Mario Lobo
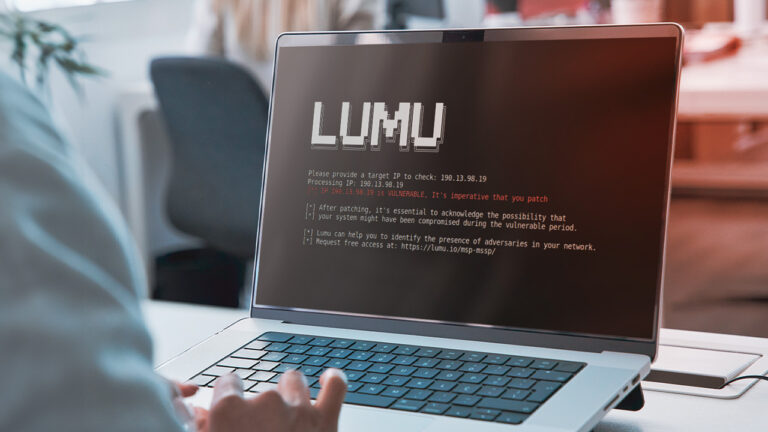
Mario Lobo Romero is a Cybersecurity Specialist and Threat Analyst with over 18 years in InfoSec and Cyber Intelligence. As a Cyber Threat Intelligence Researcher at Lumu Technologies, his focus is on the independent collection, analysis, and curation of threat intelligence. His experience includes senior intelligence roles at critical sectors like National Defense and Finance. He is highly skilled in Penetration Tests, Malware Analysis, and implementing cybersecurity frameworks. Mario holds an Msc. in Cybersecurity and certifications including GIAC-GSEC and ISO 27000.