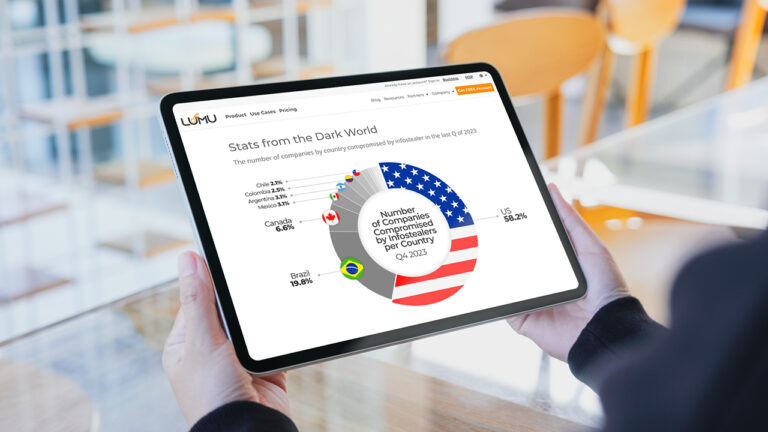
Infostealers: The Silent Threat Compromising the World One Password at a Time
Reading Time: 7 minsExplore how infostealers compromise global security, silently stealing data and offering adversaries Initial Access to networks.
Already have an account? Sign in
Sign in
Get the latest cybersecurity articles and insights straight from the experts.
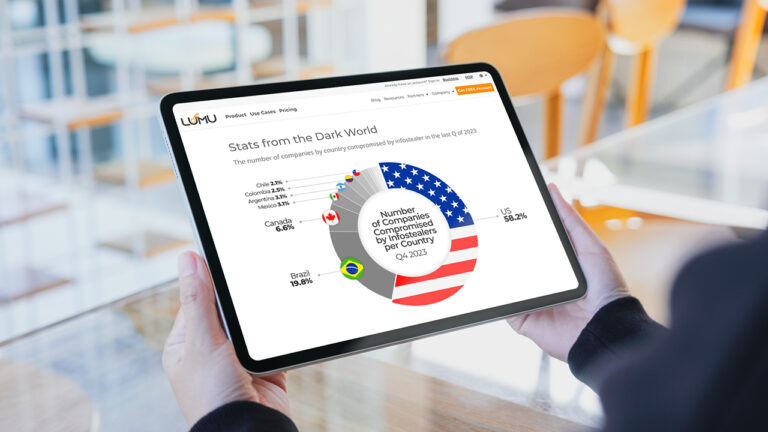
Reading Time: 7 minsExplore how infostealers compromise global security, silently stealing data and offering adversaries Initial Access to networks.
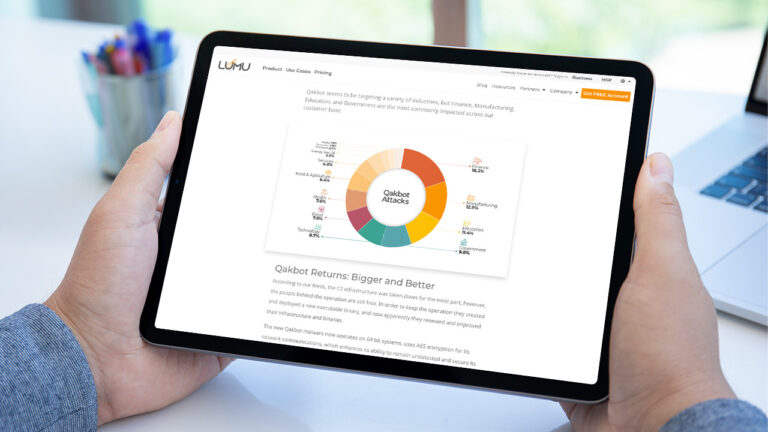
Reading Time: 3 minsQakbot resurges with new updates, posing a greater cyber threat. Discover how it’s evading defenses in our latest advisory

Reading Time: 11 minsEDR Evasion includes a suite of techniques that hackers use to elude endpoint defenses. Discover how hackers evade Endpoint Detection and Response (EDR) systems using various techniques. Learn about the common tactics used by cyber attackers to bypass endpoint defenses and how to better protect against these stealthy attacks.

Reading Time: 2 minsOur Threat Intelligence Team has discovered approximately 70,000 instances potentially exposed to a dangerous vulnerability in the 3CX Desktop App currently being exploited by threat actors. Learn how it could impact your company and how to respond in case adversaries leveraged this vulnerability to enter your organization.