Already have an account? Sign in
Sign in
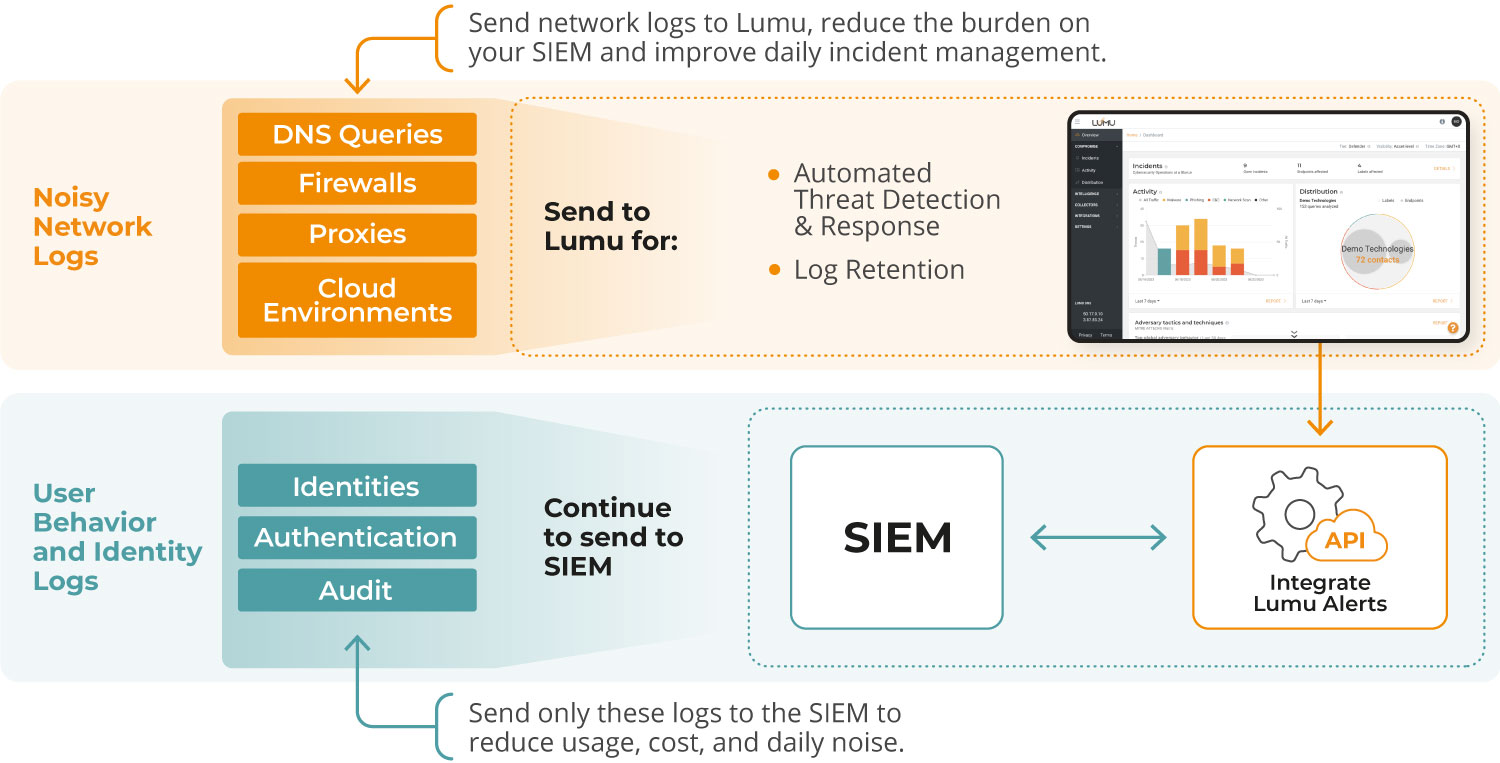
Storing logs for compliance and threat hunting can be costly and chaotic, with disjointed data and pricey SIEMs leaving your team struggling.
Lumu Archive makes it easy to search, analyze, and act on stored network data whenever you need it.
An optimized approach to retaining noisy network logs, like DNS, firewall, proxies, and cloud data for up to two years.
