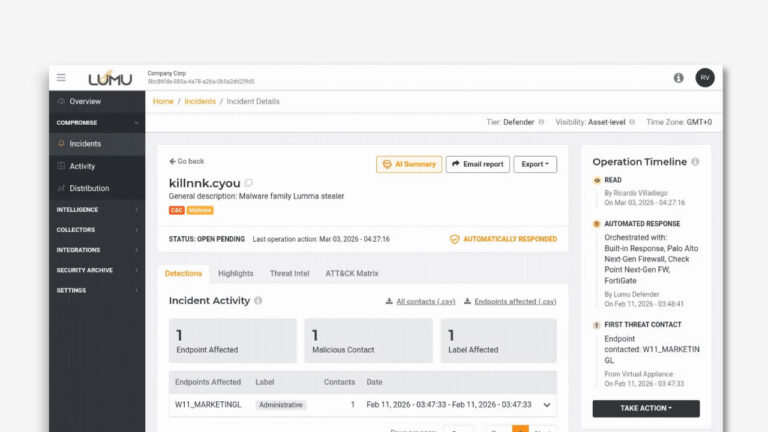
Since its inception, Lumu has built Continuous Compromise Assessment as the foundation of how organizations detect and respond to threats, and it has served as the backbone of how thousands of security teams operate cybersecurity on a daily basis. Now, it is entering a new stage of evolution and becoming its most powerful form yet. Detections will expand to cover identities, cloud deployments, and endpoints, Lumu will deliver unprecedented visibility and richer context than ever before.
This isn’t just an evolution of our Continuous Compromise Assessment but a leap forward in how modern cybersecurity operates.
What’s Coming
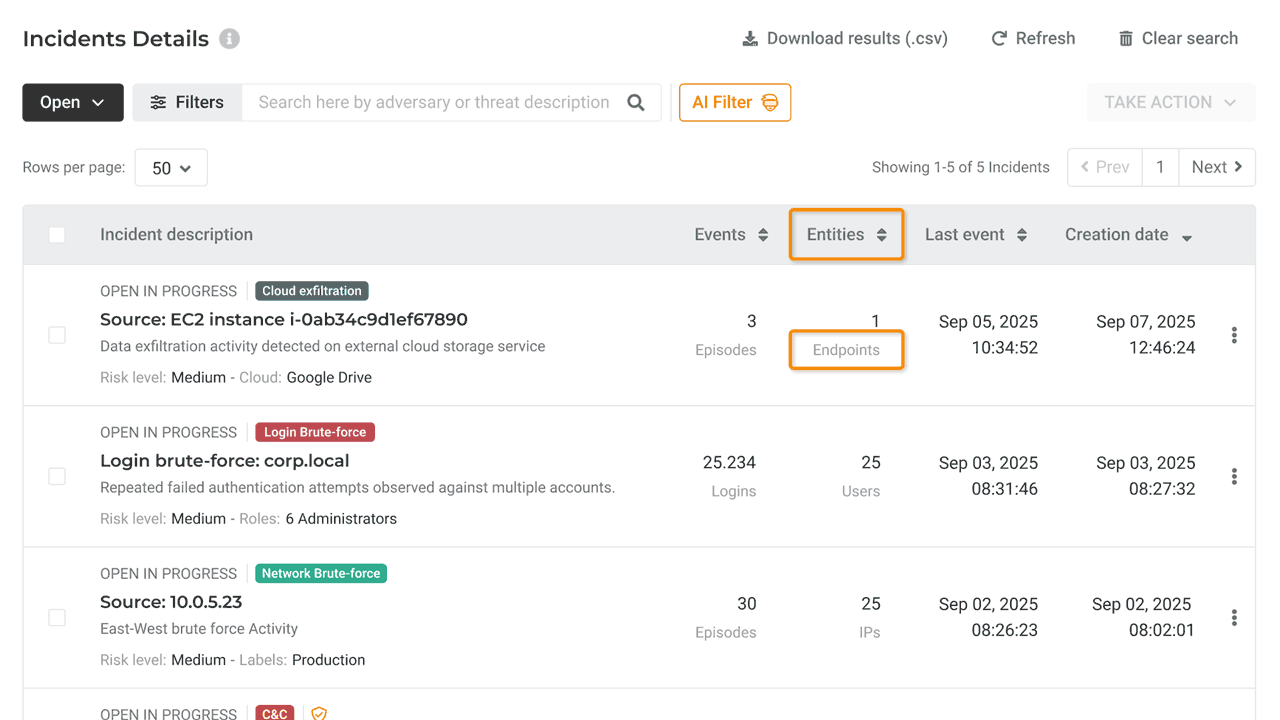
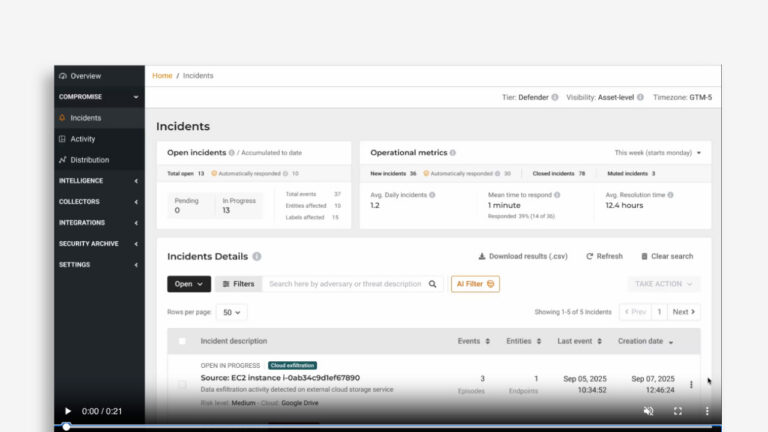
As part of this evolution, you may have noticed your Incident View has been slightly updated to reflect what’s there now and what’s coming in the near future. In the coming weeks and months, you’ll begin to see new incident types along with other related updates, including new detections and expanded capabilities directly in your Lumu portal.
Here is a look at what you can expect:
User Anomalies
Unusual Login Incidents
Account takeover is one of the most common compromise paths, often achieved through phishing, info-stealers, or password reuse. Because attackers use valid credentials, they easily bypass traditional controls. This detection profiles normal login