Table of Contents
Remcos began as a legitimate remote administration utility but has become one of the most widely deployed Remote Access Trojans (RATs) in the threat landscape. The RAT was initially used for data theft but has evolved into a real-time surveillance platform.
New variants discovered in January and February 2026 no longer wait to upload stolen files. They now stream webcam footage and transmit keystrokes instantly to attackers. This shift to ‘surveillance as a service’ allows threat actors to easily monitor infected networks live.
The latest campaigns use text-based staging and legitimate Microsoft tools (LOLBins) to bypass standard security filters. Attackers blend encrypted command traffic into normal web noise, invisible to traditional signature-based defenses.
Quick Facts: Remcos RAT
See a quick overview in our Lumu Threat Glossary. |
How Did Remcos Evolve From a Legitimate Tool?
Remcos evolved from a legitimate administration product into malware when threat actors weaponized its advanced features for cybercrime. Breaking Security released the utility in 2016 and criminals quickly purchased licenses to exploit its clean codebase and evasion capabilities.
The tool appeared on underground forums in 2016, costing between $58 and $389. Phishing campaigns targeting government agencies began by 2017. It had a modular architecture, so operators could easily extend functionality through plugins.
Remcos became a staple for initial access brokers by 2020. These middlemen compromise networks to sell access to ransomware operators. Its asynchronous communication model for Command and Control (C2) allowed traffic to blend into normal network noise. This made signature-based detection unreliable.
Threat actors refined delivery mechanisms between 2022 and 2025 with campaigns shifting to fileless execution. Phishing emails led to Office document exploits, which dropped PowerShell loaders. The loaders then retrieved Remcos payloads from cloud infrastructure. The RAT then ran entirely in memory.
But 2026 has brought a qualitative leap.
What Is the SHADOW#REACTOR Campaign?
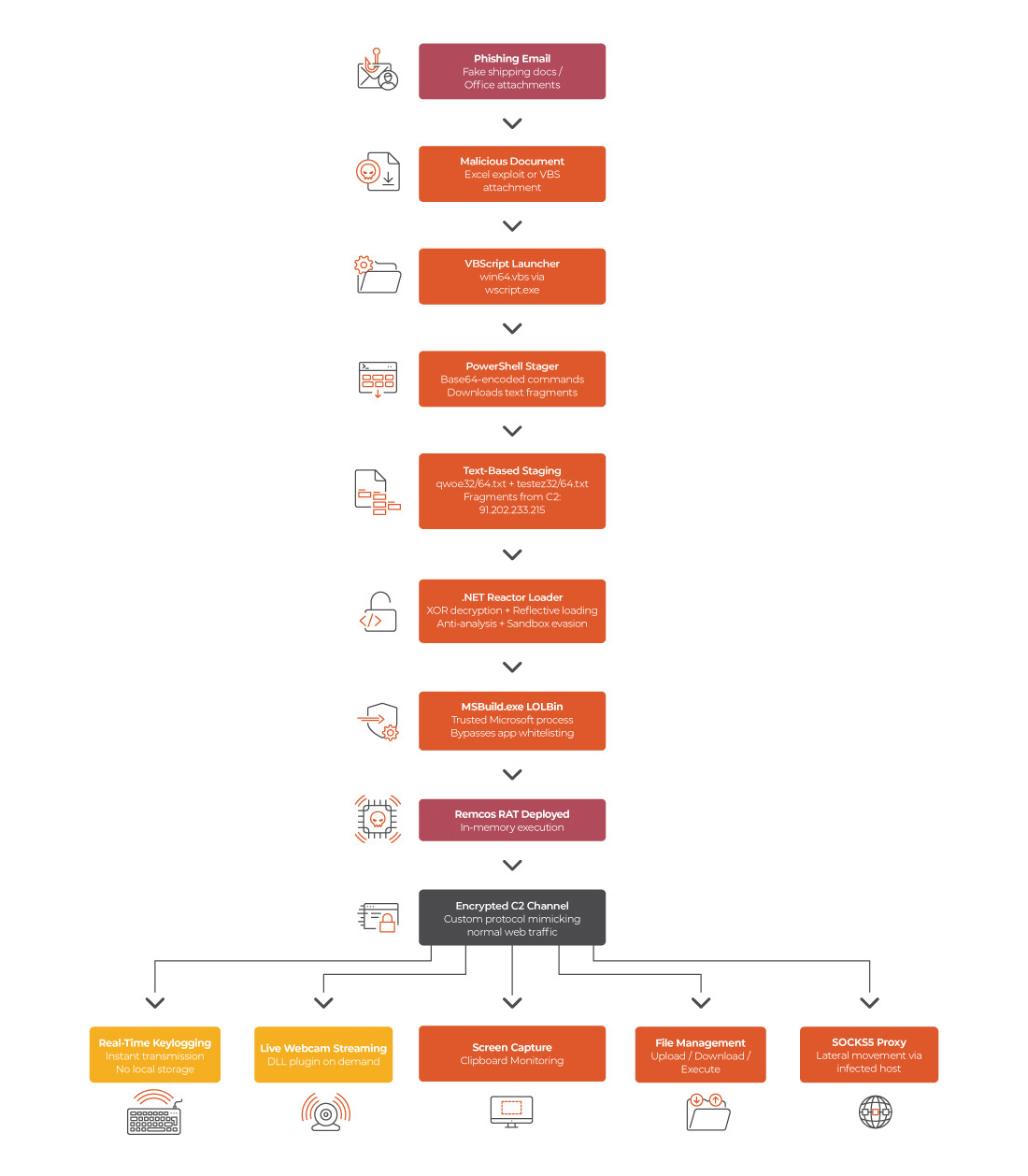
In January 2026, the Securonix Threat Research team published an analysis of a campaign they track as SHADOW#REACTOR. This is a sophisticated campaign designed to evade traditional defense layers by using text-based staging. Attackers fragment the toolchain into plain-text files hosted on remote infrastructure rather than delivering compiled binaries. Most security tools rarely alert on plain text.
