Already have an account? Sign in
Sign in
K–12 Schools face unique threats and challenges. Lumu helps you protect student data and network infrastructure.
While these tools are essential components of a cybersecurity stack, they have their shortcomings and are known to be easy targets for cyber criminals.
Cybercriminals target schools because student data is valuable. They know that traditional defenses can be bypassed and that small teams oversee networks the size of big enterprises.
Lumu gives K–12 full network visibility and empowers them to detect and respond to threats in real time. Aligned with the NIST cybersecurity framework, Lumu helps optimize security operations.
Report
Schools are now the primary objective for cybercrime in the USA. Attackers are taking advantage of the chaos of student traffic to get into your network.
Blog
Summer break is a high-risk period in cybersecurity for schools. Discover practical cybersecurity solutions for how to secure school networks over the summer.
Videos
Securing sensitive student data is a top priority at Uinta County School District. Hear from Technology and Facilities Director, Jaraun Dennis, as he shares how Lumu has played a pivotal role in the school district’s cybersecurity strategy.
Attacks
Cybercrime in the education sector is having a field day while educational institutions are suffering at the hands of cybercriminals. We look at some of the stats and reasons behind this worrying trend.

Nashville, TN

Information Systems Director
“Think of a security stack as a stack of Swiss cheese pieces: each piece provides defense, but each one of those layers has holes in it. If a threat gets through, Lumu catches that.”
Watch Interview
Evanston, WY

Technology and Facilities Director
“It paired really nicely with our Checkpoint firewall and our CrowdStrike. That interoperability oftentimes doesn’t happen. And so Lumu really makes these other tools that we were using better.”
Watch Interview
Pinedale, WY

Director of information Services
“Even though we had our security stack in place, those solutions had some gaps. [When we installed Lumu we were seeing some command and control and malware on the servers.”
Watch Interview
Nashville, TN

Information Systems Director
“Think of a security stack as a stack of Swiss cheese pieces: each piece provides defense, but each one of those layers has holes in it. If a threat gets through, Lumu catches that.”
Watch Interview
Evanston, WY

Technology and Facilities Director
“It paired really nicely with our Checkpoint firewall and our CrowdStrike. That interoperability oftentimes doesn’t happen. And so Lumu really makes these other tools that we were using better.”
Watch Interview
Pinedale, WY

Director of information Services
“Even though we had our security stack in place, those solutions had some gaps. [When we installed Lumu we were seeing some command and control and malware on the servers.”
Watch InterviewTake a look at how Lumu works.
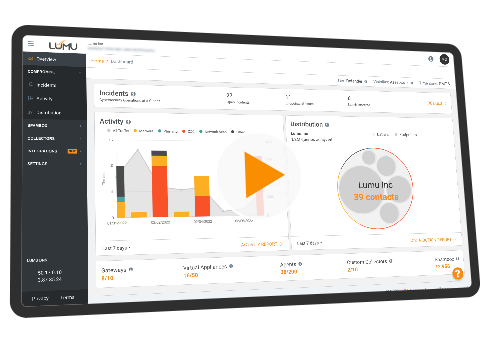
Want to go even deeper?
Sign up for a live product demo.