patterns of admin accounts and highlights anomalies like unexpected times or frequencies, providing security teams with early visibility into compromised accounts before privilege escalation or lateral movement occurs.
Login Brute Force
Brute force and password spraying are common attacker techniques to gain unauthorized access by repeatedly guessing credentials. This detection surfaces abnormal login failures and probing activity, providing security teams with clear visibility into account-targeting attacks and the ability to stop intrusions before valid access is achieved.
East-West Visibility
Network Brute Force
Attackers preparing lateral movement often probe or misuse common internal services to test credentials or exploit targets. This detection highlights abnormal surges in access attempts, revealing brute-force and enumeration activity early. It gives security teams timely east–west visibility to contain compromise and detect attackers.
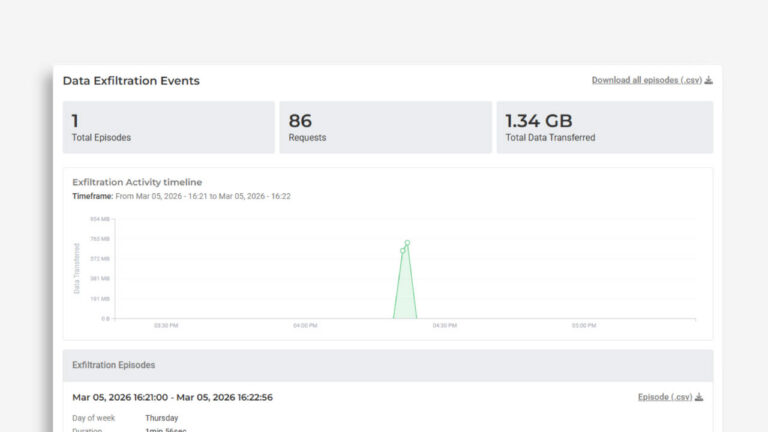
Exfiltration
Exfiltration through Cloud Providers
Attackers often use cloud storage providers to send data out under the cover of normal SaaS traffic. This detection distinguishes routine collaboration from suspicious transfers, unusual destinations, volumes, timing, or accounts, giving security teams early, actionable visibility to stop data theft and investigate insider risk or compromised identities before damage escalates.
