Table of Contents
What Are Infostealers?
Infostealers are a class of malicious software designed to collect and exfiltrate data from systems or networks without user consent. These stealth programs, often driven by financial or criminal motives, aim to exfiltrate sensitive information, posing significant risks to both individuals and organizations.
The first observed modern infostealer dates back to early 2007 and was known as ZeuS or Zbot. The main objective of the malware was to steal online banking credentials and quickly became one of the most widespread and sophisticated banking trojans ever seen. In 2011, the source code was publicly released, leading to the proliferation of numerous new variants.
Over the years, technological advancements and the underground economy have facilitated the development and proliferation of new infostealer variants, with cybercriminals continuously improving their tactics to evade detection and maximize profits. Today, infostealers remain a prevalent and potent threat, posing serious risks to individuals, businesses, and organizations worldwide.
Increasingly, infostealers are being used as an entry point in sophisticated cyber attacks, underscoring their role as a fundamental threat vector in modern cybercrime.
How Do Infostealers Work?
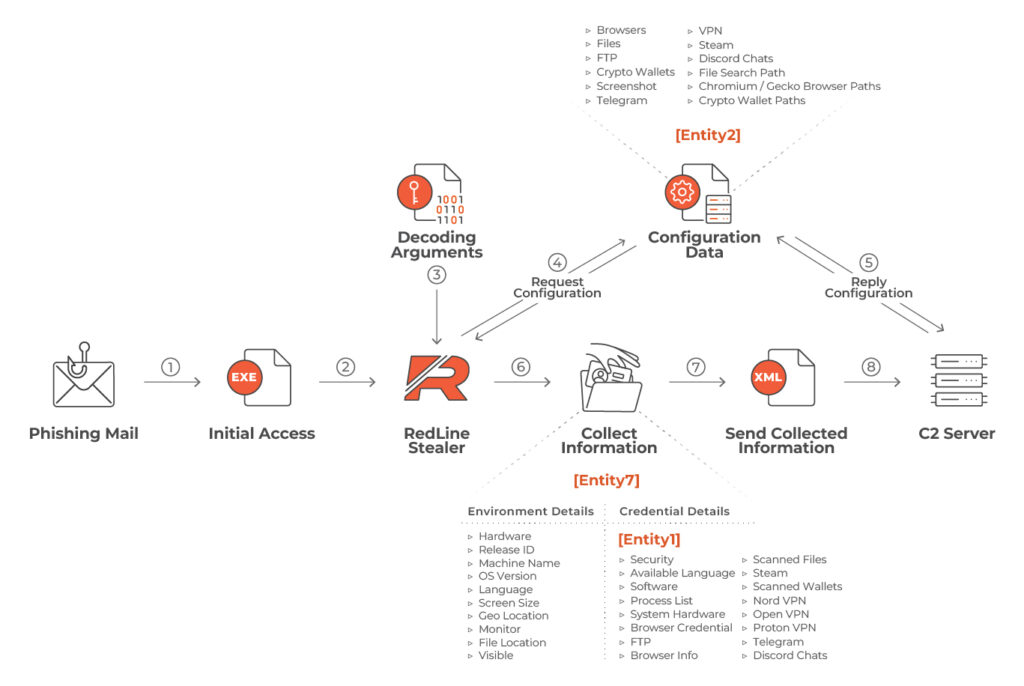
The main function of an infostealer is to clandestinely collect sensitive information from victims through various techniques such as enumerating files and directories, logging keystrokes, extracting browser data, accessing files, copying cookies and taking screenshots. The stolen data is then transmitted to a command and control server controlled by the attacker.
As is common with modern malware, infostealers have transitioned to a Malware as a Service (MaaS) model. This facilitates attackers with minimal expertise in targeting companies by utilizing such services to infiltrate systems and extract information, often in the format of logs. Subsequently, these logs are sold on underground forums and criminal marketplaces on the dark web.
