
Redefining Proactive Security: Why Contact Is Not a Compromise
Reading Time: 5 minsContact is not compromise. True proactivity means prioritizing rapid response not blindly relying on prevention
Already have an account? Sign in
Sign in
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 5 minsContact is not compromise. True proactivity means prioritizing rapid response not blindly relying on prevention

Reading Time: 5 minsYour security stack is built on trusting domain reputation scores. But attackers now weaponize malicious domain detection methods against you.

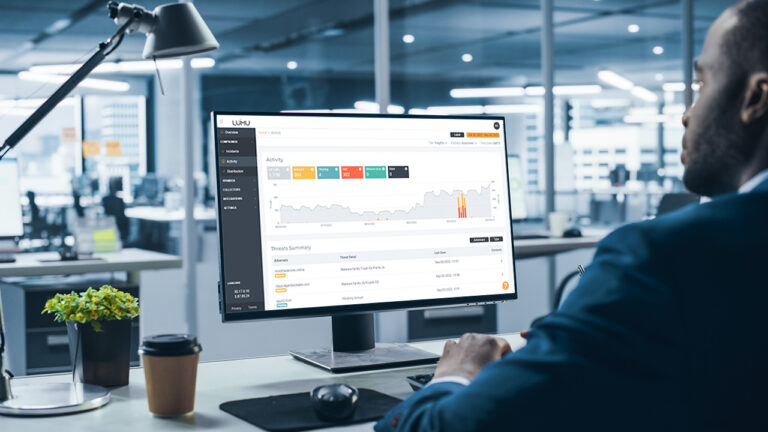
Reading Time: 5 minsIntroducing Lumu Autopilot, the latest innovation that delivers on our promise to help the world operate cybersecurity proficiently.

Reading Time: 5 minsCybersecurity Analysts can turn to these 7 habits to complement their cybersecurity strategy and be more efficient.

Reading Time: 3 minsThe 2022 Lumu Product Recap brings together all the Continuous Compromise Assessment Improvements we delivered over the last year.
Reading Time: 4 minsLumu Founder and CEO Ricardo Villadiego reflects on how continuous measurement in cybersecurity allows for a swift and effective response.

Reading Time: 3 minsDoctor Zero Trust, Chase Cunningham looks at the guiding lights that MSPs can use to navigate the complex and at-times treacherous cybersecurity market.

Reading Time: 2 minsThe Lumu ROI Calculator is a free tool that helps organizations get an idea of the time and money they can save using Lumu. The assessment is designed to enable informed decision-making when it comes to finding the right solution.

Reading Time: 4 minsThe new Lumu Incident View is a single screen that places at the cybersecurity operator’s fingertips the tools and information that they need to outwit cybercriminals at every turn.

Reading Time: 2 minsAnalyst firm Frost & Sullivan assesses how major players in the NAV market are addressing organizations’ biggest pain points.

Reading Time: 2 minsGerman Patiño has spent over a decade helping companies implement cutting-edge cybersecurity, including ZT. Here’s why Lumu is the next step.

Reading Time: 5 minsRansomware is always preceded by signs that can be identified and stopped. Learn about ransomware chains and their weakest links.

Reading Time: 3 minsMSPs’ skills and resources make them perfectly positioned to fulfill SMBs’ need for increased cybersecurity resilience.

Reading Time: 2 minsThe monetization of cybercrime has diversified while deep web credential market activity has been accelerating. Here’s why that’s serious.

Reading Time: 3 minsLumu Defender lets you feed Lumu’s confirmed compromise instances into your existing cybersecurity stack for an automated response to cyber threats.