April, 2026
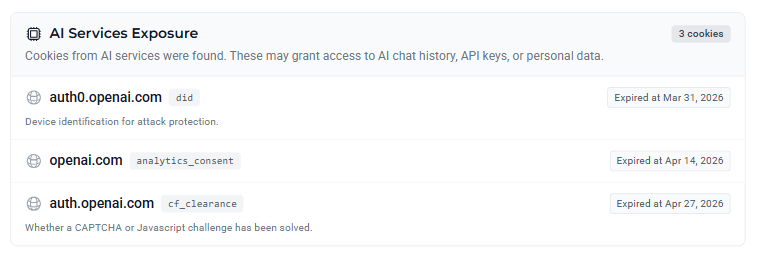
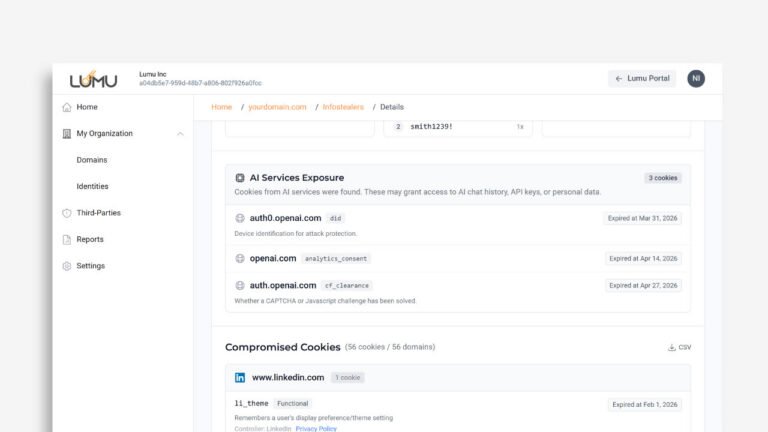
While password theft is a major threat, modern attackers rely heavily on session cookies and system-level persistence to bypass security controls. We’ve enhanced Lumu Discover to give you full visibility into Infostealers-related incidents, with one of the biggest additions being the AI Services Exposure section.
Here’s a look at the data you can expect to see in this new view:
Compromised AI Services
As teams lean more into AI, attackers are pivoting to steal session cookies for platforms like OpenAI. If an attacker grabs a session token, they don’t need a password to see your company’s sensitive AI history. With this feature, you can pinpoint exactly which AI sessions have been compromised, allowing you to quickly secure sensitive data.
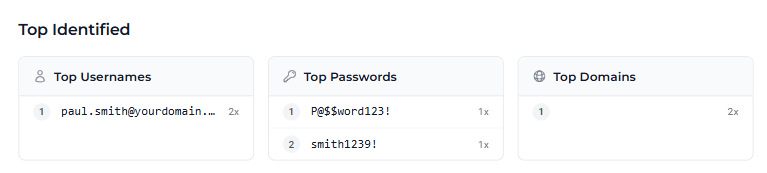
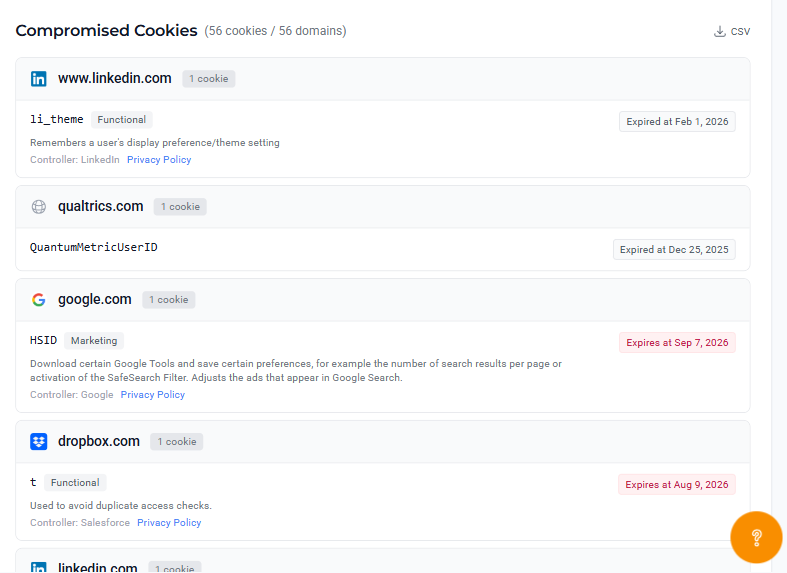
Compromised Credentials & Session Tokens
A stolen password is a major risk, but a stolen session cookie allows an attacker to bypass MFA entirely. Lumu now shows you both. By seeing exactly which domains (Microsoft, Google, LinkedIn) and users have active session exposure.
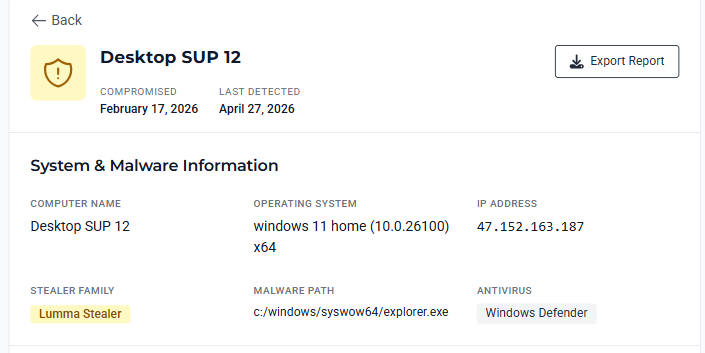
Malware Context
Infostealers often hide in plain sight. Lumu surfaces the specific infection path and malware type (e.g., Lumma Stealer), providing the deep visibility needed to identify persistence and ensure that once a threat is removed, it doesn’t come back.