
Local Government and Education Cybersecurity Advisory
Reading Time: 6 minsLocal Government and Education Institutions are under increasing threat from cyber criminals. Explore how these critical sectors can level up their cybersecurity posture.
Already have an account? Sign in
Sign in

Reading Time: 6 minsLocal Government and Education Institutions are under increasing threat from cyber criminals. Explore how these critical sectors can level up their cybersecurity posture.

Reading Time: 4 minsThe Palo Alto Networks PAN-OS firewall vulnerability exemplifies critical flaws in traditional perimeter defenses. Understand how Lumu’s detection capabilities safeguard networks.

Reading Time: 2 minsEfficiently confirm and address ConnectWise ScreenConnect vulnerabilities with our guide and user-friendly tool.

Reading Time: 7 minsLockBit takedown news and guidance: arrests made, resilience shown, and future cybersecurity steps.
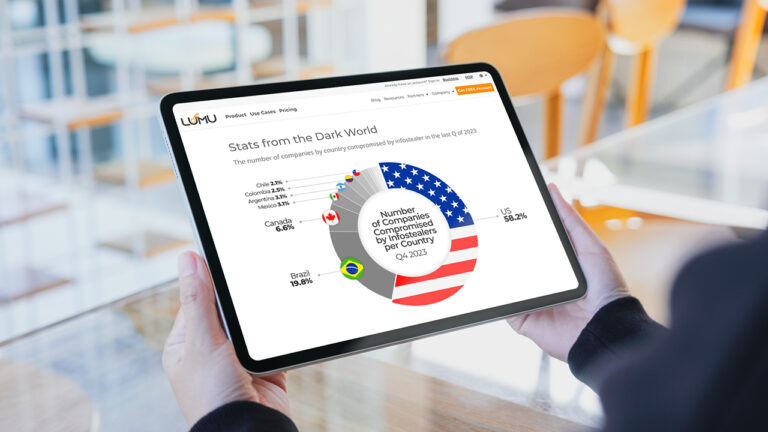
Reading Time: 7 minsExplore how infostealers compromise global security, silently stealing data and offering adversaries Initial Access to networks.
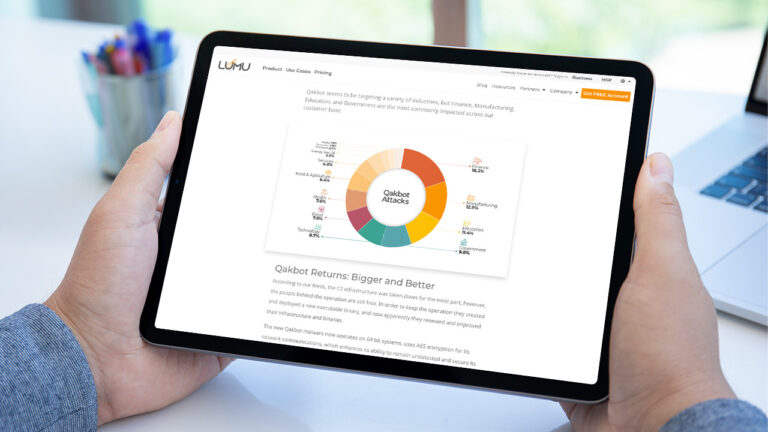
Reading Time: 3 minsQakbot resurges with new updates, posing a greater cyber threat. Discover how it’s evading defenses in our latest advisory

Reading Time: 3 minsAlert: Severe Cisco IOS XE Web UI vulnerability risks full system control. Immediate action needed for users with HTTP/HTTPS Server enabled.

Reading Time: 5 minsLumu’s threat intelligence team has identified a new Advanced Persistent Threat (APT) actor named ‘Copode 1.0’, leveraging the LockBit Black code leaks for cyberattacks. This emerging threat underlines the need for stringent security practices and Lumu’s real-time monitoring offers an efficient response to such evolving challenges.

Reading Time: 3 minsThe recently discovered MOVEit vulnerability is an actively exploited zero-day threat, which is leading to significant breaches in large and critical enterprises. Gain insight into the nature of this vulnerability, its exploitation by the CL0P Ransomware Group, who is at risk, and the necessary remedial measures to be taken.

Reading Time: 11 minsEDR Evasion includes a suite of techniques that hackers use to elude endpoint defenses. Discover how hackers evade Endpoint Detection and Response (EDR) systems using various techniques. Learn about the common tactics used by cyber attackers to bypass endpoint defenses and how to better protect against these stealthy attacks.