May, 2026
We are excited to announce two new Maltiverse integrations: Microsoft Defender and Splunk Cloud Export. These integrations operationalize high-fidelity threat intelligence by pushing Indicators of Compromise (IoCs) from Maltiverse feeds into your security infrastructure. Automation enables real-time alerting and blocking, keeping your team ahead of evolving threats.
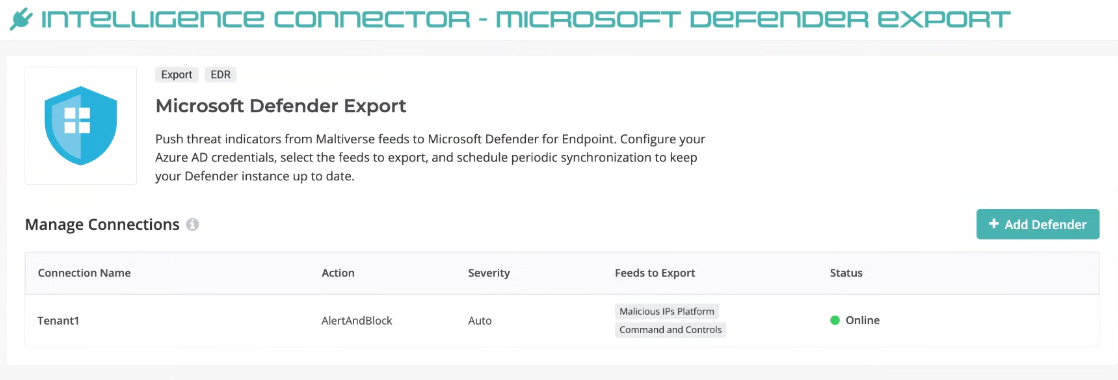
Microsoft Defender Export Integration
The Microsoft Defender integration allows you to seamlessly sync Maltiverse threat feeds with Microsoft Defender for Endpoint. By simply configuring your Azure AD credentials and selecting the feeds relevant to your organization, you can schedule periodic synchronizations to keep your Defender instance up to date. This integration empowers your SOC to trigger automated responses and blocking actions for malicious IPs, hostnames, and URLs directly at the endpoint level.
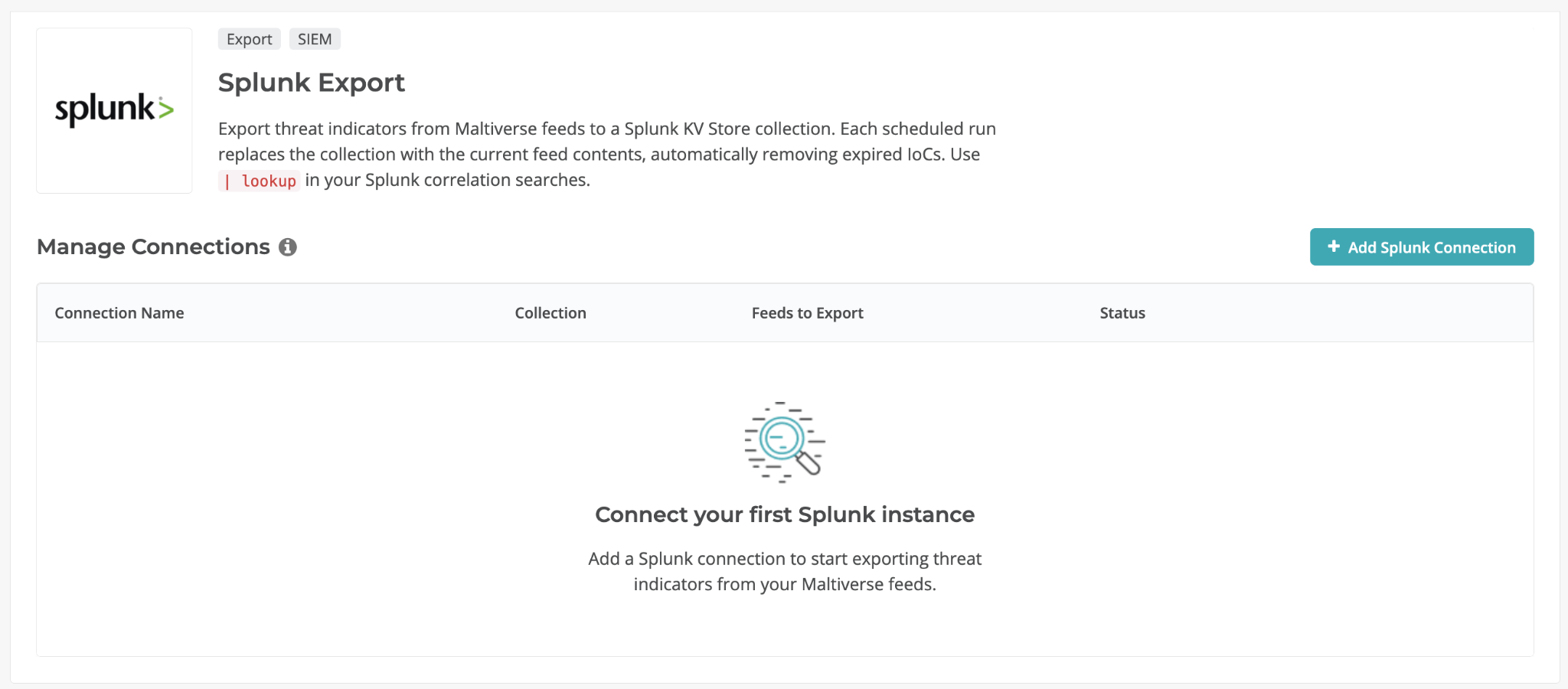
Splunk Cloud Export Integration
The Splunk Export integration is the ideal solution for operationalizing Maltiverse intelligence in any Splunk environment (including Splunk Core, Cloud, or Free) without the need for an Enterprise Security (ES) license. This full-sync integration automatically populates a standard KV Store collection with the latest IoCs, allowing you to enrich events and drive correlation searches using a simple lookup command. Because it runs on an hourly schedule and automatically removes expired indicators, you can maintain high-confidence block-lists without the manual burden of cleaning up stale data.