Is Your BYOD Policy a Gateway for Attackers? Here’s How to Secure It
Reading Time: 5 minsEmbracing remote work creates BYOD security challenges. Learn to secure the personal laptops and phones connecting to your network and protect your business.
Already have an account? Sign in
Sign in
Get the latest cybersecurity articles and insights straight from the experts.
Reading Time: 5 minsEmbracing remote work creates BYOD security challenges. Learn to secure the personal laptops and phones connecting to your network and protect your business.

Reading Time: 3 minsThe recent Akira ransomware attack, which exploited a vulnerable webcam to bypass EDR, underscores the critical need for organizations to adopt a Zero Trust architecture and continuous network monitoring.

Reading Time: 4 minsAchieve comprehensive cloud visibility across your hybrid and multi-cloud environments to proactively detect and respond to network threats.

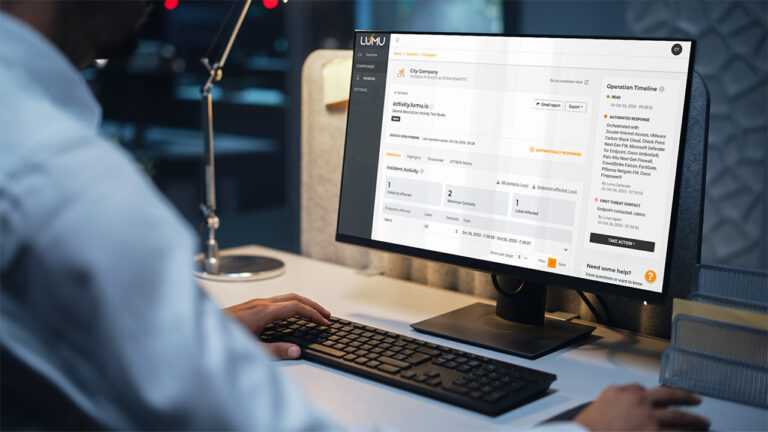
Reading Time: 5 minsLumu has released Lumu Discover, giving real-time, actionable intelligence on your external attack surface.

Reading Time: 2 minsDr. Chase Cunningham discusses the critical need for state and local governments to secure against ransomware, ensuring essential services.
Reading Time: 3 minsIntroducing Lumu for MSPs Lite, a free, AI-driven cybersecurity solution for Managed Service Providers, democratizing advanced threat detection.