- Technical Report
CISA Exposes How 12 Ransomware Gangs Are Bypassing EDRs
Take a deep dive into the techniques that attackers are actively using to disable endpoint defenses.
Get Your Copy of the Report to Learn About:
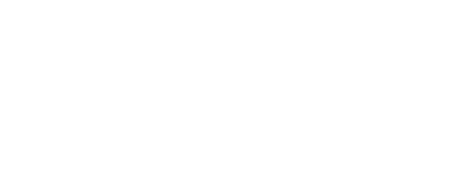
- How 12 real-world ransomware gangs consistently bypass Endpoint Detection and Response (EDR) tools.
- EDR evasion techniques that are most commonly used by attackers.
- The specific tactics and techniques that attackers exploit to disable endpoint defenses.
- How network visibility closes the gaps and helps detect threats missed by traditional defenses.
- Why the traditional security model of firewall, EDR, and email filtering is no longer enough to stop modern ransomware attacks.
Our Highlights
“Each of the 12 ransomware gangs analyzed in this report successfully evaded EDR tools using at least two different techniques. It's no longer a question of if attackers can bypass EDR—it’s a matter of when.”
“Many organizations are still building their cybersecurity posture around a traditional triad of firewall, EDR, and email security—this report shows why that model is no longer sufficient.”
“The report reveals that attackers are not just disabling EDRs—they’re leveraging trusted tools, stolen credentials, and system-level tactics that leave defenders blind unless deeper visibility is in place.”
Get the Report
By clicking “Get Report Now” you agree to the Lumu Terms of Service and Privacy Policy.