The infection chain exploits this blind spot. It begins with an obfuscated VBScript (win64.vbs) that launches PowerShell. It then retrieves text fragments from a remote server (91.202.233[.]215). These files are named qpwoe32.txt or qpwoe64.txt depending on the system architecture.
Here is where it gets clever. The system does not execute them immediately. It reconstructs them in-memory into encoded loaders. A .NET Reactor assembly decodes them and the reactor obfuscation layer (a commercial code protection tool) performs seeded XOR string decryption, reflective in-memory loading, and anti-analysis checks.
The final execution leverages MSBuild.exe, a trusted Microsoft build tool. Attackers use it as a Living-off-the-Land Binary (LOLBin) to execute the malware. This rarely raises alarms in environments using application whitelisting.
Once MSBuild completes execution, the Remcos RAT backdoor is fully deployed with interactive shell access, file management capabilities, and persistent remote control.
The campaign also implements a self-healing mechanism. The stager pauses and re-downloads if a fragment is incomplete or corrupted. This ensures network interruptions do not break the infection chain.
Securonix assesses that the SHADOW#REACTOR campaign is broad and opportunistic. It primarily targets enterprise and small or medium-sized business environments. This is consistent with initial access broker activity rather than state-sponsored operations.
How Does the February 2026 Variant Change the Threat?
The variant analyzed by Point Wild’s Lat61 threat intelligence team in February 2026 represents a fundamental shift in capability. Remcos RAT is moving from data theft to real-time surveillance.
Traditional Remcos variants operated on a ‘store-and-exfiltrate’ model that saved data locally before uploading it (typically to C:\ProgramData\colors\logs.dat). For example, screenshots were captured periodically and uploaded to the C2 server in batches. This approach left forensic artifacts, such as local log files, or periodic upload traffic. Defenders could detect and use this for incident response.
The new variant streams data instantly to attacker-controlled servers. This eliminates forensic artifacts. The online keylogger transmits keystrokes as they are typed, writing no intermediate file to disk. The webcam module enables live video streaming from the victim’s camera.
The developers overhauled the C2 communication channel. The malware uses a custom protocol designed to resemble normal web traffic. It employs encrypted channels to complicate deep packet inspection. Configuration data is decrypted only at runtime, and critical Windows APIs are loaded dynamically rather than being statically linked. This reduces the surface available for static analysis.
This variant also introduces modular plugins delivered as Dynamic Link Libraries (DLLs). This means the operator can extend Remcos’s functionality post-infection without deploying new payloads or triggering additional download alerts. This modular architecture turns a single infection into an adaptable, long-term surveillance platform.
Which Regions and Industries Are Most at Risk?
Technical evolution is only one part of the story. Security leaders must understand where the threat is hitting right now. Remcos operators show a strong preference for Latin American and North American targets. They attack a wide surface that spans virtually every major sector, with education and nonprofits bearing the heaviest burden.
Data from the Lumu Maltiverse Threat Observatory shows a distinct geographic concentration. The observatory tracks over 10,200 Indicators of Compromise (IoCs). The distribution reveals a clear pattern across the Americas.
