Already have an account? Sign in
Sign in


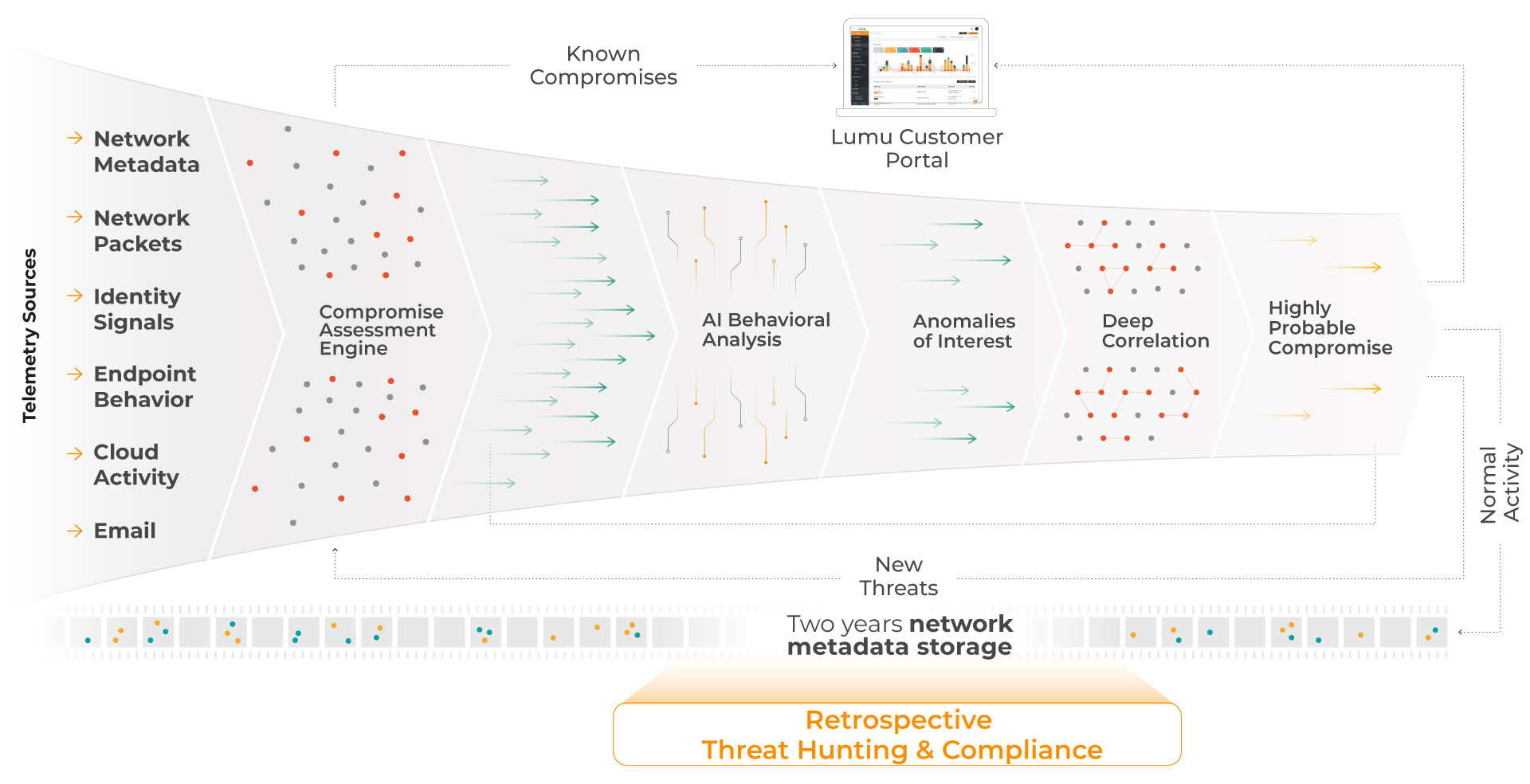
Lumu collects and analyzes telemetry sources to see your entire environment.
Telemetry is correlated against known threat data curated from across public and private sources and combined with our proprietary Maltiverse intelligence platform.
Known compromise is immediately reported and a Lumu incident is created.
Newly identified threats are added to the list of known compromises.
Multi-stage AI detects anomalies and measures them against known threat data to confirm compromises and reduce false positives.
After analysis, highly probable compromise is reported as a new Lumu incident.
Remaining "normal" metadata is saved for 2 years for retrospective analysis.
Lumu continuously measures compromise by analyzing security signals in real time. That assessment feeds a closed-loop model that validates defenses and contains threats early, so decisions are based on confirmed compromise.