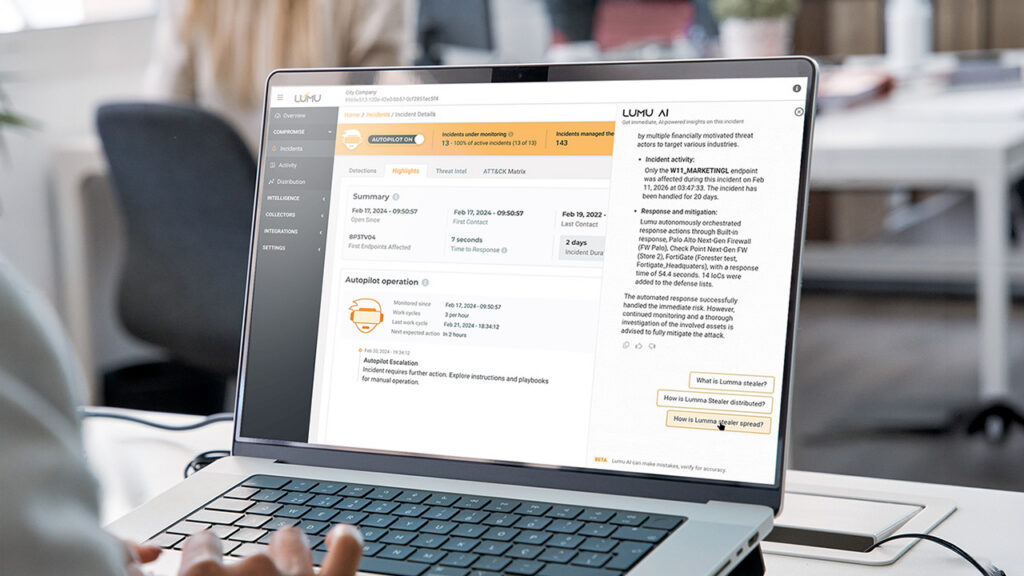
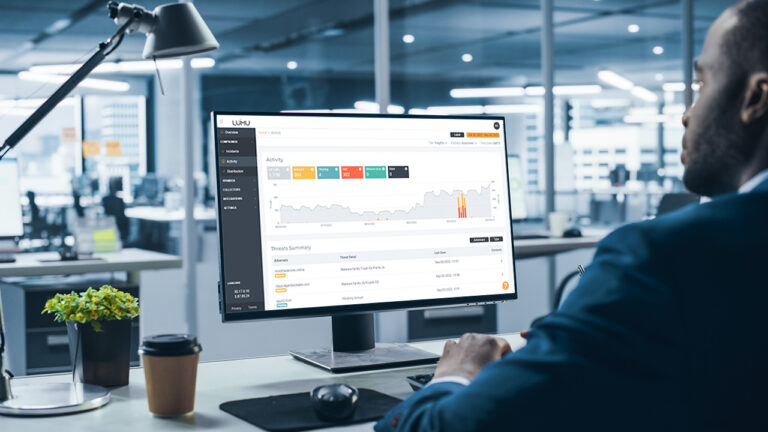
How Lumu AI Delivers Autonomous Defense and Instant Analyst Insights
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Already have an account? Sign in
Sign in
Reading Time: 5 minsLumu uses AI to uncover threats, automate responses, and transform raw telemetry into clear, actionable security insights.
Reading Time: 7 minsSummer break is a high-risk period in cybersecurity for schools. Discover practical cybersecurity solutions for how to secure school networks over the summer.
Reading Time: 6 minsEmpower your school’s cyber stack by securing 1:1 Chromebooks. Learn how network detection provides the visibility needed to stop threats early.
Reading Time: 7 minsHow does the 2026 Remcos RAT bypass your security to stream live surveillance? Understand the latest campaign and how to protect your enterprise.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 2 minsThere’s a lot of information available about ransomware, but most of what exists focuses on how to prevent ransomware rather than what to do when ransomware hits. Our latest ransomware incident response playbook details comprehensive defense and response strategies against ransomware.

