Product Updates
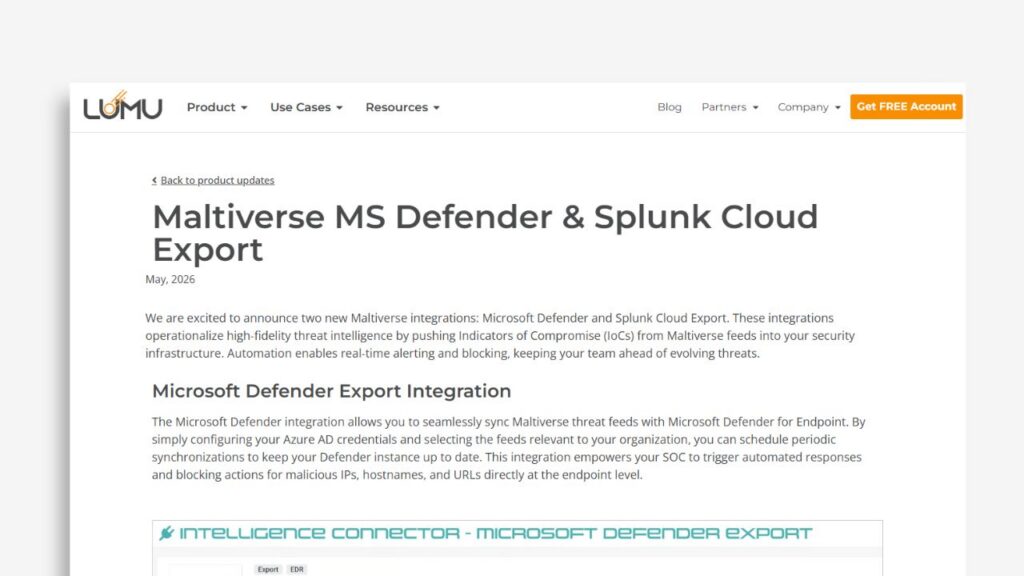
Maltiverse MS Defender & Splunk Cloud Export
Learn how Maltiverse integrates with Microsoft Defender for Endpoint and Splunk Cloud to operationalize threat intelligence through automated IoC ingestion. This update enables security teams to trigger real-time blocking actions, enrich events, and maintain high-confidence detection workflows without manual data handling or complex integrations.
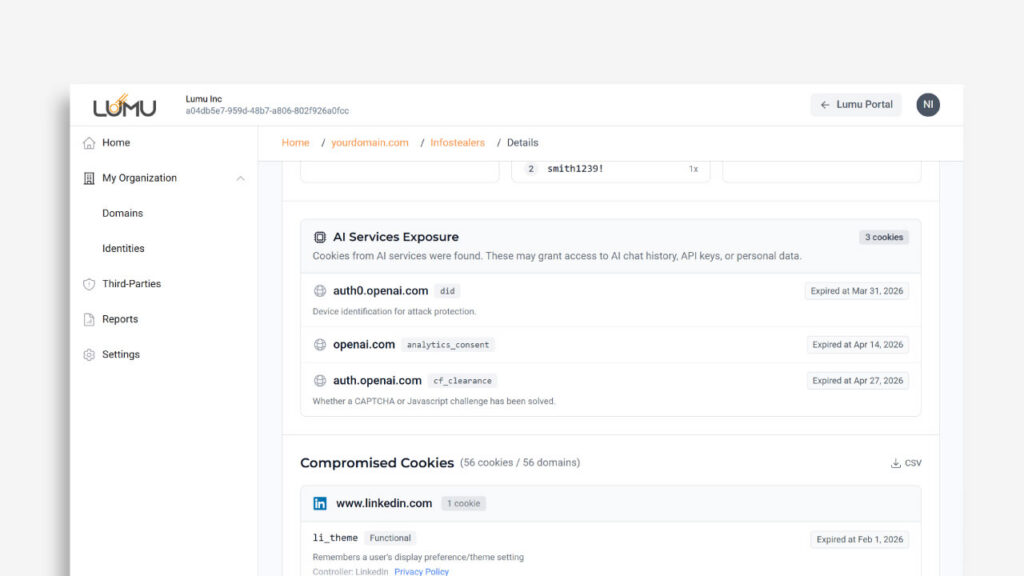
AI Services Exposure
While password theft is a major threat, modern attackers rely heavily on session cookies and system-level persistence to bypass security controls. We’ve enhanced Lumu Discover to give you full visibility into Infostealers-related incidents, with one of the biggest additions being the AI Services Exposure section.
