Akira Ransomware and the IoT Security Gap
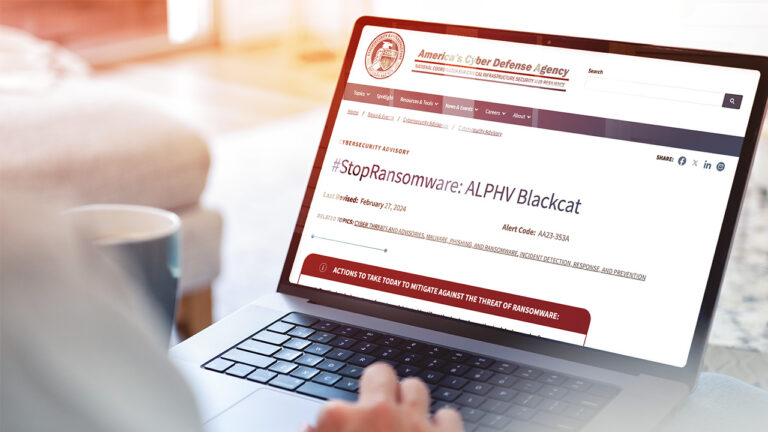
Reading Time: 3 minsThe recent Akira ransomware attack, which exploited a vulnerable webcam to bypass EDR, underscores the critical need for organizations to adopt a Zero Trust architecture and continuous network monitoring.