March, 2026
Ransomware groups have shifted to double extortion, often stealing sensitive data before a single file is ever encrypted.
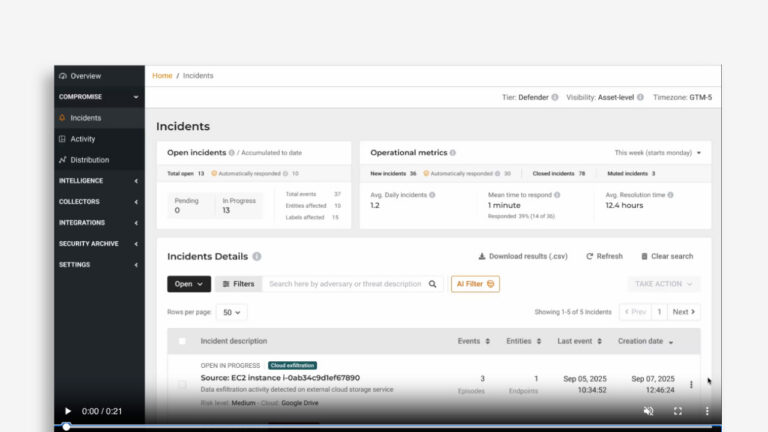
Most modern attacks are “Living off the Land,” using legitimate tools like Rclone or Mega to move data. These connections often bypass traditional security rules because they look like normal cloud traffic. Lumu bridges this gap by identifying suspicious high-volume transfers to external storage services,even when legitimate providers are used.
How Data Exfiltration Detection Protects You:
- API-Level Anomalies: Lumu detects when communication shifts from simple browsing to direct interaction with cloud storage APIs.
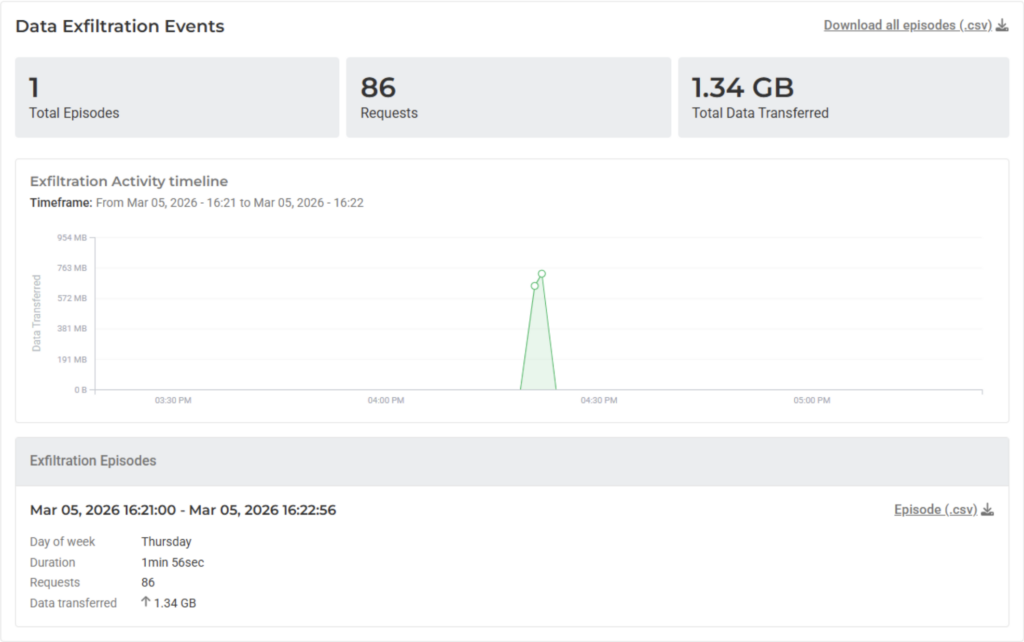
- Outbound Traffic Peaks: We monitor for high-volume flows that deviate from your organization’s unique behavioral baseline.
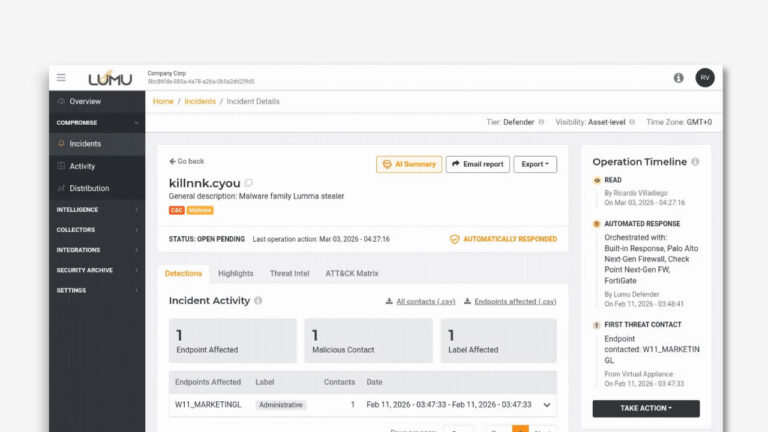
Illuminating Late-Stage Attacks: By correlating exfiltration with previous alerts (like Phishing or Malware), Lumu identifies the final stage of an attack before your data is fully compromised.
To learn more, please visit our Data Exfiltration Response Playbook. We encourage you to log into the Lumu Portal today to explore these new detections.