Table of Contents
Modern cybercriminals don’t need to hack their way through your firewalls if they already possess what they need to stroll right in. Stolen credentials, leaked sensitive data on the dark web, and compromised third-party networks are all potential entry points that can render your firewalls and endpoint protection moot.
Napoleon Bonaparte is quoted as saying, “War is ninety percent information,” and that is never more true than in cyberdefense. By learning what adversaries know about your organization and where they may find weak spots in your defenses, you can proactively strengthen where it is needed most.
Motivated by this, Lumu is proud to announce a new offering that will give our customers an extra dimension to their security operations — Lumu Discover. Lumu Discover continuously assesses your external attack surface, to ensure the best proactive cybersecurity, based on real-time actionable intelligence.
Before looking in more depth at Lumu Discover, first let’s discuss what is meant by external attack surface and why assessing this attack surface in real-time is so important.
What Is an External Attack Surface?
The external attack surface is everything that can be seen and potentially accessed from outside your network, including exposed sensitive information that can aid the breaching of defenses. This includes vulnerable websites, apps, email servers, and any other online systems. It also includes credentials and leaked data pertaining to your employees and system configurations that may allow threat actors to breach your systems.
The external attack surface represents the sum of all digital assets an organization exposes to the public internet or any network outside of its direct control. Think of it as the digital storefront of your organization, visible and potentially accessible to anyone, anywhere in the world (including malicious parties like threat actors).
This surface includes all internet-facing systems like websites, web applications, cloud services, email servers, and publicly accessible APIs. It also encompasses the network infrastructure that supports these services, such as public IP addresses and domain names. Effectively, anything that can be discovered and interacted with from outside your private network perimeter constitutes the external attack surface, making it the initial point of contact for external threat actors seeking to penetrate your defenses.
Beyond systems and applications, the external attack surface also includes exposed sensitive information that can significantly aid attackers. This encompasses leaked credentials belonging to employees or services, misconfigurations in publicly facing systems, and any data inadvertently made accessible online. For example, exposed API keys, cloud storage buckets left open, or even publicly indexed configuration files can provide threat actors with shortcuts to bypass security measures.
This sensitive information is often harvested through automated tools like web scrapers and infostealers. Threat actors frequently aggregate and expose this harvested data on the dark web, seeking to monetize their illicit findings by selling it to other malicious parties, including ransomware operators.
Crucially, it’s important to recognize that this compromising information isn’t always directly sourced from your own organization. Vulnerabilities or data leaks originating from third-party vendors, technology partners, or any entity with access to your data can also inadvertently weaken your external attack surface.
The Importance of Real-Time External Attack Surface Assessment
To paraphrase a well-known cybersecurity mantra, there are two types of companies in the world: those that have their credentials exposed and those that have their credentials exposed and don’t know it.
Today’s threat actors don’t need weeks or months to execute their attacks. A simple ransomware attack that leverages privileged access or a vulnerability can be executed in a matter of minutes or hours. In many cases, the credentials and information that is already available online is enough to achieve privileged access as easily as logging in to a terminal.
Organizations need to know immediately when sensitive information becomes available. Every minute or day that they wait gives threat actors a window of opportunity to carry out their malicious aims. In this context, periodic assessments are simply not enough.
Continuously assessing your internet-facing assets allows you to identify and address vulnerabilities as they appear, before attackers can exploit them. Gaining this visibility enables organizations to act rapidly and go straight to where the issue lies, minimizing the window of opportunity for malicious actors.
Lumu Discover
Lumu has been working hard to create a new and effective real-time external attack surface assessment solution. We can now announce a new offering: Lumu Discover.
Lumu Discover includes a comprehensive range of features and is easily viewed and controlled from the Lumu portal. What are some examples of actionable intelligence from Lumu Discover?
