
How to Turn MISP from a Compliance Burden into Active Defense
Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Already have an account? Sign in
Sign in

Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Reading Time: 4 minsThe Education sector is the number one global cyber target. It is clearer than ever that manual defense is failing. We look at how to automate detection and response and win the battle.
Reading Time: 5 minsContact is not compromise. True proactivity means prioritizing rapid response not blindly relying on prevention
Reading Time: 6 minsAsyncRAT is an adaptable open-source Trojan that has evolved into a global threat. We look at how it works and the best way to defend against it.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 2 minsAs a partner in Fortinet’s Fabric-Ready Partner Program, Lumu delivers automated attack detection and response across the network. See how to integrate Lumu Defender with Fortinet’s FortiGate NGFW.
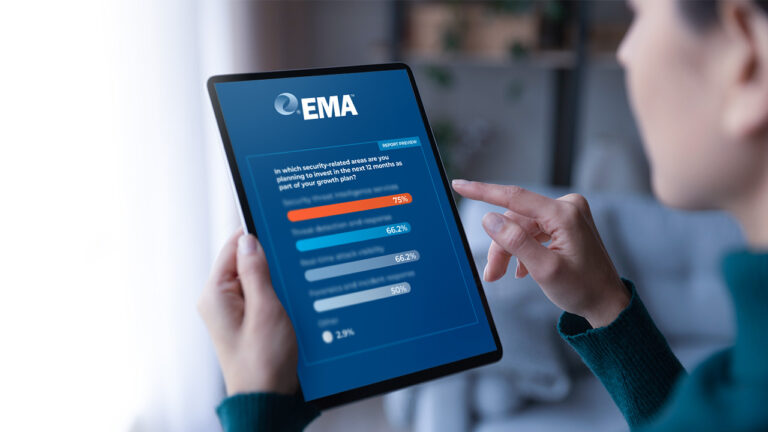
Reading Time: 2 minsThe MSP Cybersecurity Market Opportunity Blueprint shows MSPs how they can grow their business through value-added cybersecurity services. SMBs and entrepreneurs understand the need for cybersecurity.
Reading Time: 4 minsLumu Founder and CEO Ricardo Villadiego reflects on how continuous measurement in cybersecurity allows for a swift and effective response.

Reading Time: 4 minsThe recent Biden-Harris administration government represents the biggest current Zero Trust initiative. Dr. Chase Cunningham looks at how this initiative helps states, local entities, and small business entities and how you can apply.

Reading Time: 3 minsDoctor Zero Trust, Chase Cunningham looks at the guiding lights that MSPs can use to navigate the complex and at-times treacherous cybersecurity market.

Reading Time: 2 minsThe Lumu ROI Calculator is a free tool that helps organizations get an idea of the time and money they can save using Lumu. The assessment is designed to enable informed decision-making when it comes to finding the right solution.

Reading Time: 4 minsLumu’s Compromise Flashcard 2022 tells the story of compromise in 2022. Learn how threat actors are targeting companies in different ways and dig deeper into the story told by the statistics.

Reading Time: 4 minsDr. Chase Cunningham gives some insight into why he decided to head Lumu’s CISO Advisory Board.

Reading Time: 6 minsMSP Burnout is reaching critical levels. Luckily, online communities have some solid advice.

Reading Time: 4 minsManaged Service Providers are feeling the effects of MSP burnout and cybersecurity is a big culprit, but cybersecurity can also provide relief.

Reading Time: 3 minsHere are a few simple steps that startups and small businesses can take to implement a strong cybersecurity practice leveraging existing resources.

Reading Time: 5 minsLumu CTO Jeffrey Wheat takes a look at the factors placing pressure on financial sector cybersecurity teams and how automation can be the key to relieving this pressure.

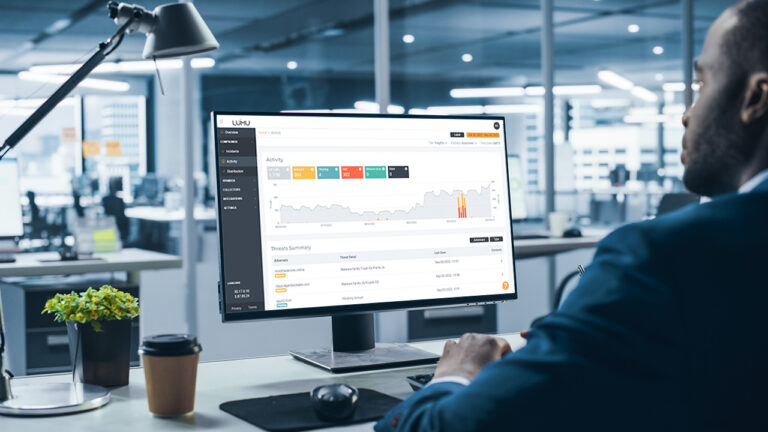
Reading Time: 4 minsThe new Lumu Incident View is a single screen that places at the cybersecurity operator’s fingertips the tools and information that they need to outwit cybercriminals at every turn.

Reading Time: 4 minsThe Conti Ransomware Group has recently unleashed a series of attacks on nations including Costa Rica, resulting in the declaration of a state of emergency. The key to their success is the network of alliances that they have built with precursor malware operators.

Reading Time: 4 minsAfter numerous conversations with customers Nicole Ibarra, Lumu’s Director of Product Marketing, reports back on her findings.