Table of Contents
Disparate Realities
Looking back on compromise over the last year tells the story of how different attacks are impacting organizations globally. One particularly interesting fact is that compromise seems to impact organizations differently depending on their size and industry.
It appears that attackers are becoming more intentional in the way that they target organizations, taking different approaches and carrying out attacks more thoughtfully.
As is shown by our Compromise Flashcard 2022 infographic, the story of compromise is very different for small businesses than for medium-sized and large organizations.
Let’s first take a look at the most prevalent attack types and industries being targeted.
How Are Attackers Getting in?
Malware continues to be the primary cause of compromise and one of the most prevalent threats with nearly 60% of respondents indicating that they have detected malware on their corporate devices.
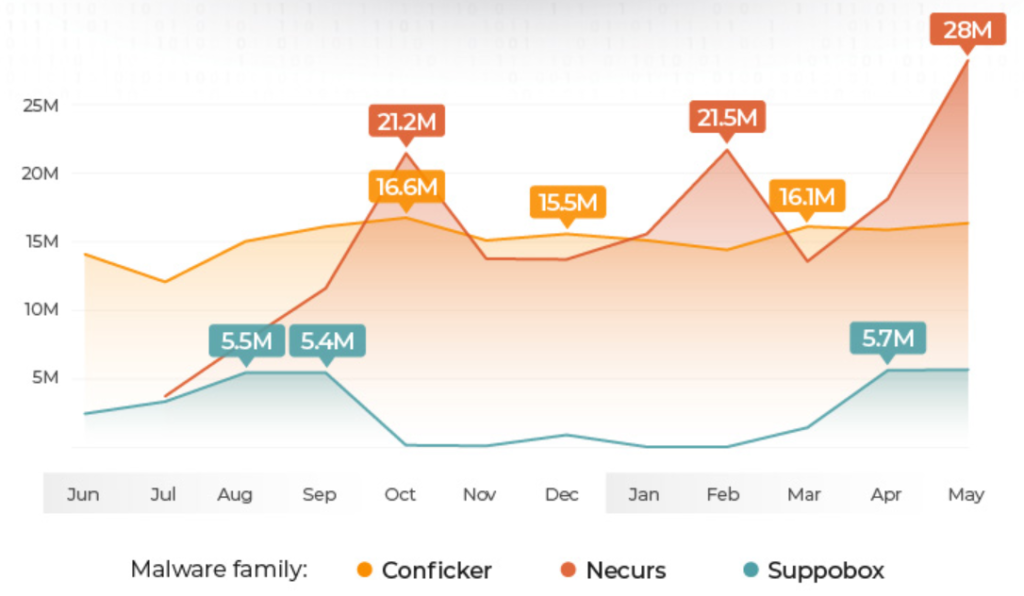
Most active Malware families impacting organizations globally include:
- Conficker, a highly prevalent botnet
- Necurs, a botnet capable of distributing ransomware
- Suppobox, a banking trojan
Who Are They Targeting?
The top four most targeted industries, according to Verizon, include:
- Professional, scientific, and technical services organizations at 19.3%
- Public Administration and government at 15.1%
- Information, broadcasting, and telecommunications at 13.9%
- Finance and insurance at 13.7%
Healthcare saw a 45% increase in incidents (2022: 849, 2021: 655) along with a 21% increase in data breaches (2022: 571, 2021: 472), according to the Verizon Data Breach Investigations Reports of 2022 and 2021.
This trend shows that threat actors are increasingly ruthless when it comes to targeting the most vulnerable industries. The sensitive information held by these organizations only serves to make them more tempting targets. Additionally, it’s worth noting that the additional regulatory burden under HIPAA has not served to lower the frequency of breaches.
Phishing Affects Verticals Differently
When it comes to phishing, the risk varies depending on the size and vertical. Data from KnowBe4 indicates that small and medium-sized Healthcare organizations are most at risk. For large and medium-sized businesses Energy & Utilities are the most at-risk verticals.
Overall, small, medium, and large businesses have different levels of exposure to phishing based on their industry which indicates that threat actors are attempting to compromise companies differently, according to their size and industry. Companies should take note of how threat actors are targeting their networks and adapt their cybersecurity posture accordingly. Unfortunately, many companies do not have visibility into their networks or the facts needed to make such decisions.
Why Is Detection Taking So Long?
Attacker dwell time is 201 days on average with compromise detection and containment taking approximately 271 days on average. Compromise continues to stay undetected for long periods of time, which is a trend that we continue to see year over year.
Results from the Lumu Ransomware Assessment, show a few reasons why attacks continue to stay undetected for such long periods of time.
When asked whether organizations monitor roaming devices, 50% said no, 28% said yes, and 22% indicated that they partially monitor roaming devices. In a workforce that has embraced remote work, it’s surprising that 50% of organizations do not monitor roaming devices.
Another interesting finding was that approximately 72% of organizations either don’t or only partially monitor the use of network resources and traffic. This is especially interesting as most compromises tend to originate from within the network. Having little to no visibility dramatically increases the risk of a data breach.
Lastly, crypto-mining doesn’t appear to be a concern for the majority of organizations as 76% either do not know or only partially know how to identify it. While there seems to be little concern around crypto-mining it’s important to remember using crypto-jacking may only be the threat actors’ initial monetization tactic. At later stages, cybercriminals can choose to monetize access to your network more aggressively through a ransomware attack.