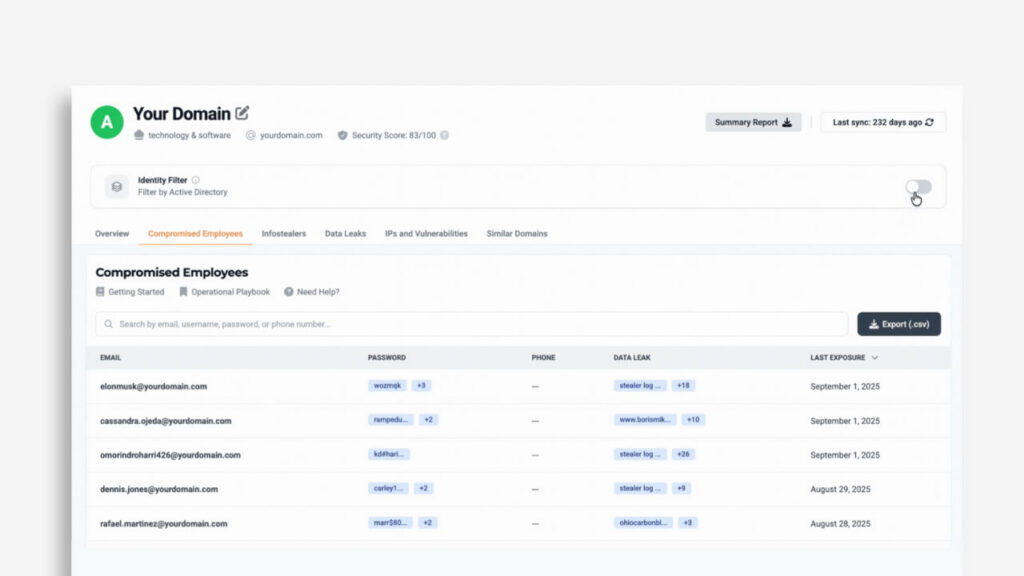
Lumu Discover: Active-Employee Threat Filtering
Eliminate dark web noise by correlating external leaks with your active employees to identify critical security gaps like disabled MFA or unauthorized email forwarding.

Lumu Defender Integration with Power BI
Learn how to integrate Lumu Defender with Microsoft Power BI to create executive-ready cybersecurity dashboards. This guide explains how to transform threat intelligence data into actionable insights, track key metrics like MTTR and incident closure rates, and demonstrate operational ROI using a ready-to-use template—without complex API scripting or manual data exports.