Data most frequently targeted by infostealers:
- System Configuration information
- Account credentials
- Browser data such as cookies and extension data
- Credit cards
- Crypto wallets
- Autofill information
Infostealers are distributed over several channels including phishing, spread phishing, and malvertising. Additionally, uncommon distribution methods include SEO Poisoning, fake software, and public social network posts.
Common Distribution Channels
Phishing: This is a common method of distributing several malware families, usually cybercriminals send documents such as PDFs, HTML files, or those from MS Office containing malicious payloads or camouflaged URL links to download the artifacts. To try to evade detection, files are often encrypted with passwords, rendering it challenging for email providers to scan for malicious content.
Legitimate software instrumentation: This is a classic infection vector, users can be easily infected when installing illegitimate software. Modified versions often harbor embedded malicious code, making them a significant risk to inexperienced users.
Malversiting: This trend started while back in 2017 and is currently on a surge, malicious actors distribute malicious payloads through some high-rank pages, oftentimes impersonating updates for popular software, like Google Chrome.
The Infrastructure Behind an Infostealer Botnet
The following is the topology of Redline Stealer, a typical modern infostealer.
Analyzing Stolen Information
The information collected by infostealers is focused on specific objectives. On one hand, it aims to acquire sensitive data like banking portal credentials, cryptocurrency wallets, email account details, social media credentials or any information that could be exploited for future misuse. On the other hand, infostealers also gather technical details about the compromised system, including session cookies, UserAgents, machine specifications, and log files. These technical insights allow attackers to simulate the environment of targeted accounts, evading security measures and attempting unauthorized access without environmental restrictions.
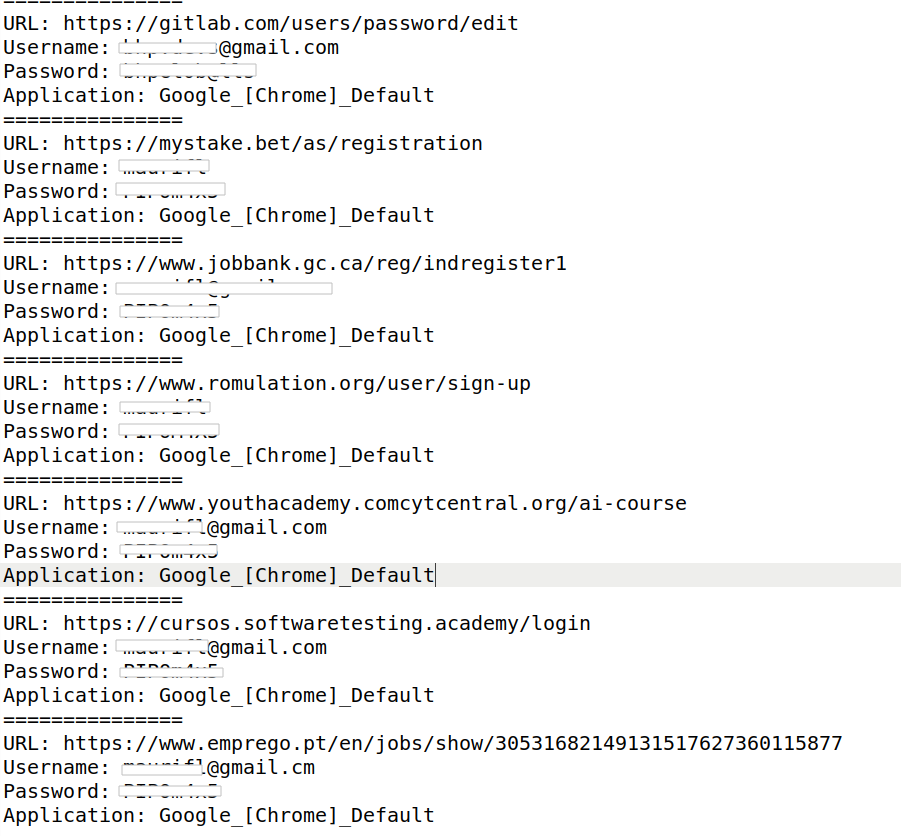
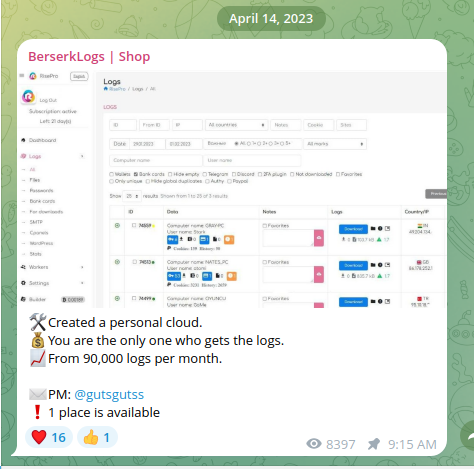
Below is an example of information stolen by a real MaaS infostealer.
