
Advisory Alert: Remcos RAT Real-Time Surveillance Platform
Reading Time: 7 minsHow does the 2026 Remcos RAT bypass your security to stream live surveillance? Understand the latest campaign and how to protect your enterprise.
Already have an account? Sign in
Sign in
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 7 minsHow does the 2026 Remcos RAT bypass your security to stream live surveillance? Understand the latest campaign and how to protect your enterprise.

Reading Time: 4 minsManual MISP management creates a resource drain that risks business outages. It is essential to automate this intelligence to secure your financial organization.

Reading Time: 6 minsAI-powered autonomous malware now generates unique threats at machine speed. This makes the transition from human-led to automated defense urgent.

Reading Time: 6 minsAsyncRAT is an adaptable open-source Trojan that has evolved into a global threat. We look at how it works and the best way to defend against it.

Reading Time: 10 minsThis technical deep-dive analyzes a sophisticated Amadey Stealer campaign leveraging Living-off-the-Land tactics and defense evasion, identified through Lumu’s network behavior analysis.

Reading Time: 5 minsDeathRansom ransomware has evolved, hiding in malicious PDFs to bypass defenses. It does not break down the door. It is invited in.

Reading Time: 5 minsYour security stack is built on trusting domain reputation scores. But attackers now weaponize malicious domain detection methods against you.

Reading Time: 6 minsOur analysis of APT-C-36, Blind Eagle, breaks down how a regional phishing attack becomes a global supply chain threat, providing insights for your proactive defense.

Reading Time: 6 minsFresh from DEFCON 33, Lumu’s Mario Lobo identifies a revolutionary shift in AI-driven attacks that is changing the rules for cyber defenders and their tools.
Reading Time: 6 minsBumbleBee malware facilitates severe attacks like ransomware or data theft. Threat intelligence shows increasing deployment across key industries and locations.
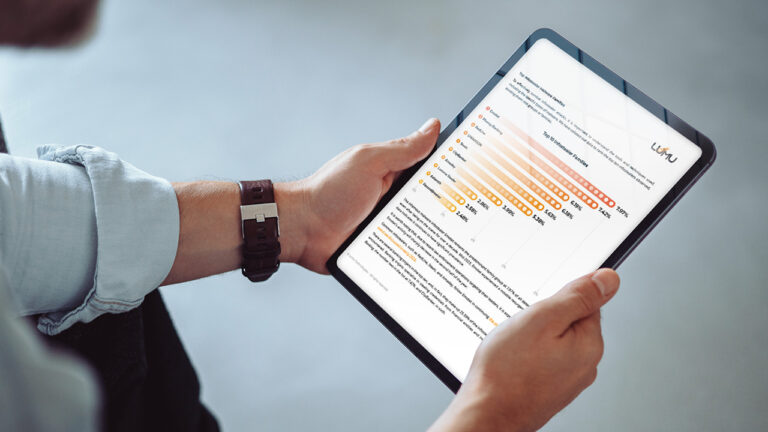
Reading Time: 5 minsLumu’s Compromise Report for 2024 uncovers surprising information about how infostealer malware has increasingly targeted US organizations, local government, and education establishments.

Reading Time: 4 minsEssential cybersecurity tips to safeguard K-12 schools during the back-to-school season.

Reading Time: 4 minsThe Palo Alto Networks PAN-OS firewall vulnerability exemplifies critical flaws in traditional perimeter defenses. Understand how Lumu’s detection capabilities safeguard networks.

Reading Time: 2 minsEfficiently confirm and address ConnectWise ScreenConnect vulnerabilities with our guide and user-friendly tool.

Reading Time: 7 minsLockBit takedown news and guidance: arrests made, resilience shown, and future cybersecurity steps.