
How to Turn MISP from a Compliance Burden into Active Defense
Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Already have an account? Sign in
Sign in

Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Reading Time: 4 minsThe Education sector is the number one global cyber target. It is clearer than ever that manual defense is failing. We look at how to automate detection and response and win the battle.
Reading Time: 5 minsContact is not compromise. True proactivity means prioritizing rapid response not blindly relying on prevention
Reading Time: 6 minsAsyncRAT is an adaptable open-source Trojan that has evolved into a global threat. We look at how it works and the best way to defend against it.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 4 minsThis story is based on true events and dives into what happens when initial contact is made with some of the most pervasive strains of

Reading Time: 4 minsRSAC 2023 brought the cybersecurity world together in San Francisco. While there is a general consensus that a paradigm shift is needed in cybersecurity, it is clear that we would be stronger still if there were consensus around what that paradigm shift needs to look like.
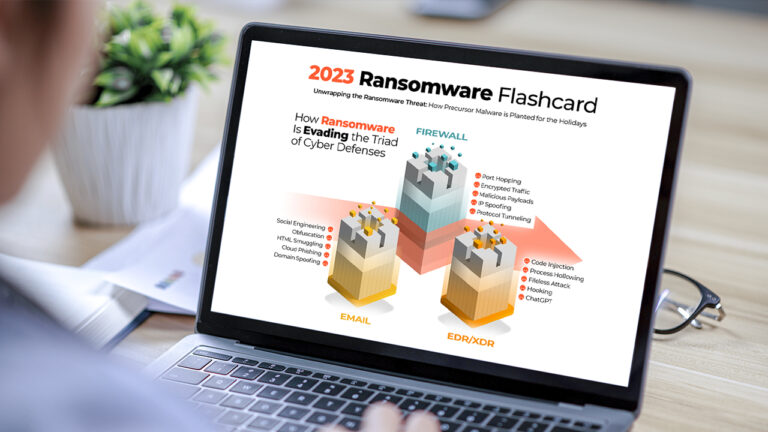
Reading Time: 3 minsExplore the key insights and trends from our 2023 Ransomware Infographic Flashcard. Learn about how hackers are evading defenses, the precursor malware they use, and ransomware’s devastating impact.

Reading Time: 11 minsEDR Evasion includes a suite of techniques that hackers use to elude endpoint defenses. Discover how hackers evade Endpoint Detection and Response (EDR) systems using various techniques. Learn about the common tactics used by cyber attackers to bypass endpoint defenses and how to better protect against these stealthy attacks.

Reading Time: 2 minsOur Threat Intelligence Team has discovered approximately 70,000 instances potentially exposed to a dangerous vulnerability in the 3CX Desktop App currently being exploited by threat actors. Learn how it could impact your company and how to respond in case adversaries leveraged this vulnerability to enter your organization.

Reading Time: 6 minsClop Ransomware is currently being unleashed in a blitz of attacks against organizations across the globe. To help you stay informed and safeguard your organization, Cristian Torres has prepared a detailed analysis examining this emerging threat.

Reading Time: 8 minsThe Manufacturing industry is targeted by ransomware more than any other industry in the USA. Take a look at the motivations and opportunities driving threat actor activity in this critical vertical.

Reading Time: 2 minsThere’s a lot of information available about ransomware, but most of what exists focuses on how to prevent ransomware rather than what to do when ransomware hits. Our latest ransomware incident response playbook details comprehensive defense and response strategies against ransomware.

Reading Time: 2 minsWe surveyed 213 U.S. cybersecurity executives on their priorities for the new year. Here’s what their responses tell us about how cybersecurity is evolving amid the recession.
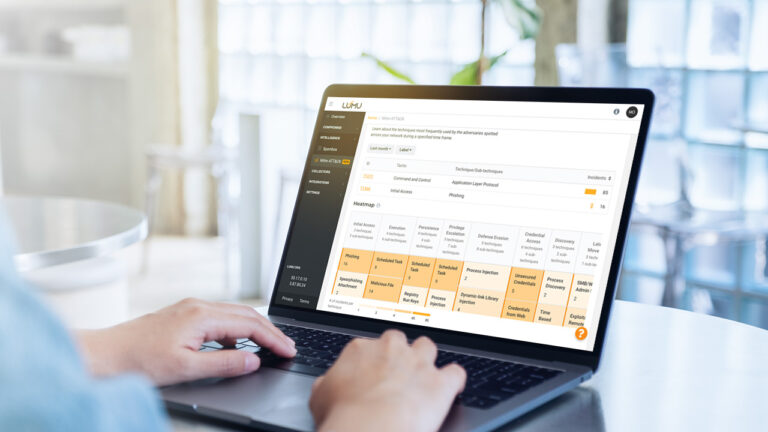
Reading Time: 6 minsThreat-informed defense is a strategic approach to risk-based cybersecurity that even smaller organizations can get up and running easily.

Reading Time: 5 minsCybersecurity Analysts can turn to these 7 habits to complement their cybersecurity strategy and be more efficient.

Reading Time: 3 minsThe 2022 Lumu Product Recap brings together all the Continuous Compromise Assessment Improvements we delivered over the last year.

Reading Time: 2 minsWith cybersecurity evolving at a faster pace than ever, here are some predictions for what to look out for in cybersecurity in 2023.

Reading Time: 3 minsWith cybersecurity evolving at a faster pace than ever, here are some predictions for what to look out for in cybersecurity in 2023.

Reading Time: 4 minsOur CISOs’ Lessons report shares the insights of cybersecurity leaders who have experienced worst-case security breaches. Here’s why we should take heed.