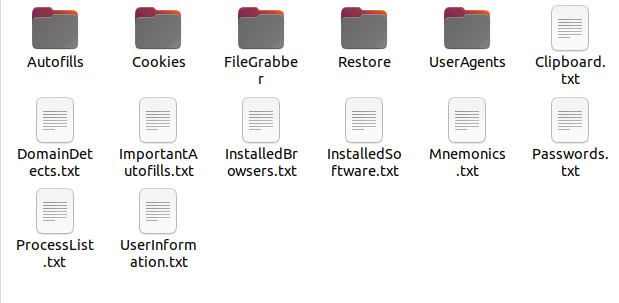
Most infostealers possess the capability to identify multiple login portals and extract credentials. After it, they format this information into structured logs, employing various techniques to transmit them to adversarial infrastructure (exfiltration). This allows attackers to easily access and exploit sensitive information collected from compromised systems.
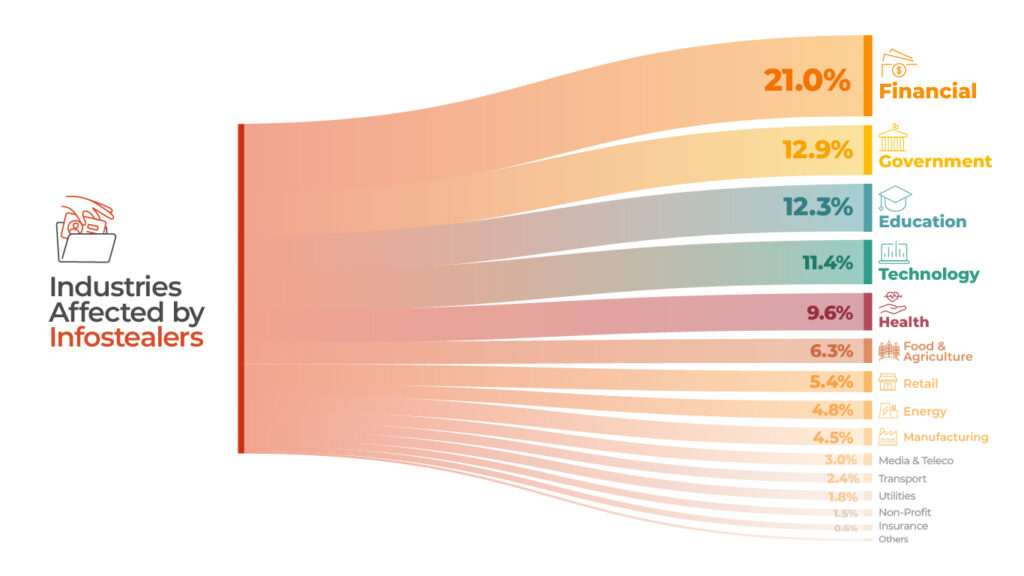
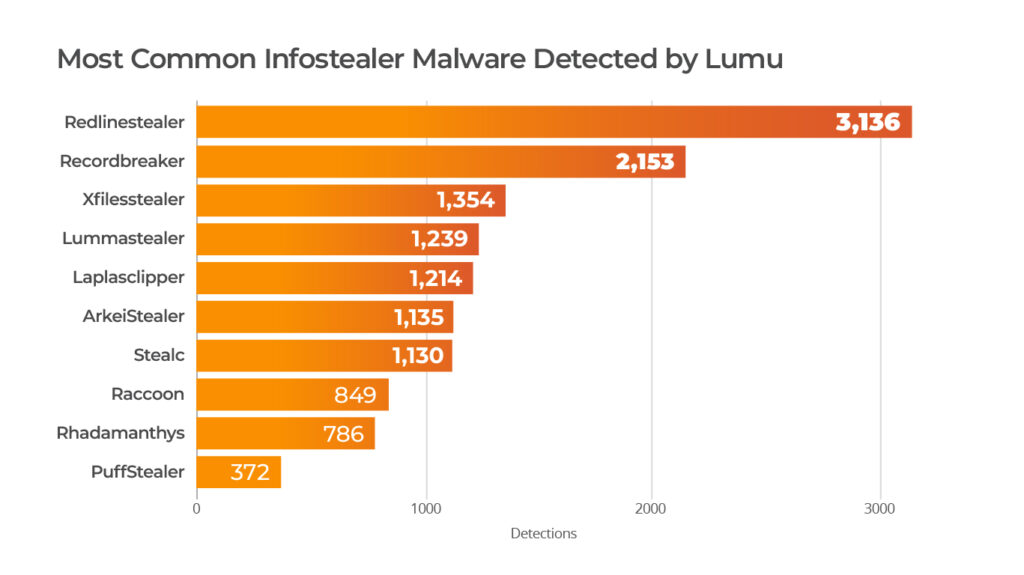
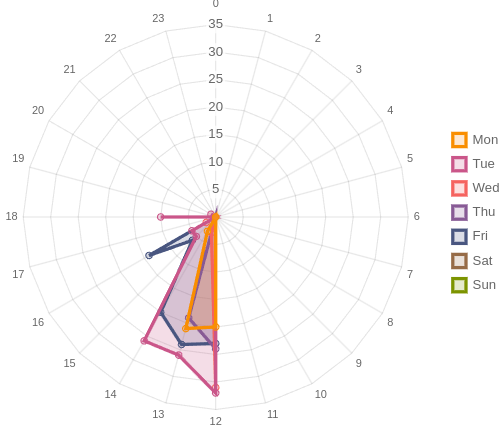
Stats from the Dark World
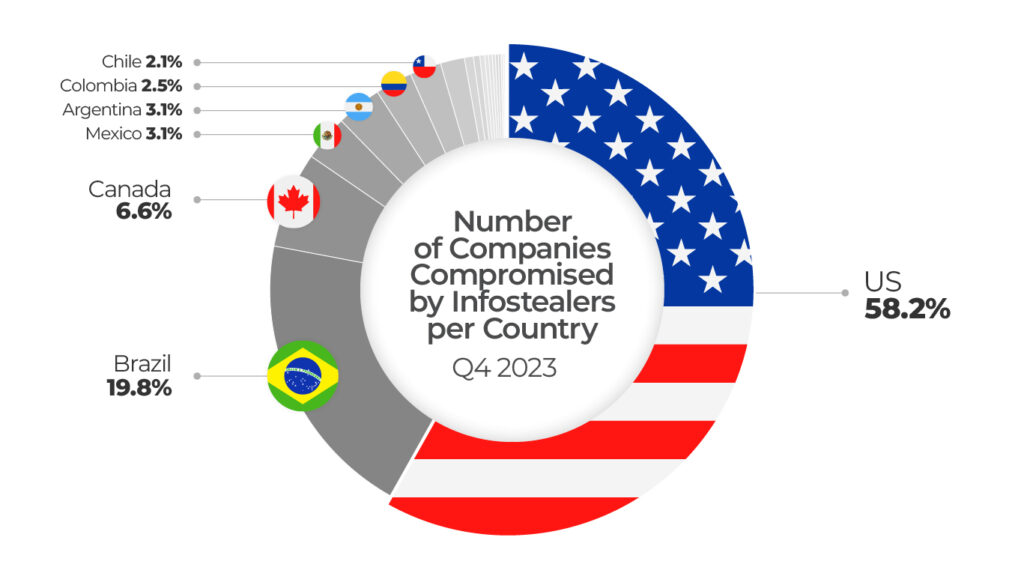
Source: Hudson Rock
Infostealers and the Cybercrime Economy
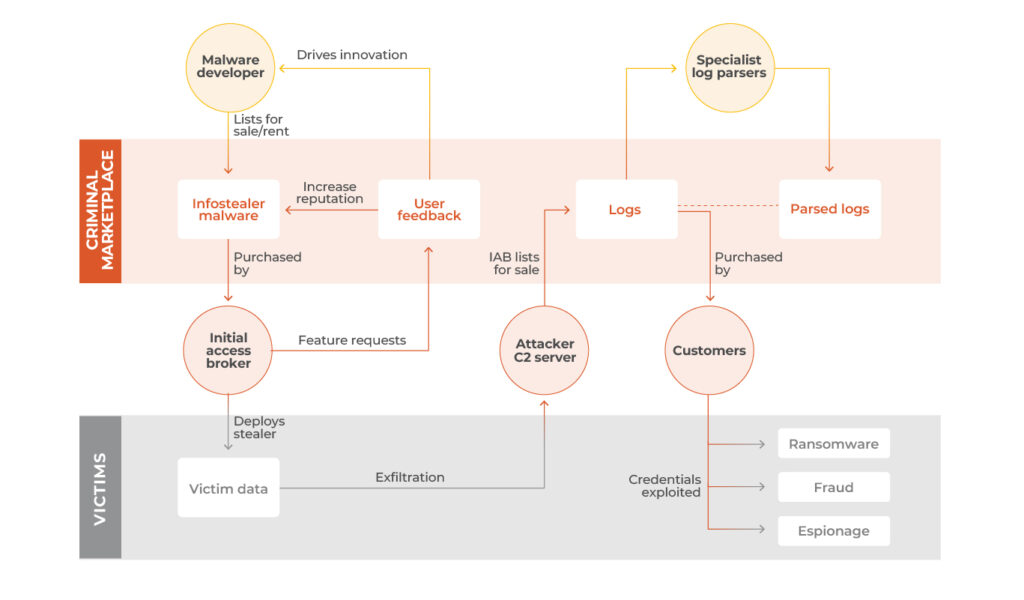
Figure: Infostealers ecosystem
Behind information theft lies an intricate cybercriminal ecosystem with diverse roles and profit levels. Researchers from SecureWorks identify at least four tiers:
Developers and Information Experts: Tasked with creating programs to steal data while evading cybersecurity measures. This level thrives on market demand for specific features tailored to targets.
Criminal Marketplaces: The second tier, also known as Initial Access Brokers (IABs), operates on dark web forums, offering services and access ranging from $50 to $1000 USD, depending on the infostealer type. Customers, typically malicious actors leveraging industry-specific knowledge, utilize this Initial Access for sophisticated attacks like ransomware. The rise of Ransomware as a Service (RaaS) has heightened the importance of IABs, streamlining intelligence gathering and reconnaissance, enabling attackers to initiate attacks with a solid initial vector.
Dark Support Infrastructure: These offshore support services are dedicated to maintaining anonymity for cybercriminals. In the latest Models as a Service (MaaS), this infrastructure is managed by the owners of the malware services themselves.
Victims: Ultimately, victims of such attacks, under pressure from various factors, succumb to paying ransom to criminal gangs. This payment is made to prevent the publication of sensitive data or decrypt crucial information essential for business continuity. Unwittingly, these actions contribute to the perpetuation of the criminal economic cycle.
