
How to Turn MISP from a Compliance Burden into Active Defense
Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Already have an account? Sign in
Sign in

Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Reading Time: 4 minsThe Education sector is the number one global cyber target. It is clearer than ever that manual defense is failing. We look at how to automate detection and response and win the battle.
Reading Time: 5 minsContact is not compromise. True proactivity means prioritizing rapid response not blindly relying on prevention
Reading Time: 6 minsAsyncRAT is an adaptable open-source Trojan that has evolved into a global threat. We look at how it works and the best way to defend against it.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 4 minsThe State of Cybersecurity in 2021: Americas’ first federal CISO talks us in the wake of yet another FBI/CISA alert on impending cyber threats.

Reading Time: 5 minsAs Director of Engineering and Security at Upward Technologies, Elias Stucky works to solve small and medium-sized businesses’ technology problems. We spoke to him about some common SMB cybersecurity challenges.
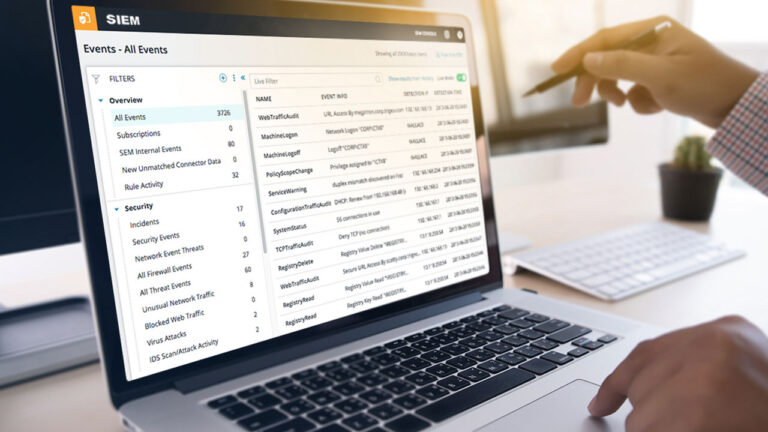
Reading Time: 4 minsVeteran Cybersecurity Operator at Lumu Andrés Argüelles looks at using Lumu with your SIEM to get the most out of both platforms.

Reading Time: 3 minsLumu Defender lets you feed Lumu’s confirmed compromise instances into your existing cybersecurity stack for an automated response to cyber threats.

Reading Time: 7 minsForrester VP & Research Director Joseph Blankenship talked to us about the state of the cybersecurity industry. Read the highlights here.

Reading Time: 4 minsXDR is the latest acronym to be buzzing around the cybersecurity industry. But does it solve the problem of ever-increasing data breaches?
Reading Time: 6 minsIn a talk presented in conjunction with the SANS Institute, cybersecurity experts Evgeniy and Jorge discuss the constructive habits that can transform professional and personal lives.

Reading Time: 3 minsA White House ransomware open letter urges business leaders to act on cybercrime. Here are some immediate action items and key takeaways.

Reading Time: 2 minsIn this Lumu Insights review, eWeek declares that Lumu makes ‘fighting cyber threats with actionable intelligence a work of IT art.’

Reading Time: 4 minsThe Colonial Pipeline cyberattack highlights the dangers of critical infrastructure ransomware attacks. Here are some takeaways for security operators at SMEs.

Reading Time: 7 minsZero Trust’s most recognizable voice speaks to us about its risks, adoption, and other ZT trends. Get more insights from “Dr. Zero Trust”.

Reading Time: 2 mins“The MITRE ATT&CK Matrix serves as the basis of a threat intelligence platform.” Get more insights from CISO Manuel Santander.

Reading Time: 4 minsThe $40 million attack on the Broward County public school district is an example of how ransomware attacks are evolving. Here’s what you can do to protect your organization.

Reading Time: 2 minsLumu Academy offers free cybersecurity courses on Lumu products. Get Lumu certification through our self-paced virtual courses.

Reading Time: 2 minsLumu’s New Experience is a game-changer. ‘Incidents’ groups related contacts and improves reporting for reduced alert fatigue and much more.