
How to Turn MISP from a Compliance Burden into Active Defense
Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Already have an account? Sign in
Sign in

Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Reading Time: 4 minsThe Education sector is the number one global cyber target. It is clearer than ever that manual defense is failing. We look at how to automate detection and response and win the battle.
Reading Time: 5 minsContact is not compromise. True proactivity means prioritizing rapid response not blindly relying on prevention
Reading Time: 6 minsAsyncRAT is an adaptable open-source Trojan that has evolved into a global threat. We look at how it works and the best way to defend against it.
Get the latest cybersecurity articles and insights straight from the experts.

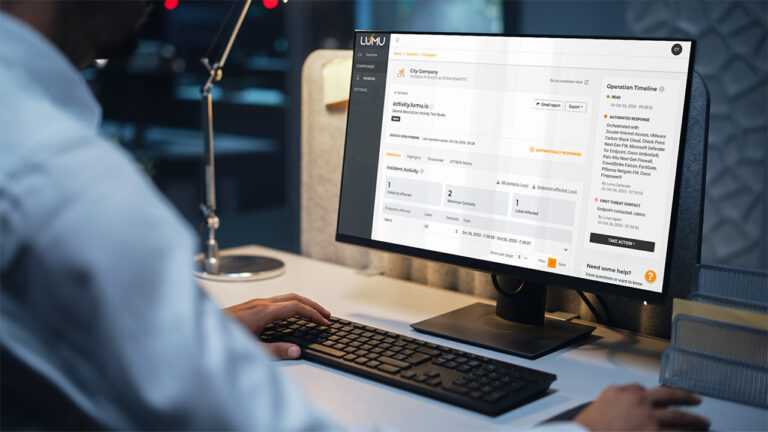
Reading Time: 4 mins2023 at Lumu: Pioneering advancements in AI-driven cybersecurity solutions and partnerships, enhancing incident management and operational efficiency.

Reading Time: 2 minsDr. Chase Cunningham discusses the critical need for state and local governments to secure against ransomware, ensuring essential services.
Reading Time: 4 minsExploring 2024 Cybersecurity Trends: How mature AI and automation are key to developing sustainable and resilient security strategies.
Reading Time: 3 minsIntroducing Lumu for MSPs Lite, a free, AI-driven cybersecurity solution for Managed Service Providers, democratizing advanced threat detection.

Reading Time: 3 minsAlert: Severe Cisco IOS XE Web UI vulnerability risks full system control. Immediate action needed for users with HTTP/HTTPS Server enabled.
Reading Time: 5 minsExplore Online vs Transfer Learning in Cybersecurity: Unpacking Lumu’s adaptive AI use for proactive threat defense and staying ahead of risks.

Reading Time: 3 minsLumu secures $30M Series B led by Forgepoint Capital, boosting cybersecurity innovation and enhancing real-time threat management.

Reading Time: 3 minsChoosing the right cybersecurity solution is pivotal in today’s threat landscape. Our buyer’s guide zeroes in on cybersecurity integrations, offering key questions to ask vendors about API availability, out-of-the-box solutions, and technical support.
Reading Time: 5 minsCollective Defense already plays a key role in shoring up the cyberdefenses of key industries. Alongside AI, it can do even more for cybersecurity practices.

Reading Time: 4 minsThe GigaOm Radar Report for Network Detection and Response (NDR) has just been released and we are pleased to announce that Lumu has been named as a Leader and an Outperformer.

Reading Time: 4 minsThreat hunting in cybersecurity can be a challenging practice. Learn how Lumu helps you build your way up the pyramid of pain and make your cybersecurity posture more difficult for threat actors to target.

Reading Time: 3 mins‘Dr. Zero Trust’ Chase Cunningham looks at Zero Trust, network visibility’s importance, and the Forrester Wave™: Network Analysis and Visibility Q2 2023

Reading Time: 5 minsLumu’s threat intelligence team has identified a new Advanced Persistent Threat (APT) actor named ‘Copode 1.0’, leveraging the LockBit Black code leaks for cyberattacks. This emerging threat underlines the need for stringent security practices and Lumu’s real-time monitoring offers an efficient response to such evolving challenges.

Reading Time: 3 minsThe recently discovered MOVEit vulnerability is an actively exploited zero-day threat, which is leading to significant breaches in large and critical enterprises. Gain insight into the nature of this vulnerability, its exploitation by the CL0P Ransomware Group, who is at risk, and the necessary remedial measures to be taken.

Reading Time: 8 minsManaged Security Service Providers (MSSPs) have become pivotal allies for businesses, providing expert services and robust technological defenses. MSSPs must understand that they are not infallible and that challenges in their growth and operational model can lead to potential gaps in security coverage.