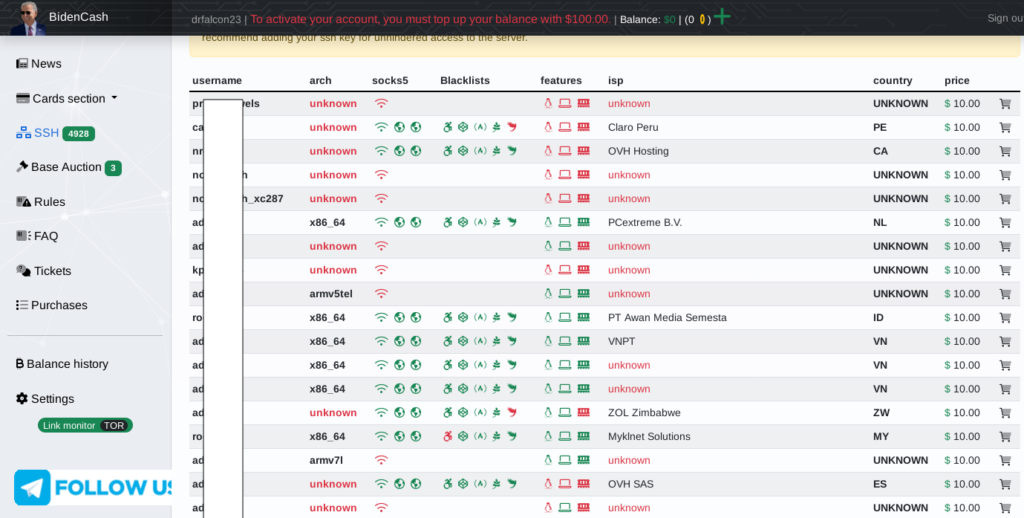
There are several forums that sell information on the dark web, like 2easy, BidenCash and Russian Market. There is also a recent trend to sell that information on decentralized stores and social media platforms like Telegram and others.
BidenCash Market
Telegram BerkserkLogs Market
Several Threat Actors have been seen using Initial Access Brokers to compromise networks and perform large scale attacks, like Lockbit 3.0, Royal Ransomware, BlackHunt, Medusa, and others.
Has Your Network Been Compromised by InfoStealers?
Threat actors constantly scan the internet for fresh targets. The more information they possess about a company, the greater their possibility to infiltrate the infrastructure. Weak security measures to decrease the attack surface, enabling attackers to identify and exploit vulnerabilities effortlessly. Moreover, the ease of acquiring credentials or access to environments facilitates illicit activities, allowing malicious actors to operate easily.
At present, several companies remain unaware that multiple of their employee credentials are being sold on the dark web. Quietly, attackers hold the key to initiating large-scale attacks.
Observe Your Network Activity
Lumu’s Continuous Compromise Assessment allows you to identify when, where, and how your infrastructure is communicating with adversaries, you gain the visibility you need of what is happening anytime in your network. The robust process of cyber threat intelligence provides you with crucial information to safeguard your infrastructure and effectively mitigate threats across multiple stages of the infection chain.
Lumu tracks malicious infrastructure that distributes, communicates or controls malware, phishing, spam, malvertising and different types of threats and techniques, and alerts your company when the enemy comes knocking.
