
How to Turn MISP from a Compliance Burden into Active Defense
Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Already have an account? Sign in
Sign in

Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.
Reading Time: 4 minsThe Education sector is the number one global cyber target. It is clearer than ever that manual defense is failing. We look at how to automate detection and response and win the battle.
Reading Time: 5 minsContact is not compromise. True proactivity means prioritizing rapid response not blindly relying on prevention
Reading Time: 6 minsAsyncRAT is an adaptable open-source Trojan that has evolved into a global threat. We look at how it works and the best way to defend against it.
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 4 minsPlatformization can limit flexibility and innovation. Discover why an open SecOps Platform is essential for cybersecurity
Reading Time: 2 minsThis VPN vulnerability highlights a typical risks associated with perimeter defenses, which can allow attackers to access networks. Stay informed and secure your network promptly.

Reading Time: 6 minsLocal Government and Education Institutions are under increasing threat from cyber criminals. Explore how these critical sectors can level up their cybersecurity posture.

Reading Time: 4 minsMissed RSA Conference 2024? Explore Lumu CEO and RSAC veteran Ricardo Villadiego’s perspective on the key takeaways from RSAC 2024

Reading Time: 5 minsIntroducing Lumu Autopilot, the latest innovation that delivers on our promise to help the world operate cybersecurity proficiently.

Reading Time: 4 minsThe Palo Alto Networks PAN-OS firewall vulnerability exemplifies critical flaws in traditional perimeter defenses. Understand how Lumu’s detection capabilities safeguard networks.

Reading Time: 2 minsEfficiently confirm and address ConnectWise ScreenConnect vulnerabilities with our guide and user-friendly tool.

Reading Time: 7 minsLockBit takedown news and guidance: arrests made, resilience shown, and future cybersecurity steps.

Reading Time: 3 minsExplore the challenges faced by a wide range of organizations in affording SOC analyst salaries amidst rising cybersecurity demands and limited budgets
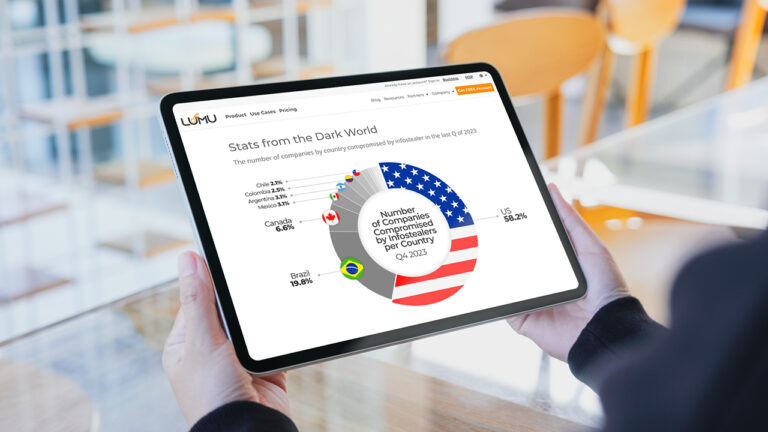
Reading Time: 7 minsExplore how infostealers compromise global security, silently stealing data and offering adversaries Initial Access to networks.
Reading Time: 5 minsDive into the impact and future of MSP Cybersecurity Disruption. Is it a looming threat or a hidden opportunity?

Reading Time: 5 minsUncover key tactics for navigating SLED cybersecurity challenges, focusing on budget-friendly solutions, advanced threat detection, and automated response.

Reading Time: 8 minsProtect your business from digital risks with cyber insurance, covering data breaches, cyberattacks, and recovery costs.
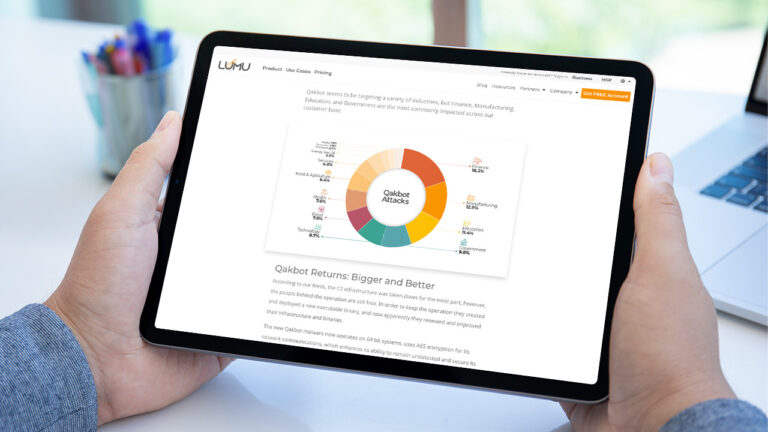
Reading Time: 3 minsQakbot resurges with new updates, posing a greater cyber threat. Discover how it’s evading defenses in our latest advisory

Reading Time: 4 minsDiscover Lumu’s 2023 MSP breakthroughs: Improved threat detection, incident management, and more.