Table of Contents
Zero days can be the most devastating of all cyber attacks given that they come from vulnerabilities that are unknown before the attack. This very quality leaves many asking if it is possible to establish a robust defense against zero day attacks.
The vulnerabilities that are exploited in zero day attacks lie in the code, unnoticed until the attack is detected. The term ‘zero day vulnerability’ refers to a flaw that’s discovered before the developer even knows it exists — meaning you have zero days (or even zero minutes) to fix it before attackers can exploit it.
As a result, cyber defenses aren’t prepared to deal with a zero day attack. You need to ask yourself how well and how quickly your cybersecurity infrastructure can react if (or when) a zero day attack evades your security controls. What components do you need to consider? For effective defense, organizations need to ensure they build both zero day attack detection and zero day attack prevention into their security structure.
Before we discuss that in more detail, we should consider how zero day attacks happen and what particular difficulties and dangers they present to defenders.
What Is a Zero Day Attack?
Zero day vulnerabilities can affect operating systems, web browsers, applications, firmware, Internet of Things (IoT) devices, and even network devices. Anything that uses code — from complex enterprise software to a simple IoT device — potentially has a zero day vulnerability ready to be found.
What do we mean by code? Almost everything, nowadays, can have code, whether that’s software code, like a web browser or operating system, firmware code, like in a router or printer, or web application code, such as for a banking website.
A zero day event begins when the vulnerability is found in the code — an attacker can then exploit the vulnerability until the vulnerability is patched. The time gap between the vulnerability being found and the patch being installed is the danger zone.

This danger zone has become even more hazardous in recent years due to AI. When a zero day vulnerability is found, it is added to the Common Vulnerabilities and Exposures (CVE) database so that organizations are aware of the danger and can take measures to defend themselves. However, with the help of Large Language Models (LLMs), attackers can find zero day vulnerabilities on the CVE and write exploit code in seconds to take advantage of this.
There is an additional danger to take into consideration. A SecOps team might be forgiven for thinking that after they apply the patch everything goes back to normal — however, the recent Fortinet incident is evidence that this is not always the case. Hackers may gain a foothold in your network through the vulnerability that can be exploited even after the patch has been applied. In other words, the attacker might be sleeping within your network, making continuous compromise assessment essential, not only during the ‘window of opportunity’ but far beyond the zero day attack’s apparent resolution.
A Zero Day Vulnerability Is Not a Silver Bullet
It is important to note that a zero day vulnerability does not result in an attack in isolation. It is not a silver bullet, but rather has to be used in conjunction with other techniques in the attacker’s toolbox.
Depending on the nature of the zero day vulnerability, it may allow attackers to gain unauthorized access to systems — however, attackers might need to first gain access to the system or network to exploit the vulnerability. The attacker may use social engineering, such as phishing, or other initial-access techniques.
Furthermore, while the successful exploitation of a zero day vulnerability may grant attackers a foothold they might not otherwise achieve, it is crucial to understand that this initial access is rarely the end goal. The initial exploit is often just the first step in a longer attack chain, requiring further actions to achieve objectives like data theft, ransomware deployment, or establishing persistent control.
The subsequent steps — escalating privileges, disabling security systems, moving laterally across systems, communicating with external command-and-control servers, and exfiltrating data — all have one thing in common: they must utilize the network. Every internal connection attempt, every command received, and every byte of stolen data transferred creates network traffic and metadata.
This unavoidable network activity, generated after the initial zero day exploit, presents a critical opportunity for detection and response, highlighting why comprehensive network visibility is indispensable even when facing unknown threats.
How Lumu Detects a Zero Day Attack
The challenge of defending against zero day attacks lies in their very nature: they exploit vulnerabilities unknown to defenders. However, all attacks — even zero day attacks — must use the network to achieve their aims, so this is a critical opportunity for detection.
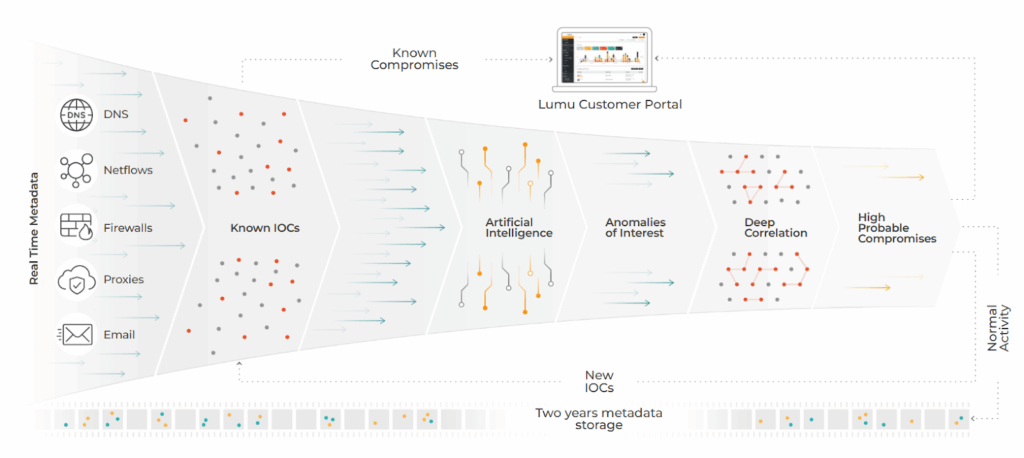
Lumu employs a multi-layered approach called the Illumination Process to discover zero day attacks on your network.
