
Why I Joined Lumu’s CISO Advisory Board
Reading Time: 4 minsDr. Chase Cunningham gives some insight into why he decided to head Lumu’s CISO Advisory Board.
Already have an account? Sign in
Sign in
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 4 minsDr. Chase Cunningham gives some insight into why he decided to head Lumu’s CISO Advisory Board.

Reading Time: 6 minsMSP Burnout is reaching critical levels. Luckily, online communities have some solid advice.

Reading Time: 4 minsManaged Service Providers are feeling the effects of MSP burnout and cybersecurity is a big culprit, but cybersecurity can also provide relief.
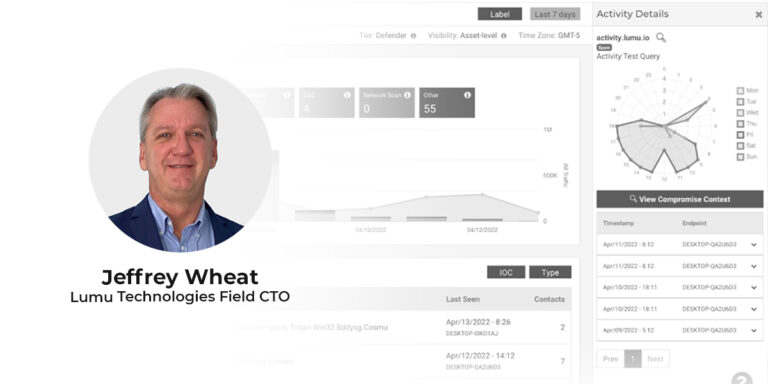
Reading Time: 4 minsLumu’s recently appointed Field CTO Jeffrey Wheat looks at the future of the SOC and how incremental improvement leads to proficient operations. Beginning his cybersecurity career at the department of defense, Jeffrey Wheat is a proven leader and CISSP with 30 years of experience spanning SOC management at international firms as well as cybersecurity architecture design and implementation.
Reading Time: 4 minsIn April of 2022, it seems that cybersecurity is more unsettled than ever. Here are the top questions we’ve been receiving about cybersecurity and emerging cyber threats

Reading Time: 3 minsThese holiday cybersecurity reads are sure to captivate and educate as we head into another eventful year for cybersecurity.

Reading Time: 4 minsOn average, a CISO’s tenure is only 26 months. Fabian Zambrano, Director of Cybersecurity at Davivienda, lays out any new CISO’s priorities.

Reading Time: 4 minsSecurity operations teams are increasingly inundated with alerts. Take a look at how Lumu can make your SOC more efficient in 3 easy steps.

Reading Time: 4 minsOver 90% of ransomware attacks are preventable. We have compiled a list of the most common mistakes leading to ransomware regret. Do you recognize any?

Reading Time: 4 minsArtificial intelligence and Machine Learning are increasingly popular in cybersecurity, but like all tools, the key is how you use them.

Reading Time: 2 minsCybersecurity Strategy needs to be more adaptable and resilient following the revelations brought about by the Covid-19 pandemic

Reading Time: 3 minsLumu now provides compromise context in one place, providing more insight into the nature of attacks and improving incident response

Reading Time: 2 minsNetwork metadata has the power to efficiently answer the most important question in cybersecurity: Is my network compromised?

Reading Time: 2 minsThe economic downturn caused by the coronavirus will place financial pressure on cybersecurity budgets, forcing more intelligent spending.

Reading Time: 2 minsThe coronavirus pandemic has forced enterprises into a rushed transition to working remotely that exposes them to security breaches.