- Discover unknown internet-facing assets
- Reveal exposed assets
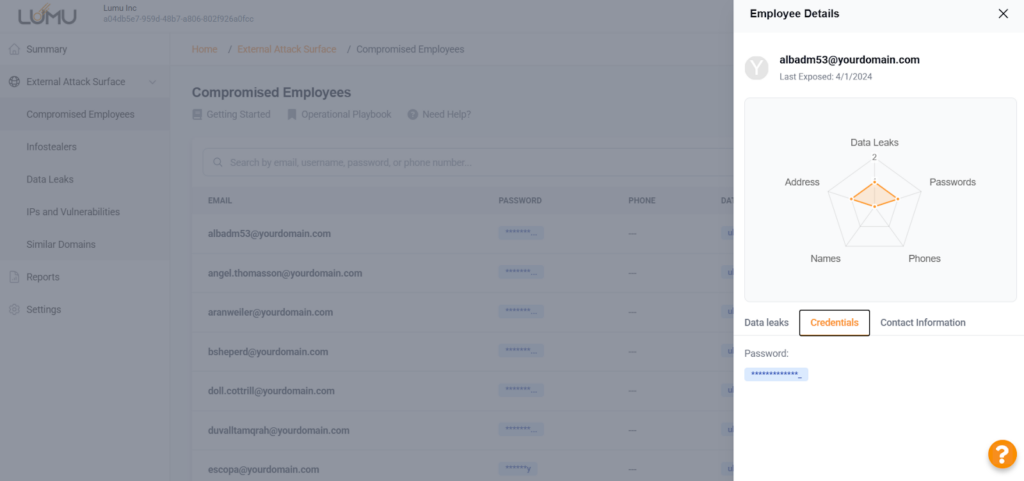
- Discover compromised credentials
- Pinpoint security gaps and vulnerabilities
- Identify misconfigurations and unpatched systems
- Identify users at high risk of phishing attacks
- Uncover cyber-risk from third-party vendors
Lumu Discover provides continuous external attack surface assessment. It relentlessly analyzes vast amounts of data, including information from the dark web, to identify any mentions or leaks related to your organization. This ongoing monitoring ensures you have the most up-to-date view of your external exposure.
The Lumu Discover Portal
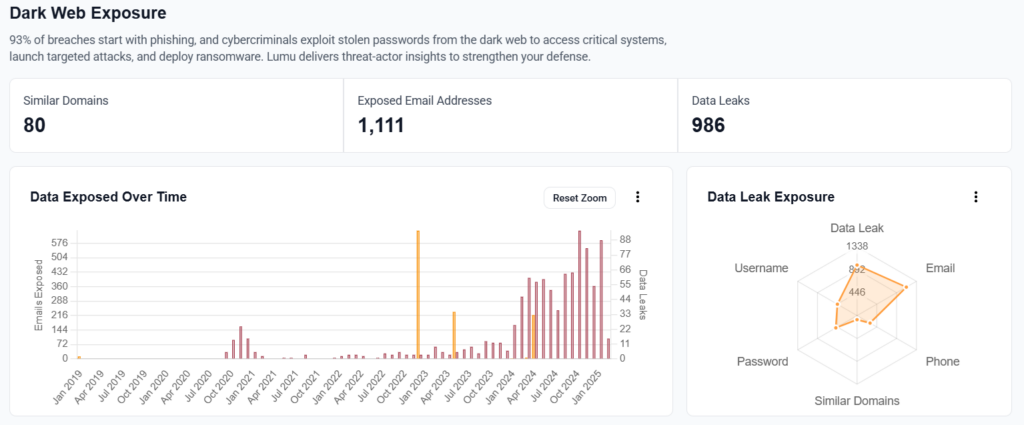
The Lumu Discover portal front page gives a quick overview of all your sensitive data that has been exposed online, showing how this exposure has developed over time, as well as what type of data is exposed. To start with, the Dark Web Exposure section includes all exposed email addresses, data leaks and similar domains found.
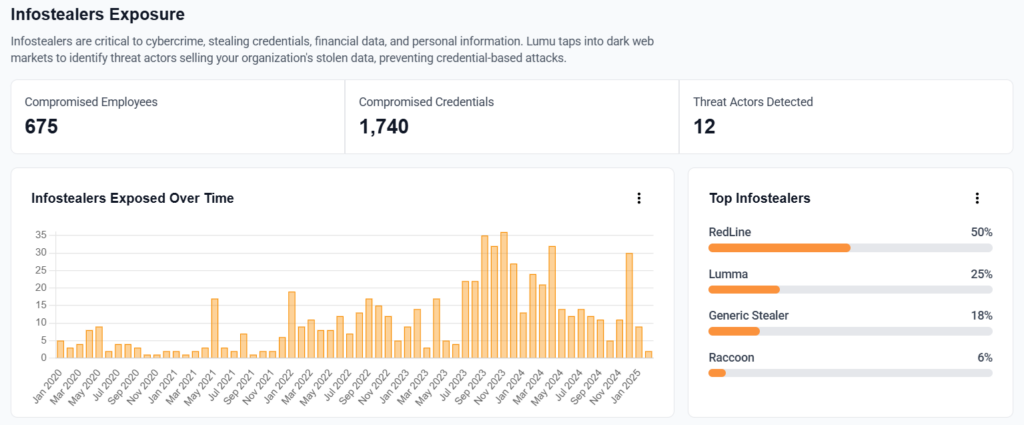
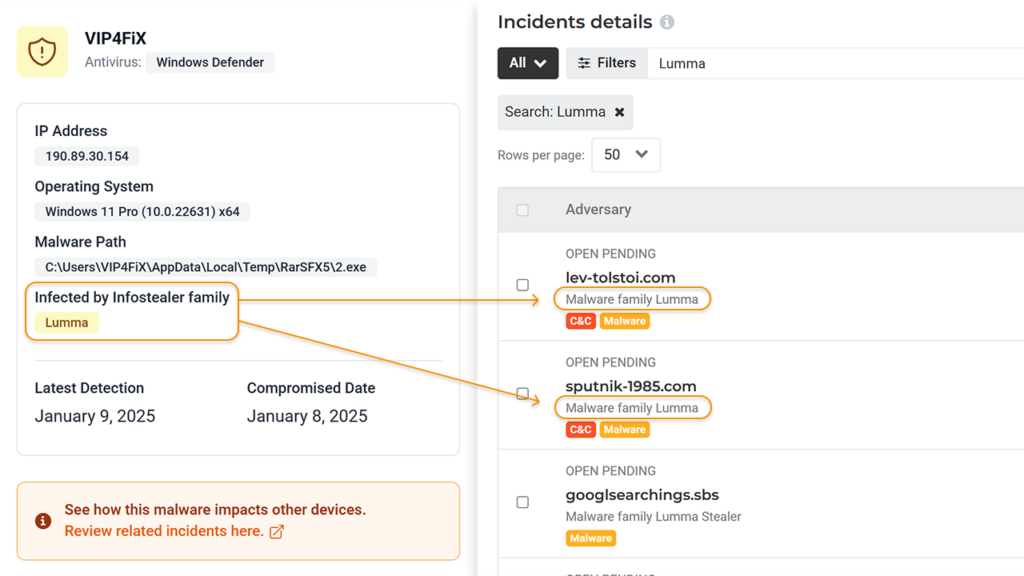
Infostealer exposure is also visually represented along with which infostealer malware family was responsible for the exposure, and key figures around the number of employees and credentials compromised.