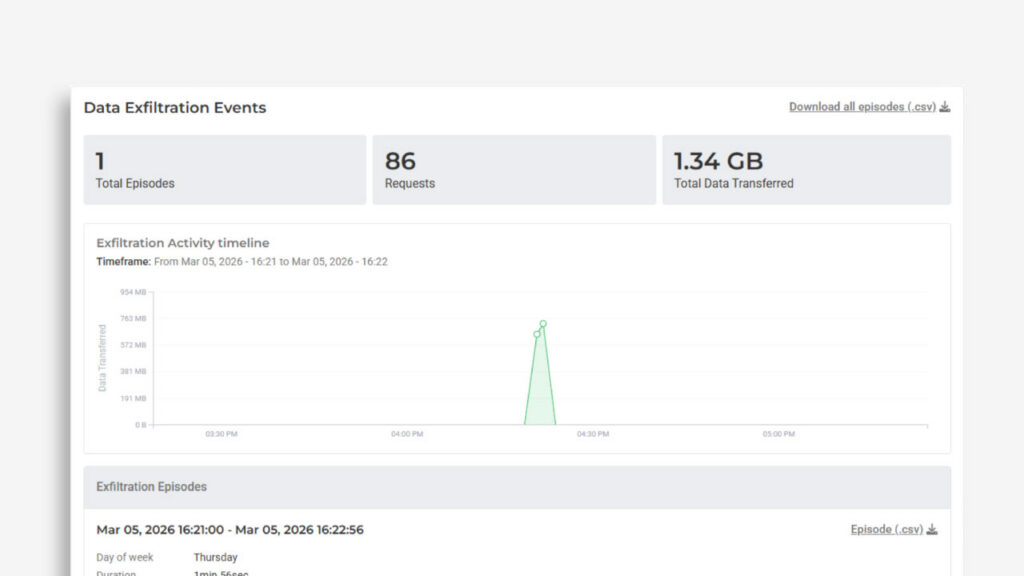
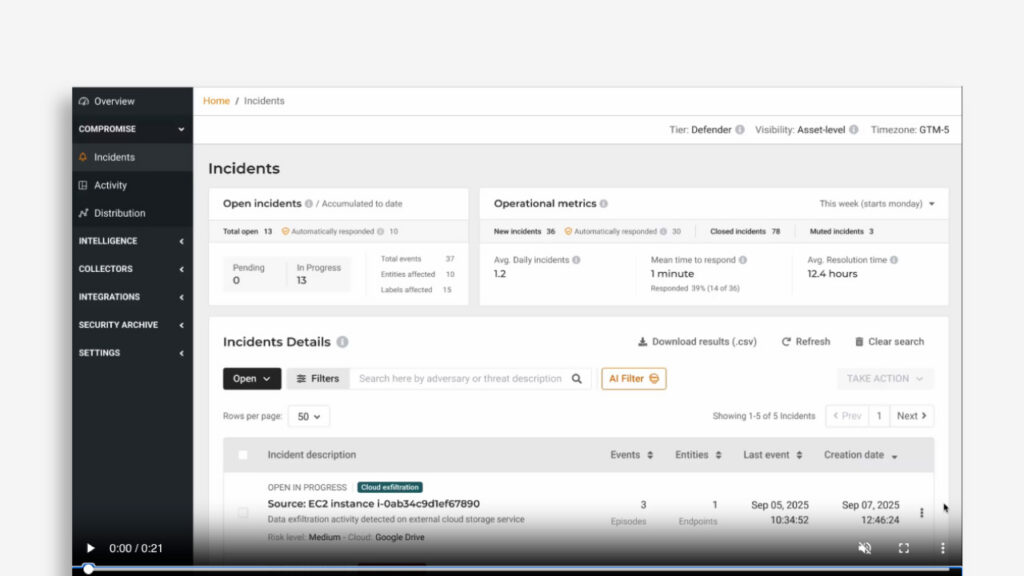
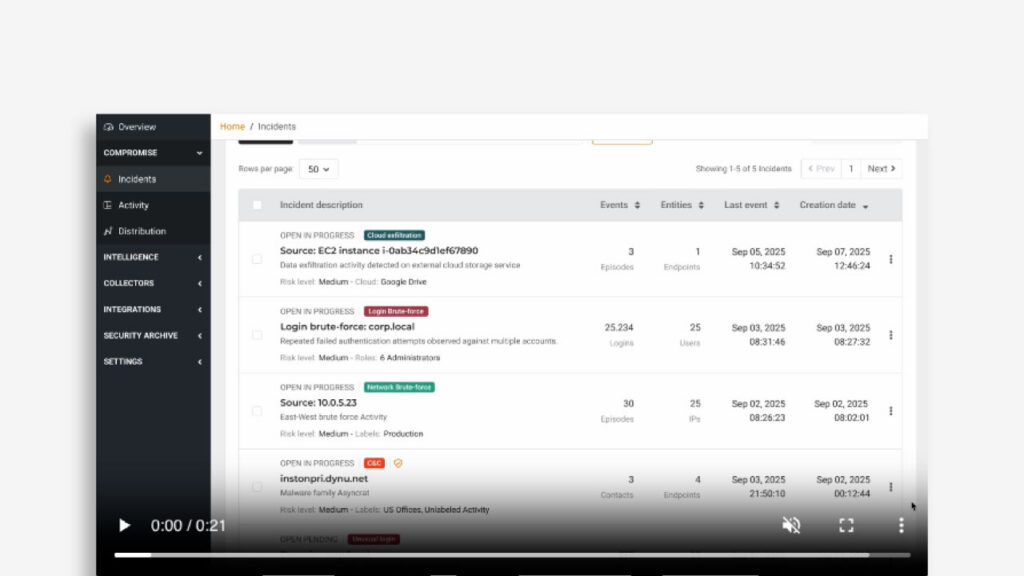
Data Exfiltration Incidents
Ransomware groups have shifted to double extortion, often stealing sensitive data before a single file is ever encrypted.