Mitre Map of Infostealer Malware
Tactic | Technique |
Reconnaissance | T1589 Gather Victim Identity Information |
Reconnaissance | T1598 Phishing for information |
Resource Development | T1583.001 Acquire Infraestructure: Domains |
Resource Development | T1585.001 Establish Accounts: Social Media Accounts |
Initial Access | T1566: Phishing |
Initial Access | T1204.002: Malicious File |
Initial Access | T1189 Drive-by Compromise |
Initial Access | T1199: Trusted Relationship |
Initial Access | T1078.002 Valid Accounts: Domain Accounts |
Execution | T1059.003: Windows Command Shell |
Execution | T1059.001: PowerShell |
Execution | T1648 Serverless execution |
Execution | T1204 User execution |
persistence | T1136 Create account |
Privilege escalation | T1484.002 Domain Policy modification |
Defense Evasion | T1564.001: Hidden Files and Directories |
Defense Evasion | T1070.004 Indicator Removal File Deletion |
Defense Evasion | T1578.002 Modify Cloud Compute Infraestructure |
Defense Evasion | T1497.001 System Checks |
Credential Access | T1555.003: Credentials from Web Browsers |
Credential Access | T1555 Indicator RemovalFile Deletion |
Credential Access | T1606 Forge Web Credentials |
Credential Access | T1621 Multi-Factor Authentication Request Generation |
Credential Access | T1552 Unsecure Credentials: Credentials in files |
Discovery | T1087: Account Discovery |
Discovery | T1217: Browser Information Discovery |
Discovery | T1046: Network Service Discovery |
Discovery | T1057: Process Discovery |
Discovery | T1012: Query Registry |
Discovery | T1518: Software Discovery |
Discovery | T1016: System Network Configuration Discovery |
Discovery | T1614: System Location Discovery: System Language Discovery |
Discovery | T1083: File and Directory Discovery |
Discovery | T1082: System Information Discovery |
Discovery | T1033: System Owner/User Discovery |
Discovery | T1538: Cloud Service Dashboard. |
Discovery | T1018: Remote System Discovery |
Discovery | T1539: Steal web session cookie |
Collection | T1113: Screen Capture |
Collection | T1119: Automated Collection |
Collection | T1115: Clipboard Data |
Collection | T1005: Data from Local System |
Collection | T1056.001: Keylogging |
Command & Control | T1102: Web Service |
Command & Control | T1102.002: Bidirectional Communication |
Exfiltration | T1041: Exfiltration Over Command-and-Control Channel |
Exfiltration | T1020: Automated Exfiltration |
Exfiltration | T1048: Exfiltration Over Alternative Protocol |
Adopt Strategies to Minimize Your Attack Surface
This silent adversary takes advantage of any inadvertent information divulged by companies. Every service that companies expose to the internet must undergo risk analysis. Companies need to adopt strategies to assess their exposed infrastructure and determine its necessity in terms of business operations. Access should be restricted using methods of least privilege in their networks and authentication systems.
The adversary will try to communicate with your infrastructure and you must be prepared to detect it.
Check Your Devices
It’s crucial to have monitoring tools in place to keep track of your device services, detecting any suspicious behavior promptly. If your company has an EDR, it is essential to maintain it up-to-date.
Protecting Against Infostealers
Cybersecurity operators looking to protect against the threat posed by infostealers can take the following actions:
- Establish an effective strategy for the continuous monitoring of network and endpoint activity to detect any suspicious activity.
- Make sure that any communication between your network and adversarial infrastructure is being blocked. With Lumu’s 125+ integrations, any detected contacts are immediately blocked using existing cybersecurity infrastructure.
- Enforce the principle of least privilege to ensure that users have access to services and permissions for their job functions and no more.
- Do not expose unnecessary services. Users are advised to disable their Remote Desktop Protocols (RDPs) if not in use, if required, it should be placed behind the firewall and users are to bind with proper policies while using an RDP.
- Get to know if there are compromised credentials.
- Familiarize employees with a proper procedure for opening digital documents.
- Tune your spam defenses.
- Establish a Sender Policy Framework (SPF) for your domain.
Conclusion
The stealth and sophistication of infostealer malware present a clear and present danger to global cybersecurity. Originally designed for data theft, infostealers now provide cyber adversaries with a potent tool for Initial Access, thereby setting the stage for more devastating attacks. Organizations must prioritize the detection and mitigation of infostealers as part of a comprehensive cybersecurity strategy. By remaining vigilant, continuously monitoring for suspicious activity, and employing advanced threat detection and response mechanisms, we can significantly reduce the risk posed by these silent threats.




