Advisory Alert: Sarcoma Ransomware Double Extortion Threat
Reading Time: 6 minsWhat is Sarcoma ransomware? This new double extortion threat both steals sensitive data and encrypting systems. You need to ensure your organization is prepared.
Already have an account? Sign in
Sign in
Get the latest cybersecurity articles and insights straight from the experts.
Reading Time: 6 minsWhat is Sarcoma ransomware? This new double extortion threat both steals sensitive data and encrypting systems. You need to ensure your organization is prepared.

Reading Time: 4 minsA supply chain cyberattack on C&M Software has impacted Brazilian financial institutions. Learn about the incident, its implications, and how to protect your organization from similar third-party risks.

Reading Time: 5 minsFollowing the release of data from over 15,000 Fortinet devices, what can we do to protect against further compromise?

Reading Time: 4 minsAnonymization, though designed to protect privacy, is increasingly exploited by cybercriminals to mask their origins and identities, complicating the detection and mitigation of attacks.

Reading Time: 4 minsThe December 2024 breach of a student information software solution for K-12 educational institutions, PowerSchool, leaves us asking: what can we learn from it?

Reading Time: 7 minsThis is the story of a serious DNS tunneling attack on a multinational insurance provider — discover the importance of DNS tunneling detection, what we found when we investigated the attack, and how we contained it.
Reading Time: 7 minsMario Lobo, Cybersecurity Specialist at Lumu Technologies, recently attended DEFCON – a hacker convention held annually in Las Vegas, Nevada – and he highlights his big takeaways.

Reading Time: 3 minsExplore the Snowflake supply chain attack, how infostealer malware impacted hundreds of major companies, and essential measures to protect your organization from similar threats
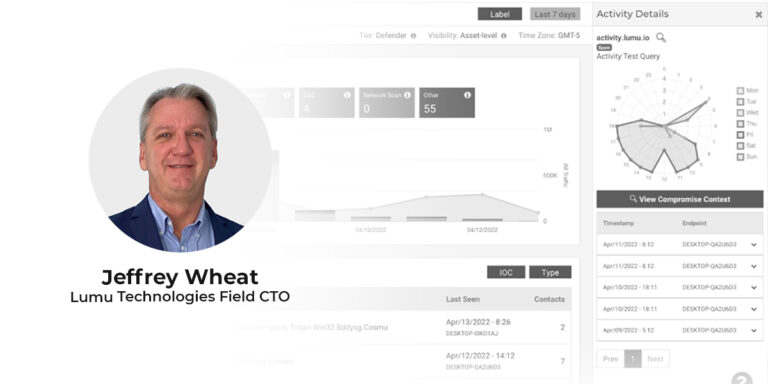
Reading Time: 4 minsLumu’s recently appointed Field CTO Jeffrey Wheat looks at the future of the SOC and how incremental improvement leads to proficient operations. Beginning his cybersecurity career at the department of defense, Jeffrey Wheat is a proven leader and CISSP with 30 years of experience spanning SOC management at international firms as well as cybersecurity architecture design and implementation.
Reading Time: 4 minsIn April of 2022, it seems that cybersecurity is more unsettled than ever. Here are the top questions we’ve been receiving about cybersecurity and emerging cyber threats

Reading Time: 3 minsA White House ransomware open letter urges business leaders to act on cybercrime. Here are some immediate action items and key takeaways.

Reading Time: 4 minsThe Colonial Pipeline cyberattack highlights the dangers of critical infrastructure ransomware attacks. Here are some takeaways for security operators at SMEs.

Reading Time: 3 mins2019 showed that no business is immune to security breaches. Turn your attention to these 8 key areas in 2020.

Reading Time: 5 minsFinancial institutions, retailers, school districts, hospitals, airlines, public offices will all be future targets of cyberattacks.

Reading Time: 3 minsIn one of the largest data breaches ever, Capital One admitted recently that more than 100 million customer records were compromised.