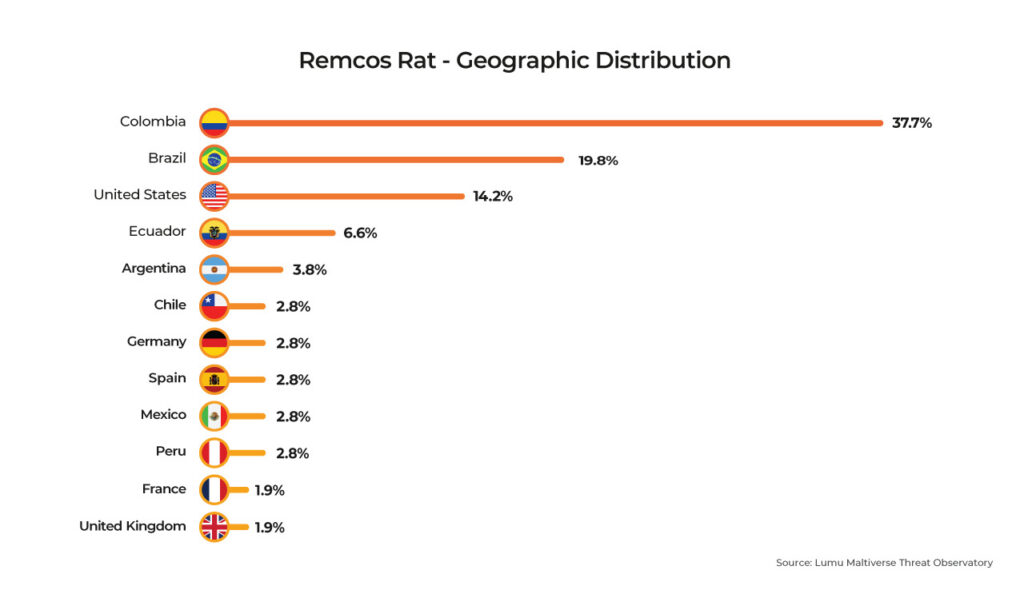
Colombia leads in Remcos activity. Brazil and the United States follow closely. Ecuador, Argentina, Chile, Mexico, and Peru round out this concentration of Latin American Countries. European presence is lighter but still significant.
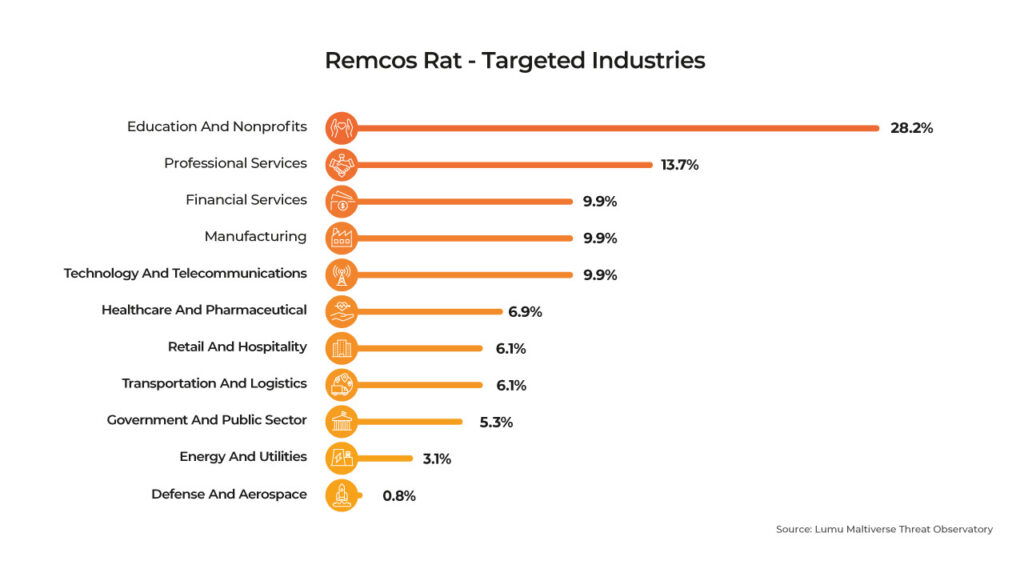
The industry breakdown reveals significant risks for specific sectors. Education and nonprofits bear the brunt of the attacks. These sectors are often underfunded but hold valuable data. Professional services are the next major target. These firms act as valuable supply chain entry points into larger organizations. Financial services, manufacturing, and technology are also primary targets. It is clear, however, that no sector is completely immune.
This data is valuable as it reflects live intelligence. The distribution shifts as new campaigns emerge and old infrastructure falls. Security teams can monitor these patterns in real time through the Maltiverse intelligence search.
How Does the Remcos Attack Lifecycle Operate?
The attack lifecycle relies on deceiving both the user and the system’s security architecture. The SHADOW#REACTOR campaign and the February 2026 variant follow a multi-stage flow designed to establish persistent, stealthy surveillance. The process begins with human error and ends with an encrypted, real-time command channel.