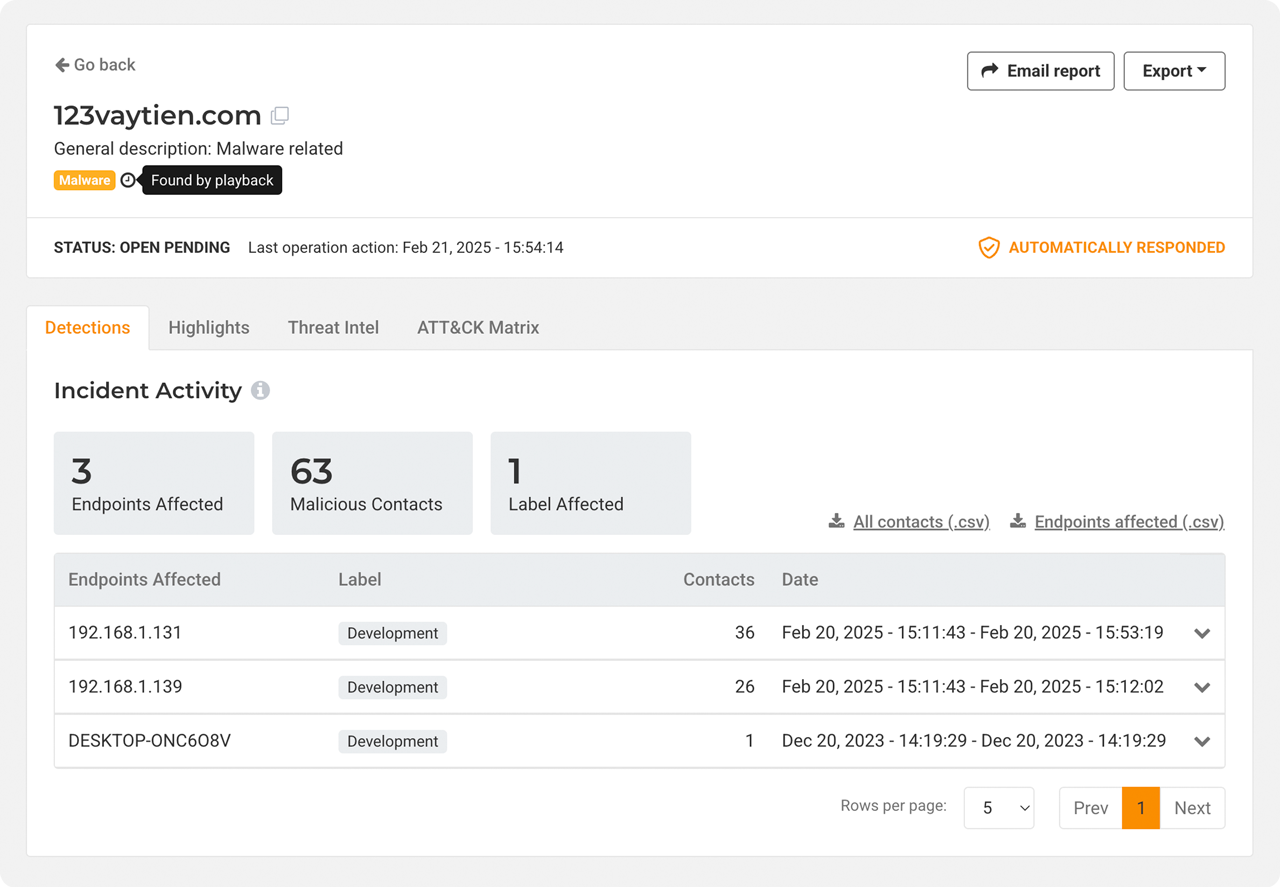
Continuous retrospective threat hunting for detecting zero-day and newly discovered attacks that might have gone unnoticed in the past.