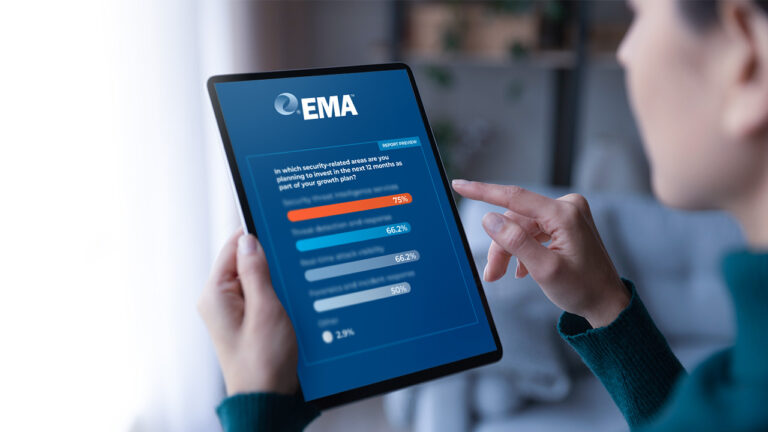
Reading Time: 2 minsWe surveyed 213 U.S. cybersecurity executives on their priorities for the new year. Here’s what their responses tell us about how cybersecurity is evolving amid the recession.
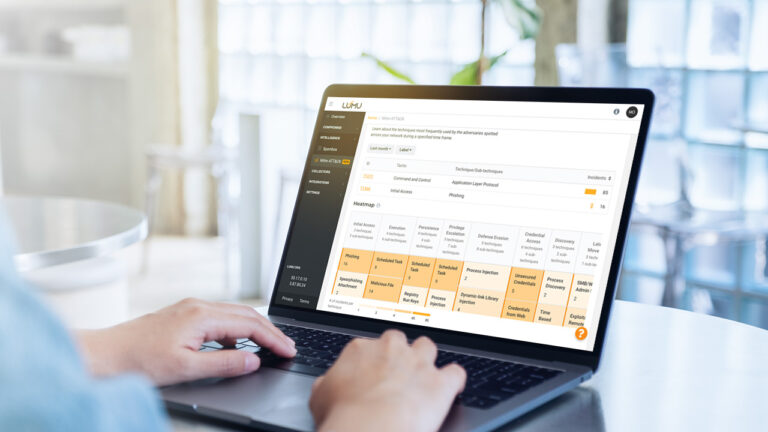
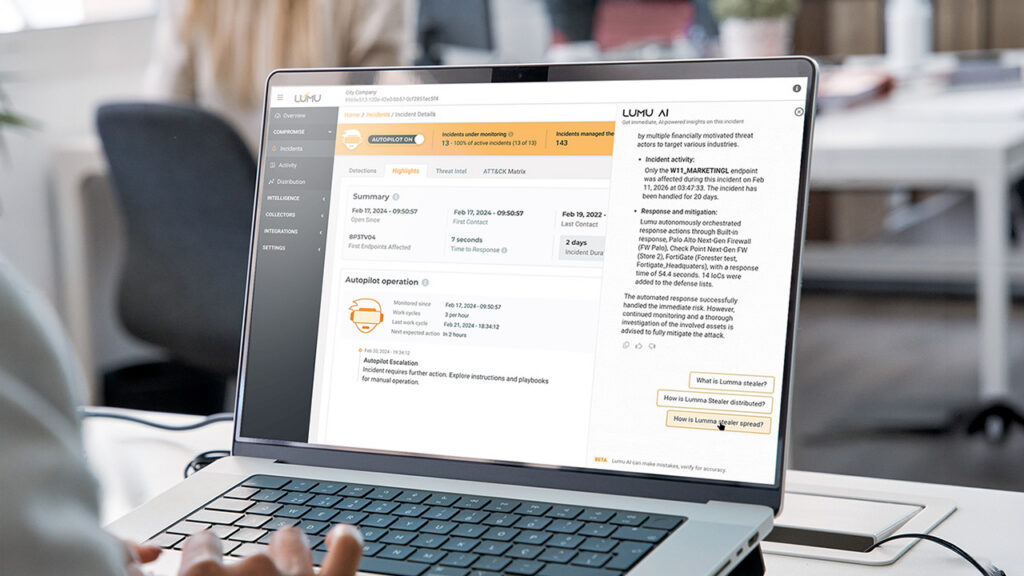
Reading Time: 6 minsThreat-informed defense is a strategic approach to risk-based cybersecurity that even smaller organizations can get up and running easily.

Reading Time: 5 minsCybersecurity Analysts can turn to these 7 habits to complement their cybersecurity strategy and be more efficient.

Reading Time: 3 minsThe 2022 Lumu Product Recap brings together all the Continuous Compromise Assessment Improvements we delivered over the last year.

Reading Time: 2 minsWith cybersecurity evolving at a faster pace than ever, here are some predictions for what to look out for in cybersecurity in 2023.

Reading Time: 3 minsWith cybersecurity evolving at a faster pace than ever, here are some predictions for what to look out for in cybersecurity in 2023.

Reading Time: 4 minsOur CISOs’ Lessons report shares the insights of cybersecurity leaders who have experienced worst-case security breaches. Here’s why we should take heed.

Reading Time: 2 minsAs a partner in Fortinet’s Fabric-Ready Partner Program, Lumu delivers automated attack detection and response across the network. See how to integrate Lumu Defender with Fortinet’s FortiGate NGFW.
Reading Time: 2 minsThe MSP Cybersecurity Market Opportunity Blueprint shows MSPs how they can grow their business through value-added cybersecurity services. SMBs and entrepreneurs understand the need for cybersecurity.
Reading Time: 4 minsLumu Founder and CEO Ricardo Villadiego reflects on how continuous measurement in cybersecurity allows for a swift and effective response.

Reading Time: 4 minsThe recent Biden-Harris administration government represents the biggest current Zero Trust initiative. Dr. Chase Cunningham looks at how this initiative helps states, local entities, and small business entities and how you can apply.

Reading Time: 3 minsDoctor Zero Trust, Chase Cunningham looks at the guiding lights that MSPs can use to navigate the complex and at-times treacherous cybersecurity market.

Reading Time: 2 minsThe Lumu ROI Calculator is a free tool that helps organizations get an idea of the time and money they can save using Lumu. The assessment is designed to enable informed decision-making when it comes to finding the right solution.

Reading Time: 4 minsLumu’s Compromise Flashcard 2022 tells the story of compromise in 2022. Learn how threat actors are targeting companies in different ways and dig deeper into the story told by the statistics.