Most modern attacks are “Living off the Land,” using legitimate tools like Rclone or Mega to move data. These connections often bypass traditional security rules because they look like normal cloud traffic.
Lumu AI
We are excited to announce that we are making Lumu AI a standard feature, available to every Lumu Defender customer, not as a luxury add-on. Lumu AI instantly transforms complex network telemetry into high-fidelity, actionable intelligence to bridge the response gap and accelerate your Mean Time to Understand (MTTU).
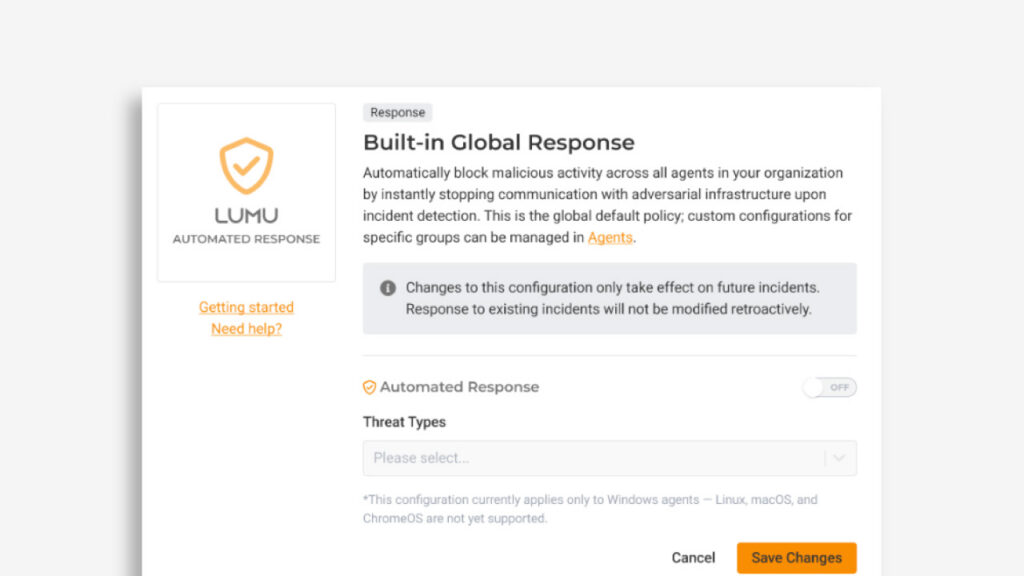
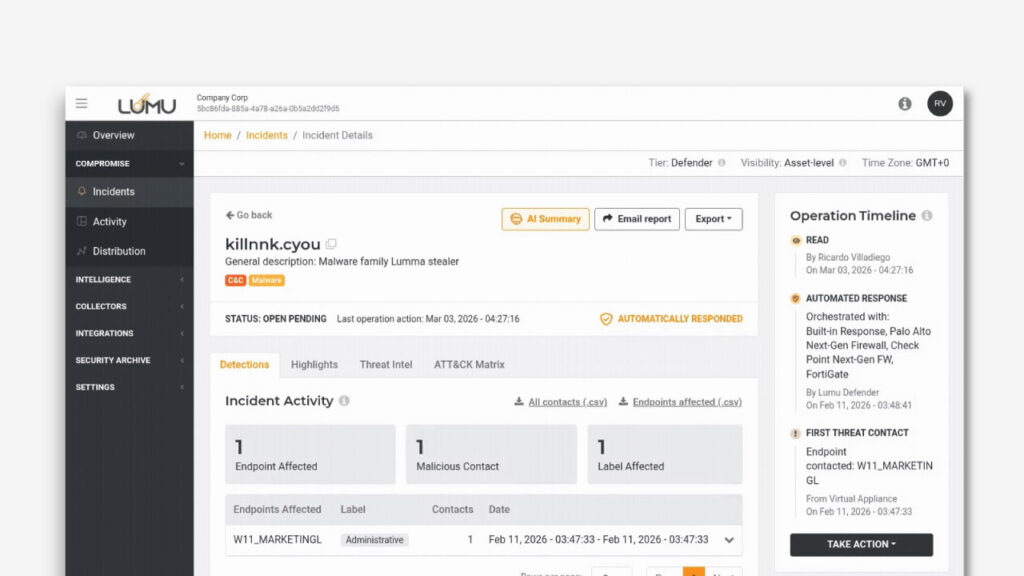
Lumu Agent with Built-in Response
The Lumu Agent now includes built-in automated response capabilities, expanding its role beyond data collection to enable direct action when threats are detected.
