
Why EDR Evasion is the New Threat Standard
Reading Time: 4 mins48% of ransomware attacks successfully evade EDR. Threat actors like Qilin are exploiting the ‘tuning gap’ in managed security. We look at how to regain the upper hand.
Already have an account? Sign in
Sign in
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 4 mins48% of ransomware attacks successfully evade EDR. Threat actors like Qilin are exploiting the ‘tuning gap’ in managed security. We look at how to regain the upper hand.

Reading Time: 6 minsFresh from DEFCON 33, Lumu’s Mario Lobo identifies a revolutionary shift in AI-driven attacks that is changing the rules for cyber defenders and their tools.

Reading Time: 4 minsAs global cybersecurity event, RSAC 2025, wraps for another year, Ricardo Villadiego, CEO of Lumu Technologies, reflects on the pulse of the cybersecurity industry.

Reading Time: 3 minsThe recent Akira ransomware attack, which exploited a vulnerable webcam to bypass EDR, underscores the critical need for organizations to adopt a Zero Trust architecture and continuous network monitoring.

Reading Time: 7 minsEndpoint Detection and Response (EDR) has a critical role in most companies’ security setup, but cybercriminals are mastering EDR bypass tactics. How can we defend against them?
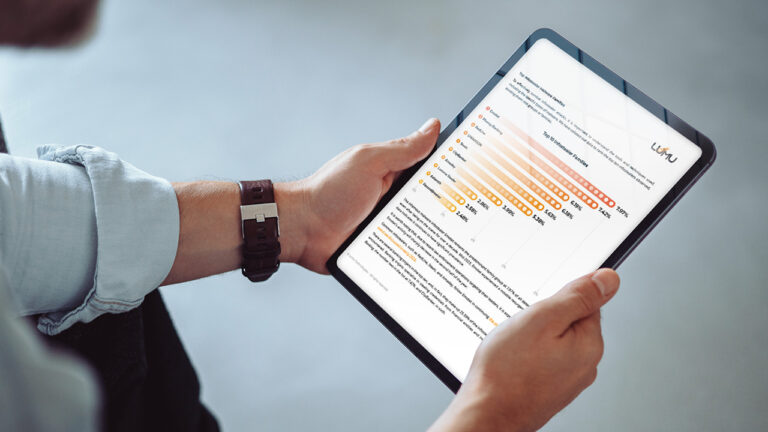
Reading Time: 5 minsLumu’s Compromise Report for 2024 uncovers surprising information about how infostealer malware has increasingly targeted US organizations, local government, and education establishments.
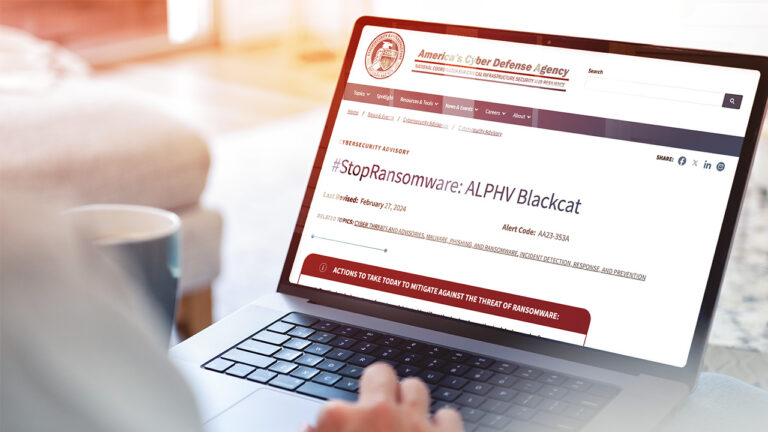
Reading Time: 4 minsRansomHub is a new ransomware group offering Ransomware as a Service that has already encrypted and exfiltrated data from at least 210 victims. How does RansomHub bypass defenses and how can you defend against it?
Reading Time: 7 minsMario Lobo, Cybersecurity Specialist at Lumu Technologies, recently attended DEFCON – a hacker convention held annually in Las Vegas, Nevada – and he highlights his big takeaways.

Reading Time: 4 minsXDR is the latest acronym to be buzzing around the cybersecurity industry. But does it solve the problem of ever-increasing data breaches?