The Tale of Two Cities
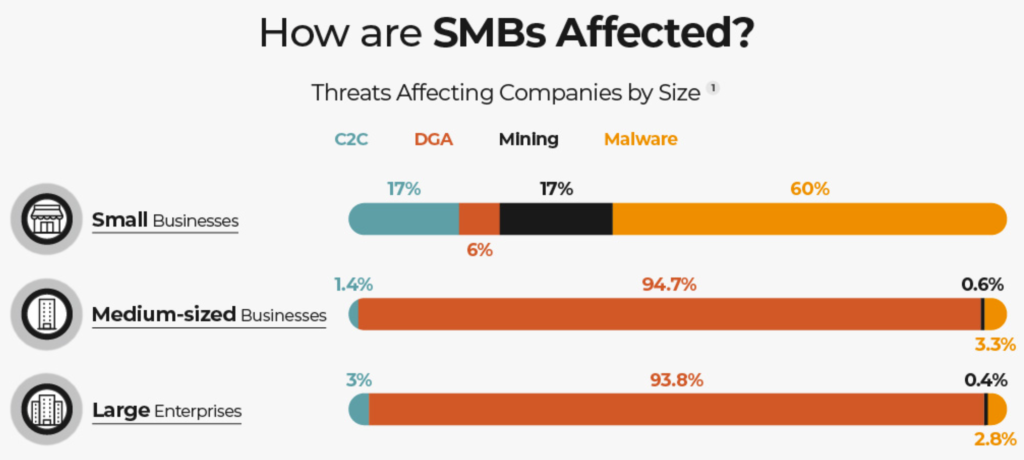
Threat data across Lumu’s 3500 customers tells a very interesting story about attack techniques used and how they vary based on the size of the organization.
Small businesses are primarily targeted by malware attacks, whereas medium businesses and large enterprises tell a very different story. It seems attackers are using more automated methods that are scalable to target medium and large organizations.
Small Businesses Face Varied Threat Vectors
Adversaries are leveraging different techniques when it comes to smaller organizations with Malware leading the way at 60%. Smaller companies are at greater risk of Malware, Command and Control, and Crypto-Mining. Attackers view smaller organizations as having fewer security protocols in place, therefore requiring less effort to compromise.
DGA Is the Play for Medium-sized and Large Enterprises
In stark contrast to small businesses, larger organizations don’t see as much malware.
DGA or Domain Generated Algorithms are most prevalent among larger organizations. This attack technique allows adversaries to dynamically identify a destination domain for command and control traffic rather than relying on a list of static IP addresses or domains.
This has the advantage of making it much harder for defenders to block, track, or take over the command and control channel, as there potentially could be thousands of domains that malware can check for instructions. Using this technique, attackers can target various organizations and bypass security protocols more easily.
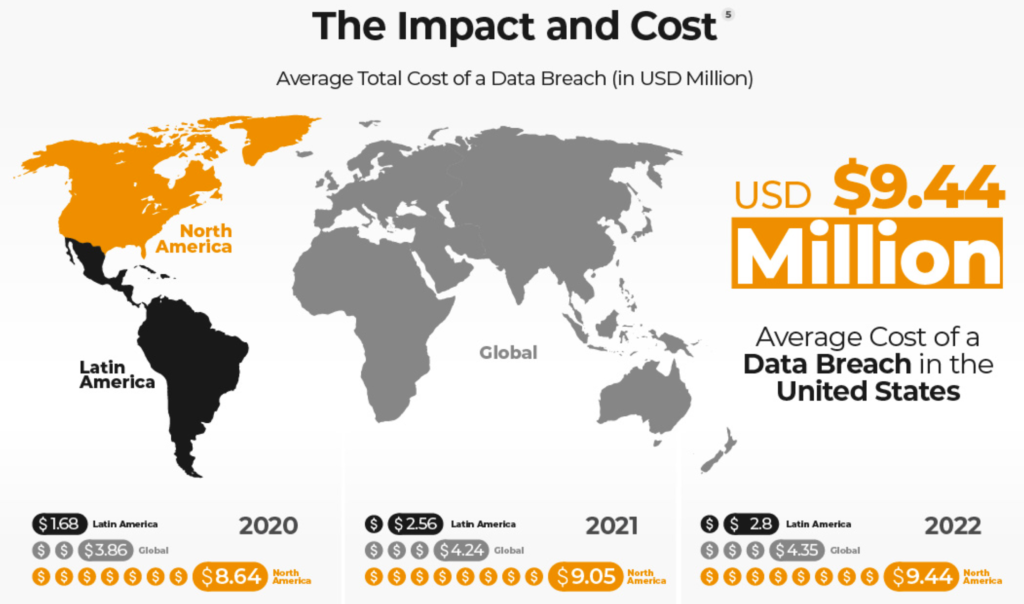
Adversaries Are Facing Inflation, Too
Year over year we continue to see a rise in the average cost of a data breach globally. It comes as no surprise in the last year as most of the world has been facing higher prices in general.
Know Your Own Reality and Act Accordingly
As the data shows in our Compromise Flashcard 2022, cybercrime is affecting organizations differently according to size and industry. There is no silver bullet when it comes to protecting your organization from being compromised. The most important thing is to understand your potential exposure and make sure that your cybersecurity protocols are aligned accordingly.