New Incidents Related to Anomalous User Behavior
Account takeover is one of the most common compromise paths, often achieved through phishing, info-stealers, or password reuse. Because attackers use valid credentials, they easily bypass traditional controls.
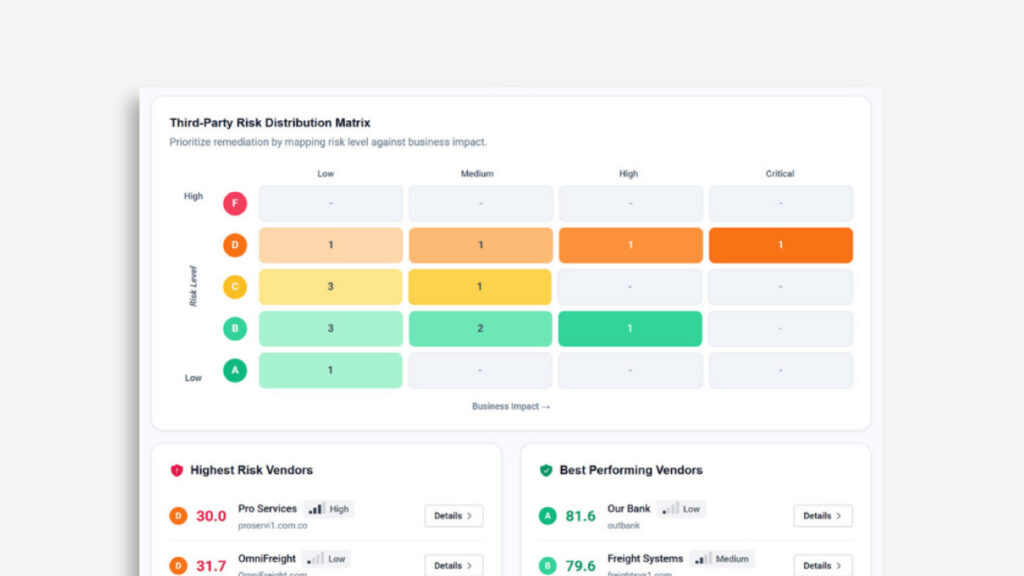
Lumu Discover: 3rd Party Ecosystem Risk
Lumu Discover now includes 3rd party risk assessment, giving you a complete picture of cybersecurity risks across your entire software ecosystem, including your technology vendors.