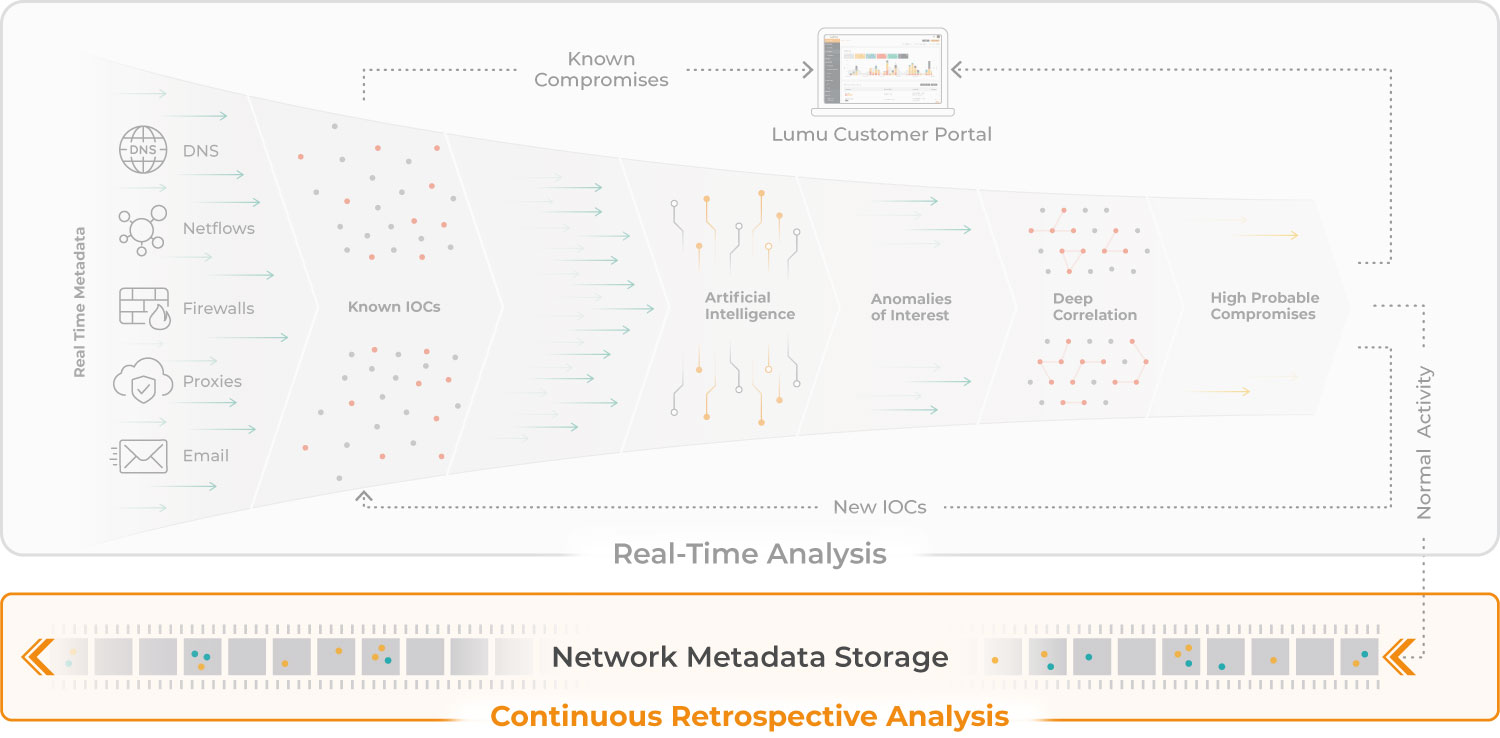
Lumu Defender analyzes live network metadata, instantly detecting and responding to network threats. Archive then retrospectively applies new threat intelligence, including IoCs and Zero-Day discoveries, to your historical logs, revealing previously undetected compromises.
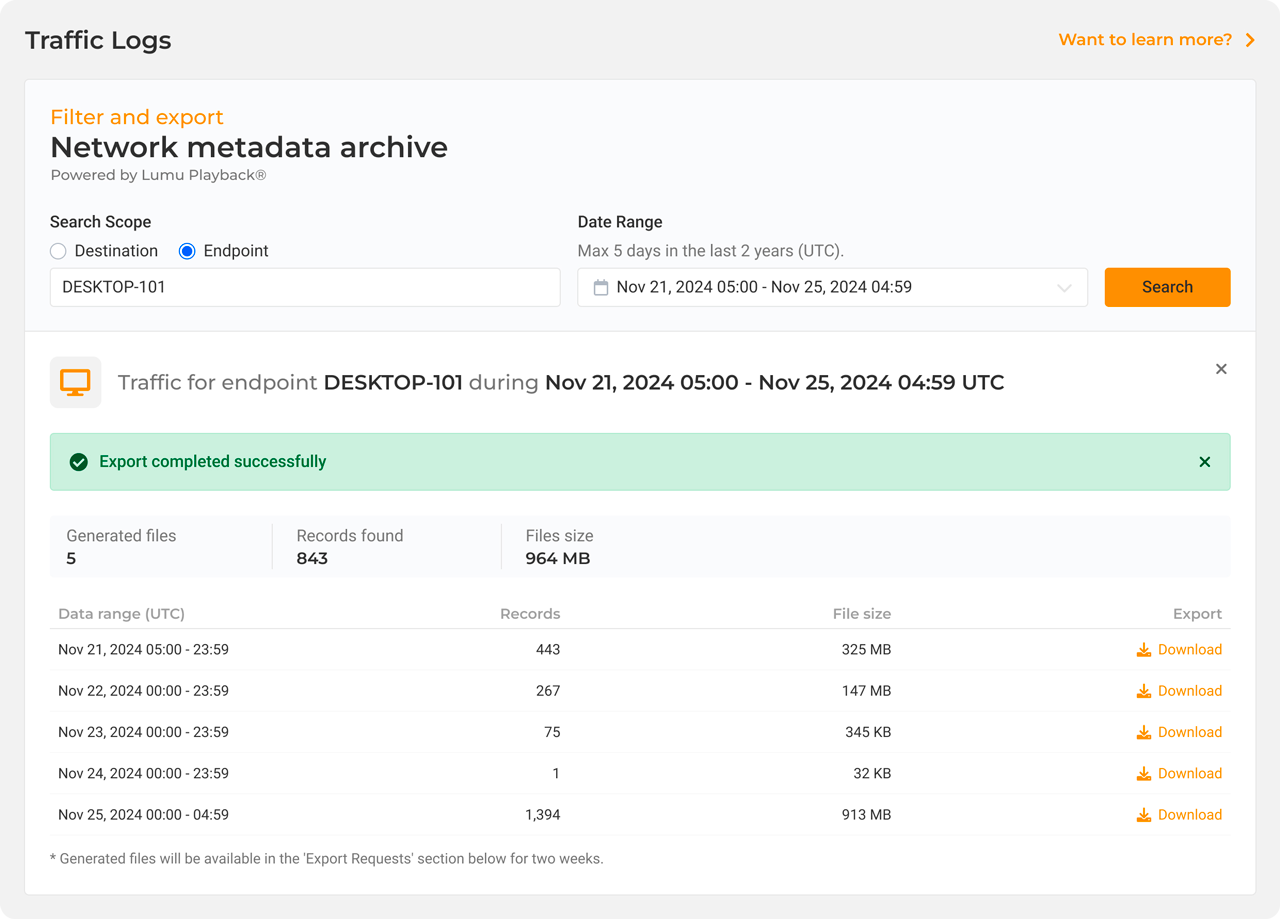
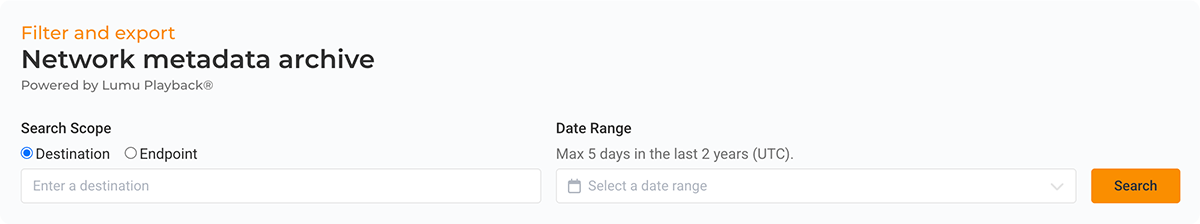
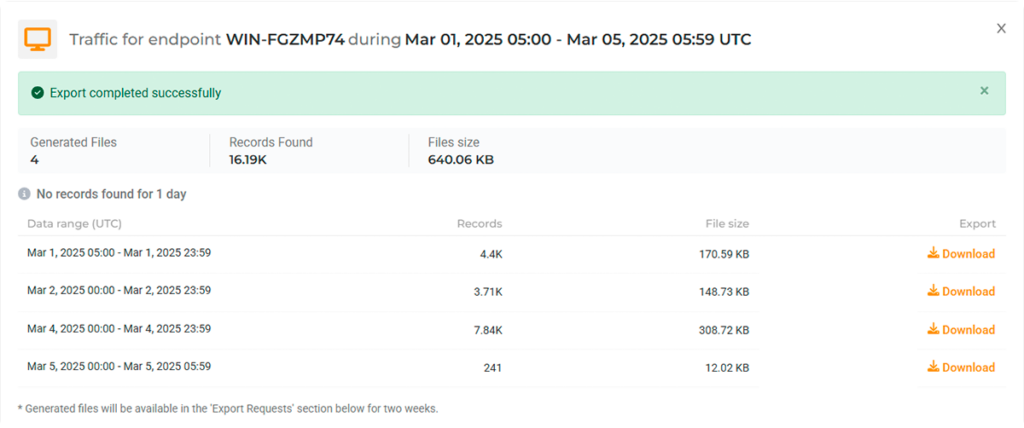
Self-service log access: unlimited, instant querying and downloading of your network logs, to support your security needs.

The Playback feature continuously reanalyzes two years of network traffic logs to identify previously unknown threats with the latest threat intelligence.

Maintain compliance and support investigations with up to 2 years of log storage.

Ensures compliance with network log storage requirements under a variety of frameworks.

Your logs are always available. Query and analyze them anytime right from the Lumu portal to accelerate forensic investigations and incident response.

Offload your network logs to Lumu, eliminate the need to store duplicates, and save up to 75% of EPS costs.

Quickly query historical data to pinpoint the source and scope of attacks, accelerating incident response and minimizing damage.
Connect with an expert to learn more about Lumu Archive