- The Illumination Process begins by ingesting real-time network metadata — including DNS queries, firewall logs, proxy data, NetFlow records, and email traffic — to deliver comprehensive visibility across the organization’s digital environment.
- This metadata is immediately compared against a curated list of verified Indicators of Compromise (IoCs). Any matches are immediately reported as an incident in the Lumu portal.
- Next, Lumu uses AI and machine learning to detect anomalies — deviations from established baseline of normal network behavior. If an attacker is able to infiltrate the network (even if their entry was facilitated by a zero vulnerability) their abnormal network communications will be picked up at this point.
- Unlike other solutions that stop at anomaly detection (often resulting in false positives), Lumu goes further, subjecting all anomalies to an additional layer of deep correlation. Here, anomalies are compared against known confirmed malicious communications. Only if their ‘technical distance’ is considered close enough, are they reported by Lumu as a confirmed compromise.
- Additionally, Lumu’s Playback capability is activated when new IoCs, including zero days, are discovered. This new threat intelligence is compared against two years of stored network metadata, continuously threat-hunting for zero day compromises in your historical data.
Proactive tools that provide visibility into your network, like Lumu Defender, can provide early warnings. Lumu detects anomalies, persistent contacts, Domain Generation Algorithms (DGA), and DNS tunneling, revealing the attack’s progression and potentially preventing a full-scale compromise. Furthermore, Lumu brings the cyberstack under one pane of glass, increasing the probability of suspicious activity being detected.
Zero day attacks often use compromised credentials and social engineering. Lumu Defender alerts your team when there are phishing attempts that might be trying to target employees for a zero attack.
Furthermore, without the Playback capability, described above, we remain blind to potential past malicious action, leaving us unable to fully understand the scope of the attack and take appropriate remediation actions. This historical data is essential for understanding the full lifecycle of a zero day attack, and for preventing future attacks.
How Lumu Helps Preempt & Prepare for a Zero Day Attack
Ideally, you never want to detect a zero day attack as that would mean you’ve already been compromised. For effective defense against zero day attacks it is essential to evaluate your attack surface — in the modern era of cloud computing, the Internet of Things (IoT) and working from home, risks are constantly evolving. Zero day attack prevention is better than detection, once you are already compromised.
Attackers may need to gain access to your system to exploit a zero day vulnerability, so ensuring that your attack surface is minimized is an important defensive measure.
Lumu Discover focuses on preventing the attack from happening in the first place by highlighting two critical areas: leaked credentials and exposed outward-facing assets.
When exploiting a zero day, attackers often need to identify vulnerabilities and exposed assets in your organization, whether servers, open ports, or compromised employees. Lumu Discover helps you understand what information attackers can gather about your organization, and reveals potential points of entry. This proactive approach empowers you to proactively mitigate risks and strengthen defenses
Social engineering is an often overlooked component of a zero day attack, so Discover is an essential tool to help your organization review weaknesses such as compromised accounts. Lumu scans the dark web and other intelligence sources for things like exposed email addresses and employee details.
To see Lumu Discover in action check out this Product Training.
How Lumu Helps After a Zero Day Patch is Applied
Even after a patch has been applied, we cannot sit on our laurels. In effect, if your front door has been wide open for attackers to enter, closing the door means that they won’t get in — but it does not mean there aren’t criminals already inside.
Lumu’s Illumination Process continues to scan for IoCs and suspicious network behaviour. If bad actors have entered your network and look for a later window of opportunity, Lumu stays alert and will catch them as soon as they move. Lumu remains constantly up-to-date with the TTPs associated with new attacks to prepare your security team for an effective response.
Furthermore, Lumu Discover constantly scans the dark web in case any of your information or credentials have been compromised.
No matter which stage of a zero day attack — before, during, or after — Lumu is going to bolster your cyber stack.
Always Expect a Zero Day Attack
While zero day attacks are often depicted as unstoppable hacker ‘silver bullets’ that can foster a sense of helplessness, this narrative overlooks crucial defensive opportunities available to prepared organizations. In reality, proactive measures centered on comprehensive network visibility, robust cyber hygiene, and diligently minimizing your external attack surface significantly diminish the impact of these threats and empower defenders to combat them effectively.
With this in consideration, Lumu offers a three-pronged defence for zero day attack detection and prevention. Lumu Defender unifies your cyber stack to ensure that any detection or IoC is quickly validated, and its Illumination process highlights anomalies in your network usage that can indicate a zero day breach. Lumu Discover preempts zero day attacks by pinpointing potential vulnerabilities within your organization, significantly minimizing the attack opportunities of these unknown threats.
To find out more about how Lumu can defend your organization and to clear up any questions you might have, sign up for a live personalized demo.