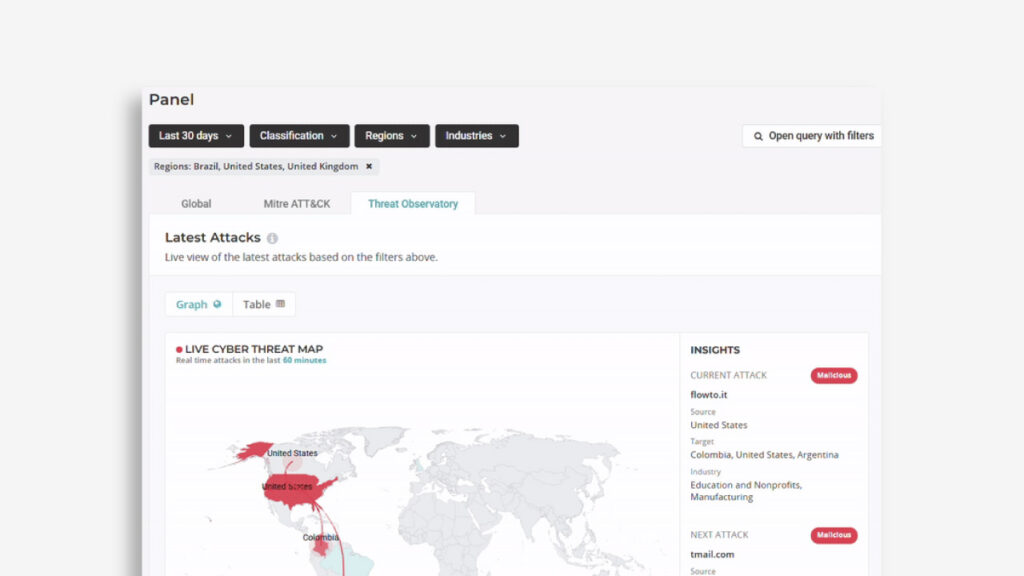
Maltiverse Threat Observatory
When global cyber threats feel like constant noise, the real question isn’t just what the threat is, but whether it’s actually targeting your industry, region, or peers.
The Next Generation of Continuous Compromise Assessment®
Since its inception, Lumu has built Continuous Compromise Assessment as the foundation of how organizations detect and respond to threats, and it has served as the backbone of how thousands of security teams operate cybersecurity on a daily basis.

Product Recap 2025
This year began with the launch of the Lumu SecOps Platform. Organizations no longer want vendor lock-in. They demand interoperability, open architectures, and the
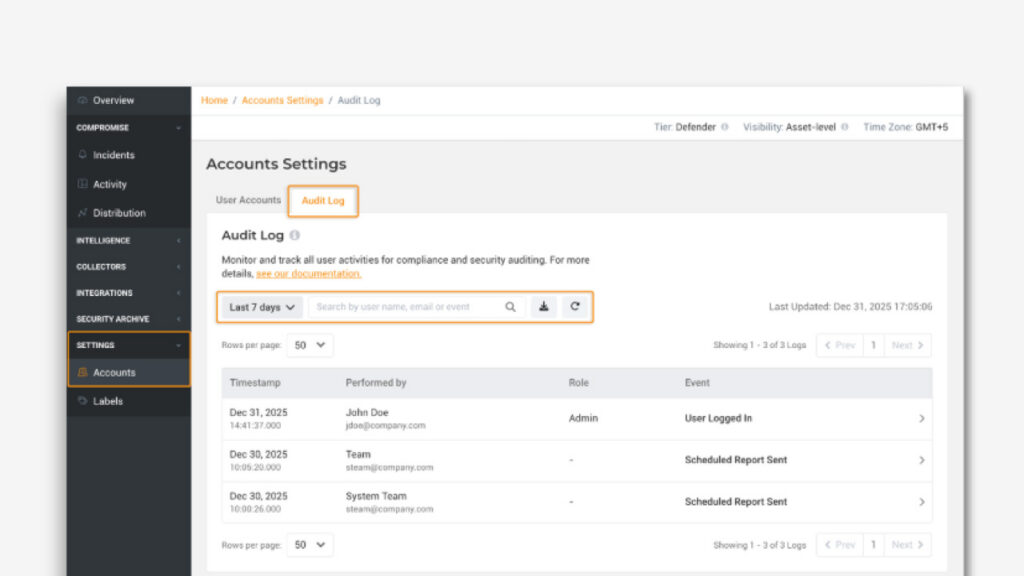
Lumu Portal Audit Logs
Audit Logs give your team a clear, auditable record of what’s happening inside the Lumu Portal.