DNS Tunneling
Attackers hide command-and-control and data exfiltration inside routine DNS activity to evade traditional controls. This detection spots DNS patterns that don’t fit normal usage, revealing covert channels early so security teams can cut off communications, contain compromised hosts, and act before the attack progresses.
Updated Terminology to reflect the broader scope of Continuous Compromise Assessment and what’s being tracked.
- Contacts are now called Events
- Endpoints are now Entities
Also Coming Soon
As part of our ongoing advances in detecting compromises holistically, Lumu will roll out additional threat detections that are clear precursors of compromise and security control evasion. This is what you can expect in the coming months:
OS Event Logging Manipulation
Attackers often try to blind defenses and cover their trail by disabling or tampering with system logging. This detection flags attempts to suppress auditing, a very usual sign of active intrusion SIEM or XDR.
Volume Shadow Copy Deletion
Ransomware often deletes system backups to make recovery harder and guarantee impact. Detecting backup destruction attempts gives responders critical visibility to react faster against ransomware or destructive attacks.
Early Ransomware Alerts
An early-warning for ransomware. When files start getting encrypted or destroyed, this detection alerts quickly so you can act on affected assets and contain the spread to mitigate impact.
Suspicious Account Activity
Detect anomalous admin creation, abrupt privilege removals, and short-lived accounts to expose backdoors, disruption attempts, and covert access.
Possible Directory Service Enumeration
Attackers often list users, groups, and machines to plan their next moves. This detection catches that reconnaissance early so you can harden targets and interrupt the attack.
Potentially Unwanted Applications
Some tools aren’t malware but are commonly used by attackers. Such dual-use tools (remote access, password utilities, LOLBins) often serve as an attacker’s starter kit. This detection surfaces those risky apps so you can remove them and reduce exposure.
It Gets Even Better
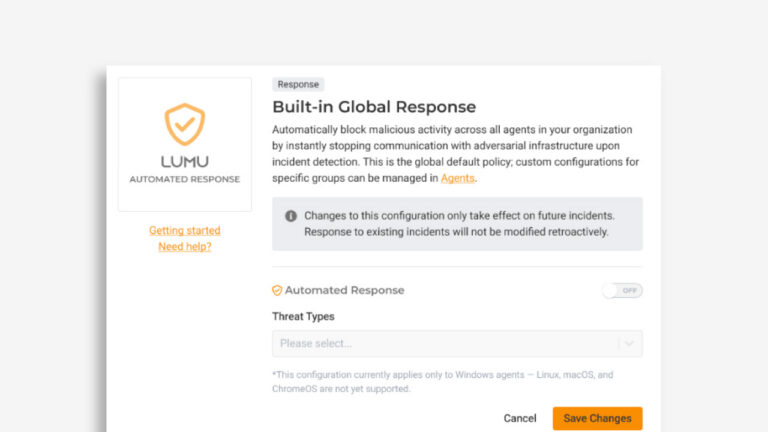
For active customers, these new powerful capabilities are included as part of your Lumu Defender subscription.
By unifying detections from the network, identity, and endpoints into the Continuous Compromise Assessment model, we are delivering actionable visibility across the elements adversaries exploit most. This is only the beginning of a future where security operations become smarter, faster, and more unified than ever before.