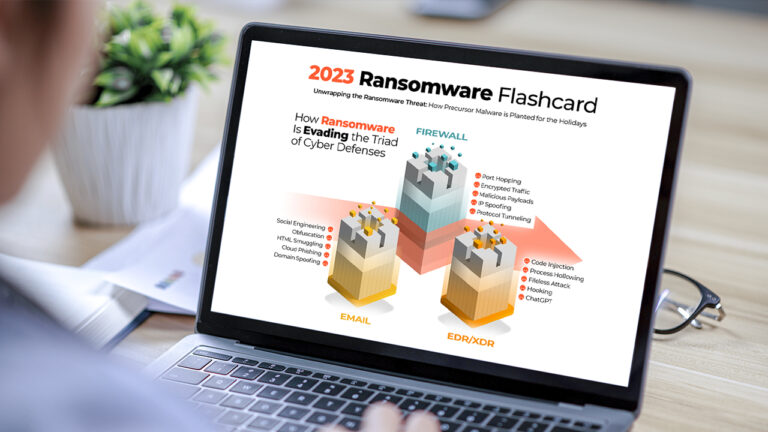
Lumu’s Ransomware Infographic: The 2023 Ransomware Flashcard
Reading Time: 3 minsExplore the key insights and trends from our 2023 Ransomware Infographic Flashcard. Learn about how hackers are evading defenses, the precursor malware they use, and ransomware’s devastating impact.