
The New and Improved Lumu Free
Reading Time: 3 mins Lumu Free just got a major upgrade. We’ve included more metadata collectors, giving you greater network visibility and more closely reflecting our vision of how cybersecurity needs to be operated.
Already have an account? Sign in
Sign in
Get the latest cybersecurity articles and insights straight from the experts.

Reading Time: 3 mins Lumu Free just got a major upgrade. We’ve included more metadata collectors, giving you greater network visibility and more closely reflecting our vision of how cybersecurity needs to be operated.

Reading Time: 3 mins MSPs’ skills and resources make them perfectly positioned to fulfill SMBs’ need for increased cybersecurity resilience.
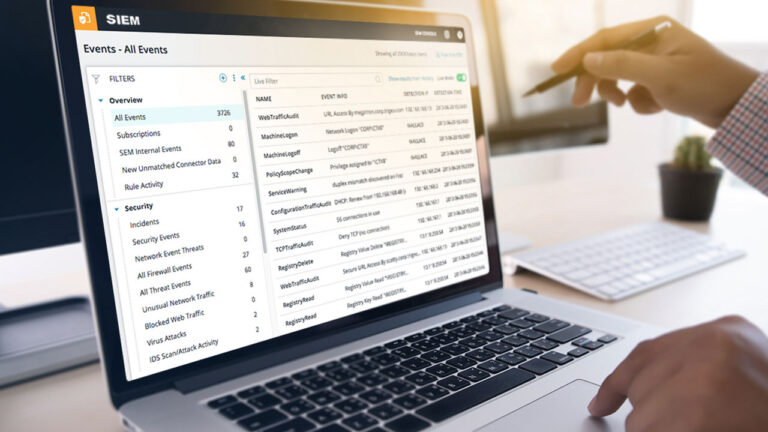
Reading Time: 4 mins Veteran Cybersecurity Operator at Lumu Andrés Argüelles looks at using Lumu with your SIEM to get the most out of both platforms.

Reading Time: 3 mins Lumu Defender lets you feed Lumu’s confirmed compromise instances into your existing cybersecurity stack for an automated response to cyber threats.

Reading Time: 2 mins In this Lumu Insights review, eWeek declares that Lumu makes ‘fighting cyber threats with actionable intelligence a work of IT art.’

Reading Time: 2 mins Lumu Academy offers free cybersecurity courses on Lumu products. Get Lumu certification through our self-paced virtual courses.

Reading Time: 2 mins Lumu’s New Experience is a game-changer. ‘Incidents’ groups related contacts and improves reporting for reduced alert fatigue and much more.

Reading Time: 2 mins Lumu’s new custom collector allows seamless network metadata collection from third-party tools for better, faster compromise assessment.

Reading Time: 4 mins Are security budgets spent on solutions that actually matter? Guest blogger Chris Steffen looks at addressing this concern with the automated ATT&CK Matrix.

Reading Time: 3 mins The powerful MITRE ATT&CK Matrix is now integrated into the Lumu Portal, making it possible to see relevant TTPs for all detected compromises.

Reading Time: 3 mins As security professionals, we hear about mitigation and remediation on a daily basis. However, these are terms that are commonly confused with each other.

Reading Time: 4 mins Security operations teams are increasingly inundated with alerts. Take a look at how Lumu can make your SOC more efficient in 3 easy steps.

Reading Time: 2 mins According to Gartner, 88% of organizations worldwide made it mandatory or encouraged their employees to work from home due to the global pandemic situation.
Reading Time: 5 mins Ransomware attacks have been increasing in frequency; we look at some examples like Sodinokibi, WannaCry, and MAZE, and how Lumu detects them.

Reading Time: 3 mins Analyzing spam metadata lets Lumu’s portal present insights on which users are being targeted and how your company is being compromised.
© Lumu Technologies All rights reserved. | Legal information.