
How to Turn MISP from a Compliance Burden into Active Defense
Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Already have an account? Sign in
Sign in

Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Reading Time: 4 minsThe Education sector is the number one global cyber target. It is clearer than ever that manual defense is failing. We look at how to automate detection and response and win the battle.
Reading Time: 5 minsContact is not compromise. True proactivity means prioritizing rapid response not blindly relying on prevention
Reading Time: 6 minsAsyncRAT is an adaptable open-source Trojan that has evolved into a global threat. We look at how it works and the best way to defend against it.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 3 minsCybersecurity operations can be hard but are needed in all businesses. EMA Research Director Chris Steffen shares how MSPs and MSSPs can help small and medium-sized businesses operate cybersecurity proficiently.
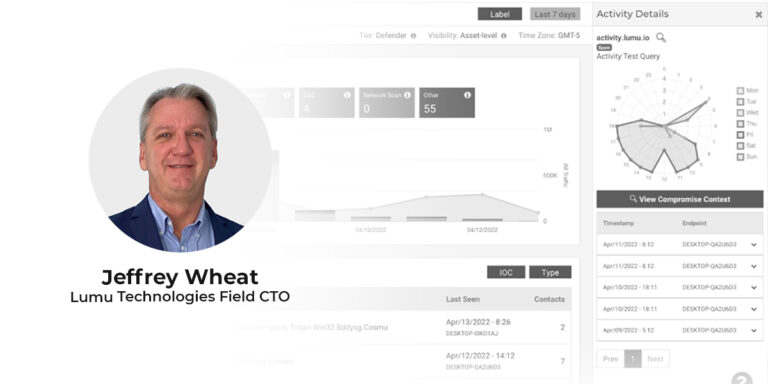
Reading Time: 4 minsLumu’s recently appointed Field CTO Jeffrey Wheat looks at the future of the SOC and how incremental improvement leads to proficient operations. Beginning his cybersecurity career at the department of defense, Jeffrey Wheat is a proven leader and CISSP with 30 years of experience spanning SOC management at international firms as well as cybersecurity architecture design and implementation.
Reading Time: 4 minsIn April of 2022, it seems that cybersecurity is more unsettled than ever. Here are the top questions we’ve been receiving about cybersecurity and emerging cyber threats

Reading Time: 3 minsTrends from 2021 indicate that 2022 will see an increased threat of ransomware on a global level. Here are some insights and background information to accompany the facts and figures provided by our Ransomware Flashcard 2022.

Reading Time: 3 minsLumu Free just got a major upgrade. We’ve included more metadata collectors, giving you greater network visibility and more closely reflecting our vision of how cybersecurity needs to be operated.
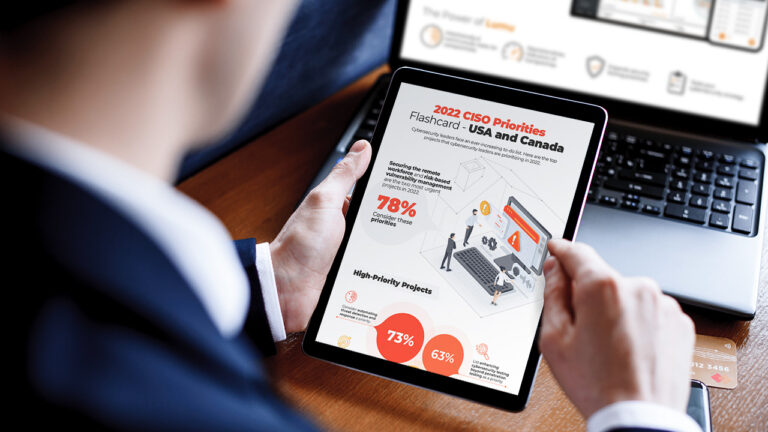
Reading Time: 2 minsWe polled over 300 CISOs from across the Americas on the cybersecurity challenges they’re prioritizing in 2022. Gain insight into the key projects, emerging priorities, and deprioritized secondary initiatives—despite high risks.
Reading Time: 2 minsIn 2021 Lumu grew from strength to strength—in every metric. Here’s our Year in Review with all the unmissable highlights from the year of experience-based growth.
Reading Time: 2 minsThe Log4j vulnerability (designated as CVE-2021-44228 by MITRE) affects 1000’s of software applications. Here are some quick facts and how Lumu helps.

Reading Time: 2 minsWith cybersecurity evolving at a faster pace than ever, here are some predictions for what to look out for in cybersecurity in 2022.

Reading Time: 2 minsAnalyst firm Frost & Sullivan assesses how major players in the NAV market are addressing organizations’ biggest pain points.

Reading Time: 2 minsGerman Patiño has spent over a decade helping companies implement cutting-edge cybersecurity, including ZT. Here’s why Lumu is the next step.

Reading Time: 2 minsSmall businesses are realizing that cybersecurity is an increasingly important business risk. Here are a few commonly believed cybersecurity myths that need to be cleared up.

Reading Time: 5 minsRansomware is always preceded by signs that can be identified and stopped. Learn about ransomware chains and their weakest links.

Reading Time: 3 minsMSPs’ skills and resources make them perfectly positioned to fulfill SMBs’ need for increased cybersecurity resilience.

Reading Time: 2 minsThe monetization of cybercrime has diversified while deep web credential market activity has been accelerating. Here’s why that’s serious.