The infection chain starts with a phishing email carrying a malicious attachment. This triggers a sequence of obfuscated scripts and legitimate Microsoft tools to evade detection. The system reconstructs the malware entirely in memory. Once deployed, Remcos establishes an encrypted connection to the attacker’s server. This connection mimics normal web traffic while facilitating live surveillance and data theft.
How Do Remcos Tactics Map to the MITRE ATT&CK Framework?
Recent Remcos RAT (MITRE ID: S0332) campaigns utilize a broad spectrum of tactics across the attack lifecycle. The malware relies heavily on defense evasion and collection techniques. This allows attackers to maintain stealth while maximizing data extraction. Security teams can use this framework mapping to build targeted behavioral detections.
The table below outlines the specific techniques observed in the SHADOW#REACTOR campaign and the real-time February 2026 variants.
Tactic | Technique | ID | Description |
Initial Access | Phishing: Spearphishing Attachment | T1566.001 | Malicious Office documents and VBS files delivered via email |
Execution | Command and Scripting Interpreter: VBScript | T1059.005 | Obfuscated VBS launcher (win64.vbs) initiates infection chain |
Execution | Command and Scripting Interpreter: PowerShell | T1059.001 | PowerShell stager downloads and reconstructs payloads in memory |
Execution | Trusted Developer Utilities Proxy Execution: MSBuild | T1127.001 | MSBuild.exe used as LOLBin for final Remcos execution |
Persistence | Boot or Logon Autostart Execution: Registry Run Keys | T1547.001 | Adds entries to HKCU\Software\Microsoft\Windows\CurrentVersion\Run |
Privilege Escalation | Abuse Elevation Control Mechanism: Bypass UAC | T1548.002 | Built-in UAC bypass capability |
Defense Evasion | Obfuscated Files or Information | T1027 | RC4 encryption, base64 encoding, .NET Reactor code protection |
Defense Evasion | Process Injection | T1055 | Injects into legitimate processes to avoid detection |
Defense Evasion | Modify Registry | T1112 | Maintains registry control for persistence and configuration |
Defense Evasion | Virtualization/Sandbox Evasion: System Checks | T1497.001 | Detects Sandboxie, VMware, and analysis environments |
Credential Access | Input Capture: Keylogging | T1056.001 | Real-time keylogging with instant C2 exfiltration |
Collection | Audio Capture | T1123 | Captures microphone data from compromised systems |
Collection | Video Capture | T1125 | Live webcam streaming via on-demand DLL plugin |
Collection | Screen Capture | T1113 | Automated and on-demand screenshot capture |
Collection | Clipboard Data | T1115 | Steals and monitors clipboard contents |
Command and Control | Ingress Tool Transfer | T1105 | Downloads additional modules and uploads stolen data |
Command and Control | Proxy | T1090 | Uses infected hosts as SOCKS5 proxies for lateral movement |
Command and Control | Application Layer Protocol | T1071 | Custom encrypted protocol mimicking normal web traffic |
What Are the Latest Remcos Indicators of Compromise?
Security teams must track active infrastructure to defend against Remcos. Recent campaigns leave specific traces across networks and endpoints. You can use these indicators to hunt for threats and block malicious activity.
How Can Organizations Defend Against Remcos?
Defending against Remcos requires a layered approach. Security teams must address both the sophisticated delivery mechanisms and the real-time surveillance capabilities of the latest variants. A single point of defense will fail.
Network Level Defenses
Organizations should monitor for anomalous outbound connections. Look for persistent and low-bandwidth encrypted channels, characteristic of Remcos C2. DNS monitoring is critical. Remcos campaigns consistently use Dynamic DNS services like DuckDNS. Monitor DNS queries to these providers and correlate them with outbound TLS connections. This can reveal compromised endpoints that signature-based tools miss.
Endpoint Level Defenses
You must monitor for suspicious process lineages as attackers abuse MSBuild.exe as a trusted proxy. PowerShell spawning MSBuild.exe is not a normal business process. Behavioral detection rules are more reliable than signature-based detection against these multi-stage campaigns.
Email Security Controls
Phishing remains the primary vector for initial access. Train employees to recognize suspicious shipping documents and unexpected Office attachments. Organizations should consider disabling macros by default. You should also restrict VBScript execution through Group Policy.
Surveillance and Post-Compromise Detection
Organizations should monitor for unexpected webcam and microphone access at the operating system level. Dynamic DLL loading means post-compromise capability can expand without download alerts. This makes initial detection and rapid containment critical.
Proactive Threat Intelligence Integration
Integrate proactive threat intelligence to stay ahead. Check indicators against up-to-date feeds to identify compromised infrastructure early. Understanding active indicators transforms a static blocklist into an adaptive defense.
Ready to Upgrade Your Threat Intelligence? Stay ahead of emerging threats like the Remcos RAT. Maltiverse provides real-time visibility and actionable indicators to secure your enterprise. Open a free Maltiverse account today.