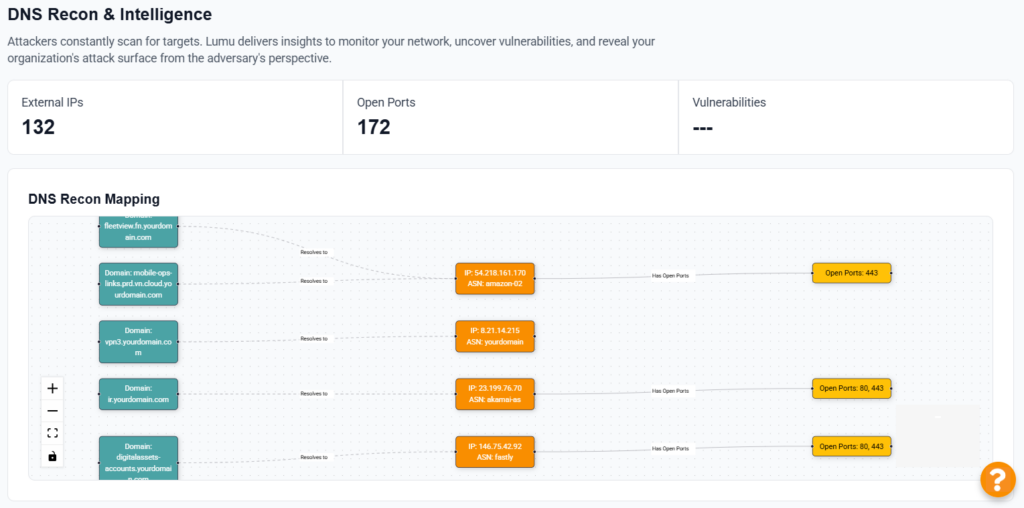
The DNS Recon and Intelligence section shows the open ports, vulnerabilities , and external IPs found by Lumu Discover’s reconnaissance, along with interactive mapping of risky domains, IPs, and ports.
But the Lumu Discover portal doesn’t stop there. For each exposed record, the portal will show the details of the finding, giving you the particulars you need to take action.
When Lumu Discover is paired with Lumu Defender, the portal maps external exposure to confirmed compromise incidents. This feature will allow you to see if your external threat surface correlates with internal malicious traffic or active compromises — with the ability to pinpoint to the threat actor and the involved devices. Keep in mind that this correlation feature applies specifically to devices within Lumu Defender’s deployment and monitoring scope.
For a detailed overview of all the features included with Lumu Defender, feel free to visit our technical documentation page.
With Lumu Discover, gain the advantage by proactively identifying leaked data and understanding your exposed attack surface. Visualize potential attack pathways and take decisive action. Get started with Lumu Discover here.




